What does Annex D tell you?
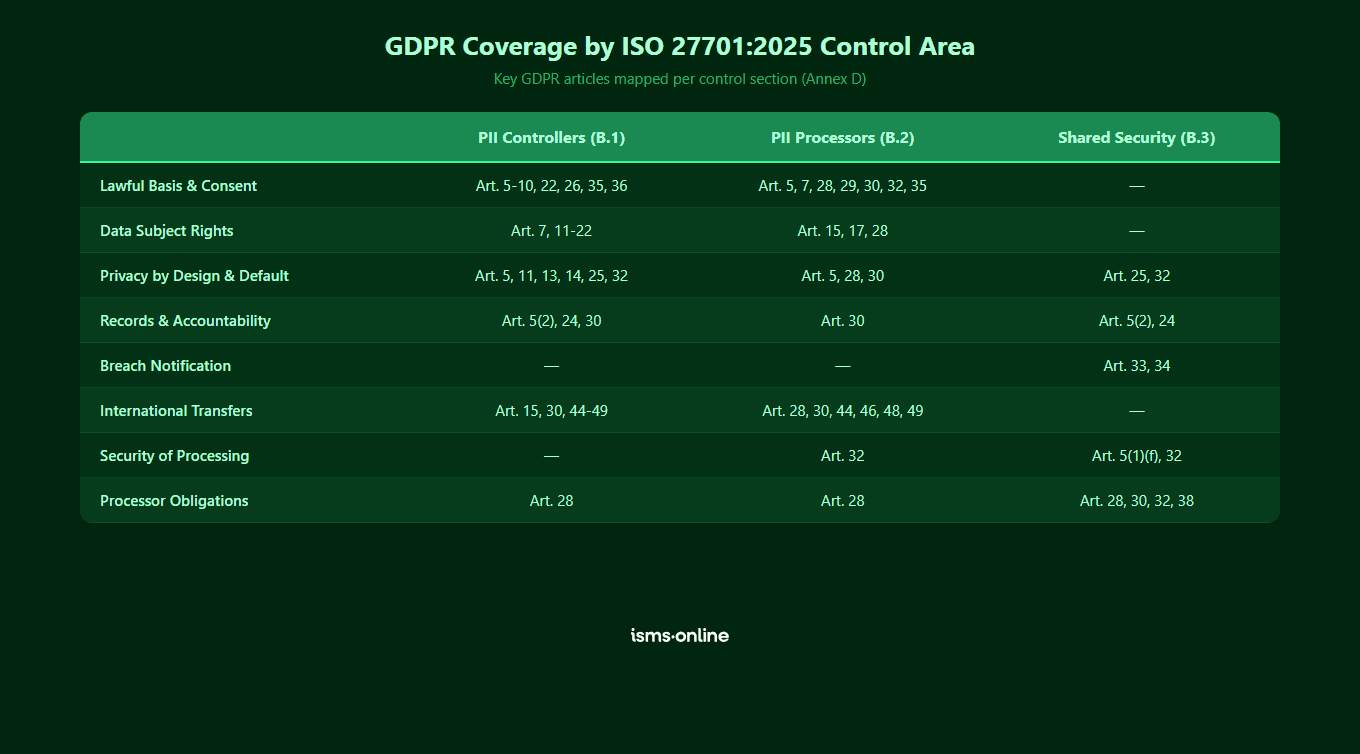
Annex D is an informative annex that maps ISO 27701:2025 clauses and controls to Articles 5 through 35 and 44 through 49 (excluding Articles 36-43) of the EU General Data Protection Regulation (GDPR). It shows how conformity with the requirements and controls of the standard can be relevant to fulfilling GDPR obligations.
Important: This mapping is purely indicative. It is the organisation’s responsibility to assess its own legal obligations and decide how to comply with them. Implementing ISO 27701:2025 controls does not automatically guarantee GDPR compliance, but it provides a structured framework for demonstrating that you have addressed key requirements.
For a broader look at the key changes, see what’s new in ISO 27701:2025. For mapping to other frameworks, see Annex C (ISO 29100) and Annex E (ISO 27018/29151). For 2019 equivalences, see the Annex F correspondence table.
How are the management system clauses mapped to GDPR?
The standard’s management system requirements (Clauses 4 to 10) map primarily to GDPR articles on data protection responsibility, certification, impact assessments and supervisory authority consultation.
| ISO 27701:2025 Clause | Key GDPR Articles | Topic |
|---|---|---|
| 4.1 Understanding the organization | Art. 24, 25, 28, 32 | Data protection responsibility, codes of conduct, certification |
| 4.2 Needs of interested parties | Art. 31, 35 | Cooperation with supervisory authority, DPIA consultation |
| 4.3-4.4 Scope and PIMS | Art. 32 | Security of processing |
| 5.2 Privacy policy | Art. 24 | Responsibility of the controller |
| 5.3 Roles and responsibilities | Art. 27, 37-39 | Representatives of non-EU organisations, DPO designation and tasks |
| 6.1.2-6.1.3 Risk assessment and treatment | Art. 32, 35 | Security of processing, data protection impact assessment |
How do PII controller controls (B.1) map to GDPR?
