It was my first day back at my desk on Monday this week and I almost scared myself to death reading this interesting article on cybercrime in 2015. The mere names associated with cyber threats warn of their malicious nature and give you a bad case of the heebie-jeebies. Who wants to be ‘hacked’ or suffer a ‘Masque attack’ or even suffer a ‘cyber-worm’? Yuk!
However, this is no nightmare, it’s reality. It seems the threats are getting more serious, more regular and have more costly consequences.Until recently I was a smug iOS user believing that, assuming I observed all the usual rules, the good guys at Apple had it covered. But, whilst Android attacks are more common, the blog predicts more rigorous attempts to attack iOS as they gain market share.
Concerns have also heightened as more organisations rely on teleworkers and the need for staff to remotely access their systems.
So, if you’ve embraced the leap to unified communications to help drive efficiencies, better collaboration and customer service then the chances are you have invested in technology and architecture that fully supports multiple operating systems and devices and even BYOD (bring your own device).
But have you equally embraced, and addressed the associated risks?
A survey carried out in the US last year highlighted 94% of full-time employees regularly connect their mobile device to a public Wi-Fi Network. Not in itself, a major issue but given the rest of the statistics reported, such as 41% did not know what two-factor authentication was and 37% only changed their passwords sporadically or annually, it’s very worrying. Read and tell me you are confident your policies and training have it covered!
I suspect a third of you haven’t. The HM Government Information Security Breaches Survey 2015 identified that 32% of respondents hadn’t carried out any form of security risk assessment and that was up from 20% on the previous year. Now that’s scary!
So what should I be doing?
Get a plan
A great place to start is to take a look at ISO 27001. It provides the ‘best-practice’ framework to keep you safe including areas such as protection from Malware, the control of software installation on operational systems, asset management and human resource security.
Following the ISO 27001 standard, with or without accreditation will encourage you to look at all areas of information security within your business and put in place policies and controls to not only protect your organisation but also what to do in case of a breach.
Manage your assets
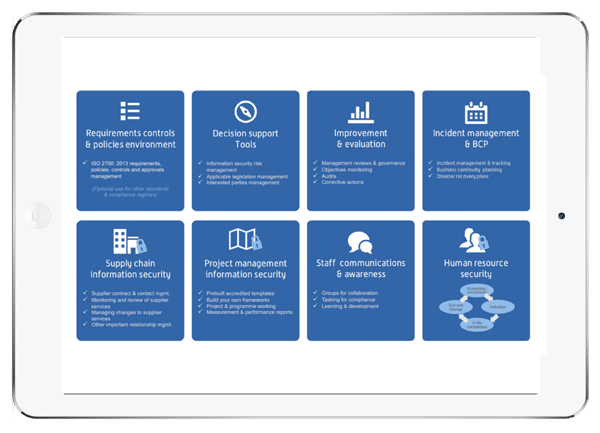
We have ISO 27001:2013 accreditation and 8.1 of the standard considers asset management. We use our own ISMS.online platform which has a framework where we record all assets and any device owned by an employee but used for information processing. That way, employee groups can be set-up by, for example, the operating system they use, and potential threats and vulnerabilities notified to everyone concerned at the click of a button. For urgent action, tasks can be set for the individuals to acknowledge and confirm when the necessary steps have been taken.
Reporting on information security events
Sadly security incidents will be inevitable but, thanks to ISO 27001, we have policies in place for reporting potential security threats such as lost or stolen devices, suspected breaches in security or malfunctions in software or hardware. Any suspected risk is considered by our Senior Information Risk Officer and, where necessary, entered on our system as a Security Incident. We use our tracking tool to follow the incident to a satisfactory conclusion and, wherever possible, a corrective action or improvement.
Employee education
It is true to say that no matter what solutions you put in place they are only as good as the engagement they receive from your employees.
ISO 27001 covers human resource security well but all the policies in the world will not protect you if an employee didn’t read his induction manual or understand the importance of information security in the organisation.
We know from all we read that the human factor is one of the biggest security headaches in any organisation so tackling it is a fundamental part of any information security management system. Luckily, this really is where ISMS.online comes into its own, benefiting from its heritage as a collaboration platform, pam.
All policies and controls are stored safely in one place with communication, from induction training right through to exit management, targeted to individuals on a need to know basis. Groups can be set-up around any criteria you choose and messages and updates only alerted to those they affect. Actions can be tasked with deadlines and sign-off or approval.
So, If your staff battle with hundreds of emails every day, the chances are they will miss the one about the latest major Android threat, iOS update or scam, and a crack in your armour may just have appeared. How much more useful would it be to set alerts with actionable deadlines that can be reviewed and signed-off?
Of course, many of you will view ISO 27001 as creating its own nightmare…. an abundance of paperwork and documents, difficult to engage staff in and costly in terms of resource to implement and maintain it.
It really doesn’t have to be that way. If you have invested in technology to resolve other business needs, then look to technology to make implementing and maintaining your ISMS simple and effective.
Keep the nightmares as just that, and make 2016 the year for tackling the risks head on with a an easy to manage information security management system.