Last week CSO Online reported yet another security breach, this time on the other side of the pond. An estimated 320,000 Time Warner Cable residential customers, using Time Warner as their ISP, had their email credentials stolen.
Hacked email accounts are frustrating but maybe we underestimate the dangers in having our email address and password stolen.
A recent article in V3 discussed the rise of cybercrime-as-a-service. “underground marketplaces are structured by analysing the price and availability of stolen credit and debit card details, banking credentials, personal identity information and even media subscription log-ins”. It revealed that UK bank details are sold for as little as £12 on the dark web.
But what would a criminal do with your email address and password?
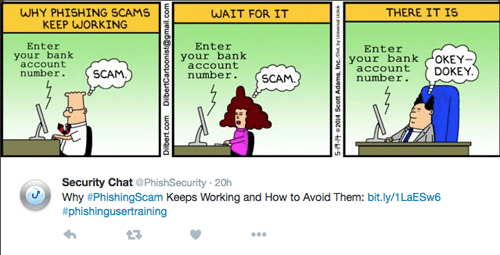
Go phishing – phishing attacks can be targeted at your email contact lists – the fastest way to lose friends and business contacts! Why does it work? I loved this Tweet by @PhishSecurity which sums it up.
Secondly, they have access to your emails. Doesn’t take long to figure out, for example, who you hold online accounts with, especially if you don’t practice good mailbox housekeeping.
Then, of course, there is the issue of passwords. Hands up how many people use the same passwords for multiple accounts and who change them infrequently? So, they have your password, they have your email address…next stop your other online accounts.
Of course, all this relates to personal addresses but the same employees who are ignoring basic internet security at home are likely to be doing so at work too.
I discussed this in my last post on managing the risks of remote working but it is worth emphasising that a recent survey in the US showed 63% of workers used a work mobile device for personal activities.
Incident management and response
All of the above underlines the need for information security policies, controls, training and staff engagement and a system for managing it all.
But, looking at it from Time Warner’s perspective, it also underlines the need for an effective incident response plan.
Sadly, attacks such as these are a way of life now and not just limited to careless organisations without the proper controls in place.
Implementing ISO 27001 will give you the best practice specification for an information security management system and this will, without doubt, reduce your risk.
However, within ISO 27001, 16.1.5 outlines the requirement for a procedure to cover how you respond to a security incident should it occur. This should include how you communicate any potential compromises in customer information security.
How you deal with your customers and, potentially, the press could be crucial to your reputation and even your share price. The immediate aftermath of a breach is not the time to be stumbling around wondering who should do or say what.
We are ISO 27001 accredited and use our own cloud software ISMS.Online to store all our controls and policies, including our procedure for responding to our own information security incidents.
Once an incident has occurred, it is assessed and recorded, describing the context and potential threat. The Senior Information Risk Officer has full visibility while the team on the ground manage the incident process, made easy by the use of the tool we have built for incident tracking. At any stage of the process tasks and alerts, with deadlines, can be set for those with responsibilities to action, including the CEO and Communications Manager.
Having a collaboration tool is really useful to cut through the noise of other communications such as email or voicemail. It also ensures all facts recorded are saved, for future reference and learning, and can easily be retrieved if necessary.
We hope we never need to call on our Communications Manager to handle a breach but, if we did, our systems ensure it would be done quickly and efficiently to minimise the impact on our customers and, of course, our reputation.
If you’d like to know more about how www.isms.online can support your ISMS, enabling effective communication around it, contact us to arrange a free demo or discuss your requirements in more detail.