The PII controller implementation guidance in Annex B maps extensively to GDPR’s core principles and data subject rights. Each B.1 control provides implementation guidance for the corresponding Annex A control with the same numbering (e.g. B.1.2.2 is the guidance for A.1.2.2).
| Annex B Guidance | Annex A Control | Key GDPR Articles | Topic |
|---|---|---|---|
| B.1.2.2 | A.1.2.2 Identify and document purpose | Art. 5(1)(b), 32(4) | Purpose limitation |
| B.1.2.3 | A.1.2.3 Identify lawful basis | Art. 5(1)(a), 6(1)-(4), 8, 9, 10, 17, 18, 22 | Lawfulness, special categories, criminal data, children’s consent |
| B.1.2.4-5 | A.1.2.4 Determine consent, A.1.2.5 Obtain and record consent | Art. 7, 8, 9(2)(a) | Conditions for consent |
| B.1.2.6 | A.1.2.6 Privacy impact assessment | Art. 35 | DPIA and prior consultation |
| B.1.2.9 | A.1.2.9 Records of processing | Art. 5(2), 24, 30 | Accountability, records of processing activities |
| B.1.3.3-4 | A.1.3.3 Information for PII principals, A.1.3.4 Providing information | Art. 11-15, 18, 21 | Transparency, information to data subjects |
| B.1.3.5 | A.1.3.5 Withdraw consent | Art. 7(3), 13, 14, 18 | Right to withdraw consent, restriction of processing |
| B.1.3.6 | A.1.3.6 Object to processing | Art. 13, 14, 21 | Right to object |
| B.1.3.7 | A.1.3.7 Access, correction or erasure | Art. 5(1)(d), 13, 14, 16, 17 | Right of access, rectification, erasure |
| B.1.3.9 | A.1.3.9 Providing copy of PII | Art. 15(3-4), 20 | Right to data portability |
| B.1.3.10 | A.1.3.10 Handling requests | Art. 12(3-6), 15 | Procedures for exercising rights |
| B.1.3.11 | A.1.3.11 Automated decision making | Art. 13, 14, 22 | Automated individual decision-making, profiling |
| B.1.4.2-3 | A.1.4.2 Limit collection, A.1.4.3 Limit processing | Art. 5(1)(b-c), 25(2) | Purpose limitation, data minimisation, data protection by design |
| B.1.4.6 | A.1.4.6 De-identification and deletion | Art. 5(1)(c-e), 6(4)(e), 11, 32 | Data minimisation, storage limitation, pseudonymisation |
| B.1.5.2 | A.1.5.2 Basis for international transfer | Art. 15, 30, 44-49 | Transfers to third countries, adequacy, safeguards, BCRs, derogations |

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

How do PII processor controls (B.2) map to GDPR?
The PII processor implementation guidance follows the same numbering convention. Each B.2 reference corresponds to its matching A.2 control.
| Annex B Guidance | Annex A Control | Key GDPR Articles | Topic |
|---|---|---|---|
| B.2.2.2 | A.2.2.2 Customer agreement | Art. 28, 35 | Processor obligations, DPIA support |
| B.2.2.3 | A.2.2.3 Organisation’s purposes | Art. 5(1)(a-b), 28(3)(a), 29, 32 | Processing under controller authority |
| B.2.2.4 | A.2.2.4 Marketing and advertising | Art. 7(4) | Consent not conditional on service |
| B.2.2.7 | A.2.2.7 Records of processing | Art. 30(2-5) | Records of processing activities (processor) |
| B.2.3.2 | A.2.3.2 Obligations to PII principals | Art. 15(3), 17(2), 28(3)(e) | Assist controller with data subject requests |
| B.2.4.3 | A.2.4.3 Return or disposal of PII | Art. 28(3)(g), 30(1)(f) | Deletion or return after end of service |
| B.2.5.2 | A.2.5.2 International transfers | Art. 44, 46, 48, 49 | Transfers to third countries (processor) |
| B.2.5.7 | A.2.5.7 Disclosure of subcontractors | Art. 28(2) | Sub-processor authorisation |
| B.2.5.8 | A.2.5.8 Engagement of subcontractor | Art. 28(2-4) | Sub-processor contractual requirements |
| B.2.5.9 | A.2.5.9 Change of subcontractor | Art. 28(2) | Sub-processor change notification |
How do shared security controls (B.3) map to GDPR?
