Where should you start with ISO 27701:2025?
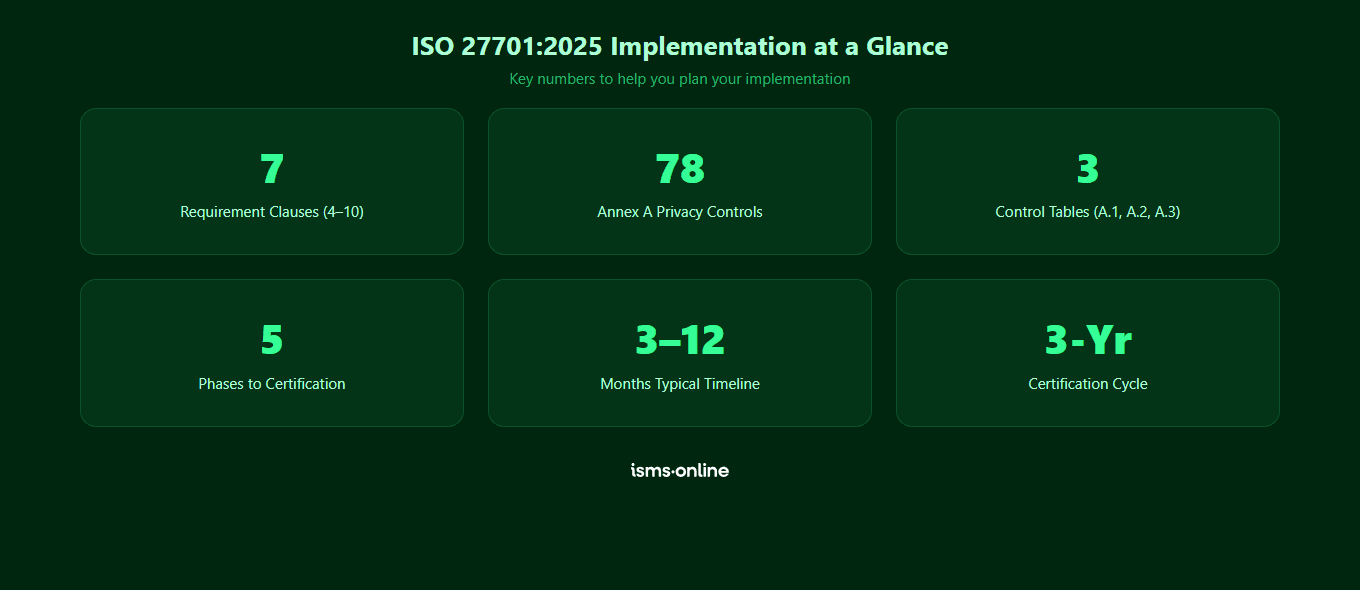
Implementing ISO 27701:2025 can feel overwhelming when you look at the full scope of management system requirements and Annex A privacy controls. The good news is that the implementation follows a logical, well-trodden path that thousands of organisations have navigated successfully.
This hub provides the practical guidance you need at each stage of your implementation journey, from initial gap analysis through to audit readiness.
What is the typical implementation process?
A successful ISO 27701:2025 implementation generally follows five phases:
| Phase | Activities | Typical Duration |
|---|---|---|
| 1. Gap analysis | Assess current privacy practices against the standard, identify gaps and prioritise actions | 2—4 weeks |
| 2. Planning | Define scope, prepare Statement of Applicability, create implementation plan, assign resources | 2—4 weeks |
| 3. Implementation | Develop policies, implement controls, configure processes, train staff | 2—6 months |
| 4. Internal audit | Conduct internal audit, address nonconformities, management review | 2—4 weeks |
| 5. Certification audit | Stage 1 (documentation review) and Stage 2 (implementation assessment) | 2—6 weeks |
What is a gap analysis and why does it matter?
A gap analysis is your starting point. It compares your current privacy practices against every requirement of ISO 27701:2025, identifying where you already comply and where work is needed. This assessment drives your implementation plan and helps you estimate the time, cost and effort required.
A thorough gap analysis covers the management system clauses (4—10), all applicable Annex A controls for your role (controller, processor or both) and supporting documentation such as policies, procedures and records.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

What is the Statement of Applicability?
The Statement of Applicability (SoA) is one of the most important documents in your PIMS. It lists every Annex A control, states whether each one is applicable to your organisation and justifies any exclusions. Your certification body will scrutinise the SoA during the audit, so it must be thorough and accurate.
For ISO 27701:2025, the SoA must address controls from three tables depending on your role:
- Table A.1 — PII controller controls (if you determine the purposes and means of processing)
- Table A.2 — PII processor controls (if you process personal data on behalf of a controller)
- Table A.3 — Shared controls applicable to both roles
What audit evidence do you need to prepare?
Certification auditors will look for objective evidence that your PIMS is not just documented but actively operating. Key evidence categories include:
- Policies and procedures — Privacy policy, data processing procedures, incident response plans
- Risk management records — Privacy risk assessments, risk treatment plans, risk register
- Operational records — Data processing records, consent logs, data subject request logs
- Training evidence — Privacy awareness training records, competency assessments
- Monitoring and review — Internal audit reports, management review minutes, corrective action records
Using a compliance platform like ISMS.online centralises all of this evidence in one place, making audit preparation significantly more efficient.

Get started easily with a personal product demo
One of our onboarding specialists will walk you through our platform to help you get started with confidence.

What are the most common implementation mistakes?
Organisations that struggle with ISO 27701:2025 implementation typically fall into a few common traps:
- Scoping too broadly — Trying to cover all data processing activities at once rather than starting with a manageable scope
- Treating it as a documentation exercise — Writing policies without implementing the underlying processes
- Ignoring the risk assessment — Privacy risk assessment (Clause 6) drives the entire system. Rushing this undermines everything that follows
- Insufficient management commitment — Without visible leadership support (Clause 5), implementation stalls
- Leaving internal audit too late — Internal audits should happen with enough time to address findings before the certification audit
Why choose ISMS.online for ISO 27701:2025 implementation?
- Pre-built PIMS framework — Every clause and control mapped with templates, policies and procedures ready to customise
- Gap analysis tools — Built-in assessment against the standard to identify exactly where you need to focus
- Statement of Applicability builder — Generate your SoA with justifications for every control decision
- Evidence management — Centralised document storage with version control and approval workflows
- Audit management — Plan, execute and track internal audits with structured findings and corrective actions
- Collaboration — Assign tasks, track progress and manage the entire implementation across your team
FAQs
How long does ISO 27701:2025 implementation typically take?
Most organisations achieve certification within 3 to 12 months. Smaller organisations with simpler data processing activities can move faster, particularly with a compliance platform. Larger organisations with complex processing across multiple jurisdictions may need the full 12 months.
Do you need to implement every Annex A control?
No. The controls in your Statement of Applicability depend on your role (controller, processor or both) and your privacy risk assessment. You must justify any exclusions, but it is normal for some controls not to apply to your specific data processing activities.
Can you implement ISO 27701:2025 without a consultant?
Yes. A compliance platform like ISMS.online provides the framework, templates and guidance that would otherwise come from a consultant. Many organisations achieve certification using a platform and their internal team, saving significant cost compared to the consultant route.
What if you already have ISO 27001?
If you already hold ISO 27001 certification, you have a significant head start. Much of the management system infrastructure (risk management, internal audit, management review, document control) transfers directly. Your implementation will primarily focus on the privacy-specific controls in Annex A and extending your existing processes to cover privacy risks.









