Integrate instantly with your existing setup, remove manual tasks, and let ISMS.online do the work for you.
Book a demoLeverage the benefits of automating compliance by integrating ISMS.online with your tech stack and enable ongoing monitoring of controls and gathering of evidence.
Integrating ISMS.online with your dedicated HR platform lets you keep track of all personnel within your organisation.
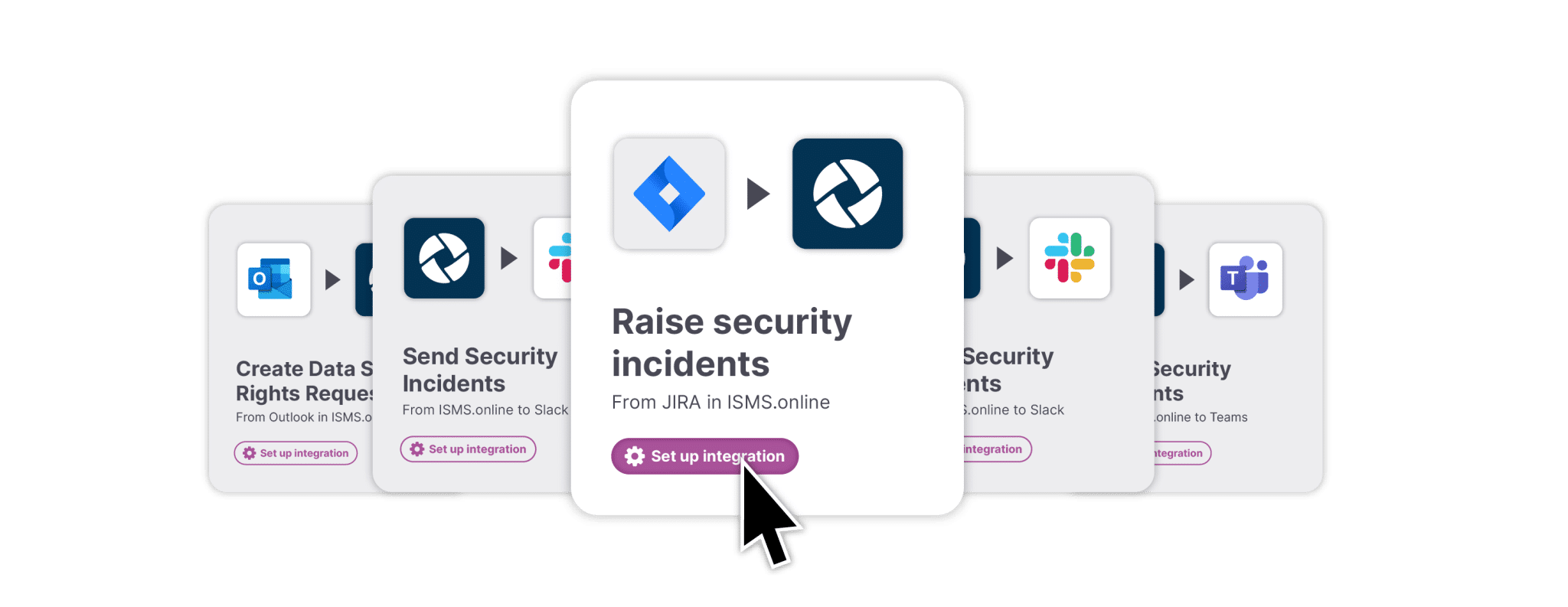
Raise security incidents within your ticketing system and have them automatically populate within your ISMS for streamlined management.
Report security incidents through your task management platform for automatic integration into your ISMS Security Incident Management track.
Use our SSO integration to sign in securely with your Azure AD, Google and Okta accounts and more. Our implementation also supports any SAML2 SSO provider.
Single Sign-on
Single Sign-on
Single Sign-on
Single Sign-on
We need the contact information you provide to us to contact you (via email and/or telephone) about our products and services. You may unsubscribe from these communications at any time. For more information please check our Privacy Policy.
Effortlessly address threats & opportunities and dynamically report on performance
Easily collaborate, create and show you are on top of your documentation at all times
Out of the box integrations with your other key business systems to simplify your compliance
Shine a light on critical relationships and elegantly link areas such as assets, risks, controls and suppliers
Engage staff, suppliers and others with dynamic end-to-end compliance at all times
Manage due diligence, contracts, contacts and relationships over their lifecycle
Make light work of corrective actions, improvements, audits and management reviews
Visually map and manage interested parties to ensure their needs are clearly addressed
Make better decisions and show you are in control with dashboards, KPIs and related reporting