The shared security controls primarily map to GDPR Article 5(1)(f) (integrity and confidentiality) and Article 32 (security of processing). Each B.3 reference corresponds to its matching A.3 control.
| Annex B Guidance | Annex A Controls | Key GDPR Articles | Topic |
|---|---|---|---|
| B.3.5-9 | A.3.5 Classification, A.3.6 Labelling, A.3.7 Transfer, A.3.8 Identity, A.3.9 Access | Art. 5(1)(f) | Integrity and confidentiality principle |
| B.3.10, B.3.13 | A.3.10 Supplier agreements, A.3.13 Legal requirements | Art. 28, 32 | Processor obligations, security of processing |
| B.3.11-12 | A.3.11 Incident management, A.3.12 Incident response | Art. 33-34 | Breach notification (to supervisory authority and data subjects) |
| B.3.14, B.3.16 | A.3.14 Protection of records, A.3.16 Compliance | Art. 5(2), 24, 32 | Accountability, compliance verification |
| B.3.19-25 | A.3.19 Clear desk, A.3.20 Storage media, A.3.21 Disposal, A.3.22 Endpoints, A.3.23 Authentication, A.3.24 Backup, A.3.25 Logging | Art. 5(1)(f), 32(1)(a) | Integrity, confidentiality, encryption and pseudonymisation |
| B.3.26 | A.3.26 Use of cryptography | Art. 32(1)(a) | Encryption and pseudonymisation |
| B.3.27-29 | A.3.27 Secure development, A.3.28 Application security, A.3.29 System architecture | Art. 25(1) | Data protection by design |
| B.3.31 | A.3.31 Test information | Art. 5(1)(f), 32 | Protection of PII in test environments |

Get started easily with a personal product demo
One of our onboarding specialists will walk you through our platform to help you get started with confidence.

How should you use this mapping in practice?
The Annex D mapping is a starting point, not a compliance checklist. Here is how to use it effectively:
- Gap analysis: If you have implemented ISO 27701:2025 controls, use the mapping to identify which GDPR articles you have already addressed and where gaps remain
- Audit evidence: Reference the mapping when demonstrating to supervisory authorities or auditors that your PIMS supports GDPR compliance
- Cross-framework reporting: Use the mapping to produce unified compliance reports that show how one set of controls satisfies multiple regulatory requirements
- DPIA support: The mapping to Article 35 helps you connect your privacy impact assessments (control A.1.2.6) to the GDPR’s DPIA requirements
- Transition planning: If you are moving from ISO 27701:2019, use the mapping alongside the transition guide to check GDPR coverage under the new control structure
Remember that GDPR compliance involves obligations beyond what any single standard covers (e.g. appointing a lead supervisory authority, responding to enforcement actions). The mapping shows where ISO 27701:2025 provides structured support, not where compliance is guaranteed.
Why choose ISMS.online for GDPR and ISO 27701 alignment?
ISMS.online helps you manage both frameworks in a single platform:
- Integrated compliance views — See how ISO 27701:2025 controls map to GDPR obligations in one dashboard
- Evidence library — Attach the same evidence (policies, DPIAs, breach procedures) to both ISO 27701 controls and GDPR requirements
- Regulatory tracking — Stay current with GDPR enforcement trends and update your PIMS accordingly
- Data mapping — Document your processing activities, lawful bases and international transfers in a structured register
- Breach management — Track incidents from detection through notification, aligned to both Art. 33/34 and controls A.3.11/A.3.12
FAQs
Does implementing ISO 27701:2025 mean I am GDPR compliant?
Not automatically. ISO 27701:2025 provides a management system framework that supports many GDPR requirements, but GDPR compliance depends on your specific processing activities, lawful bases, and how you implement and operate your controls. The Annex D mapping is indicative, not a compliance certificate. For a detailed look at how the standard supports GDPR, see the GDPR compliance guide.
Which GDPR articles are most comprehensively covered by ISO 27701:2025?
Articles 5 (principles), 6 (lawful basis), 12-22 (data subject rights), 25 (data protection by design), 28 (processor obligations), 30 (records of processing), 32 (security), 33-34 (breach notification) and 44-49 (international transfers) all have extensive mappings to ISO 27701:2025 controls. The controller controls provide the broadest coverage, addressing data subject rights, purpose limitation and lawful basis requirements.
Has the GDPR mapping changed from the 2019 edition?
The mapping has been updated to reflect the new control numbering (Annex A/B structure instead of Clauses 6-8), but the underlying GDPR articles covered remain broadly similar. The 2025 mapping is more granular in some areas due to the restructured control set. See the full comparison of changes for details.
What is the relationship between Annex A and Annex B?
Annex A defines the privacy controls (what you must do) and Annex B provides the corresponding implementation guidance (how to do it). They share the same numbering: A.1.2.2 is the control and B.1.2.2 is its guidance. Both annexes are normative in the 2025 edition. The Annex D mapping references the B numbering because it maps the implementation guidance to GDPR articles, but each B control has a direct A counterpart.









