Why does ISO 27701:2025 matter for CISOs?
Privacy is no longer a legal function that sits outside the CISO’s remit. As data protection regulation has expanded globally, boards increasingly expect the CISO to take operational ownership of privacy alongside information security. Securing management buy-in is a critical first step. ISO 27701:2025 provides the management system framework to do this effectively.
The 2025 edition is a significant improvement for CISOs because it now functions as a standalone standard. While the 2019 edition was purely an extension of ISO 27001, the 2025 version contains its own complete management system requirements in Clauses 4 to 10. This gives CISOs two options:
- Integrated approach — Extend your existing ISO 27001 ISMS to include ISO 27701 privacy controls, running both as a unified management system
- Standalone approach — Implement ISO 27701 independently if your organisation needs privacy certification without full information security certification
For most CISOs who already manage an ISO 27001 certified ISMS, the integrated approach delivers the greatest efficiency. The management system clauses share the same high level structure, so you are building on existing processes rather than creating new ones.
How does ISO 27701:2025 relate to ISO 27001?
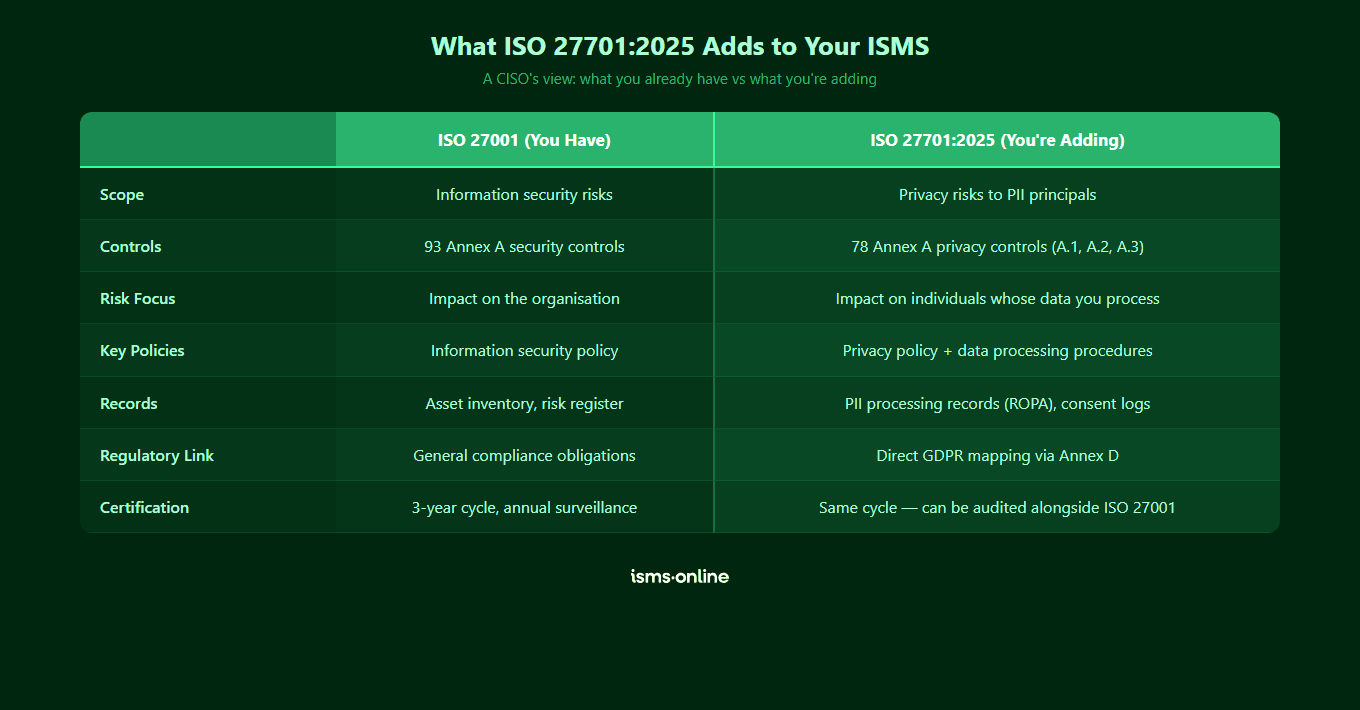
Understanding the relationship between these standards is critical for CISOs planning their approach:
| Area | ISO 27001 | ISO 27701:2025 | Integration opportunity |
|---|---|---|---|
| Scope | Information security | Privacy and PII protection | Define a single scope covering both security and privacy |
| Risk assessment | Information security risks | Privacy risks to PII principals | Extend your risk methodology to include privacy impact dimensions |
| Controls | 93 Annex A controls | Dedicated Annex A privacy controls across 5 categories | Map overlapping controls and add privacy-specific ones |
| Statement of Applicability | Covers ISO 27001 Annex A | Covers ISO 27701 Annex A | Maintain separate SoAs or create a combined document |
| Internal audit | ISMS audit programme | PIMS audit programme | Combine into a single audit schedule covering both scopes |
| Management review | ISMS performance review | PIMS performance review | Single management review covering security and privacy metrics |
The key insight for CISOs is that ISO 27701:2025 does not replace ISO 27001. It complements it. Your information security controls remain essential — ISO 27701 adds the privacy-specific controls and processes that address how personal data is collected, processed, shared and retained.
What resources and budget are needed?
CISOs need to plan for three categories of resource:
People:
- A privacy lead or PIMS manager to coordinate implementation (this may be the DPO, a dedicated hire or a member of the existing security team)
- Process owners across the business who manage PII processing activities
- Internal audit capability for the privacy scope
- Legal support for interpreting applicable privacy legislation
Time:
- If you already have ISO 27001, extending to ISO 27701 typically takes 3 to 6 months for the implementation phase
- From scratch, allow 6 to 12 months depending on organisational complexity
- Certification audit adds 4 to 8 weeks
Budget:
- Certification body fees for the audit (incremental if combined with ISO 27001)
- Platform or tooling costs for managing the PIMS
- Training for staff involved in privacy processes
- Potential consultancy for gap analysis or specialist advice

Start your free trial
Want to explore?
Sign up for your free trial today and get hands on with all the compliance features that ISMS.online has to offer

How should CISOs integrate privacy into the security programme?
The most effective approach is to extend your existing ISMS rather than building a parallel privacy management system. Here is a practical integration roadmap:
Phase 1: Scope and gap analysis (weeks 1 to 4)
- Map your current PII processing activities across the organisation
- Identify which Annex A controls apply to your processing scope
- Conduct a thorough gap analysis to assess existing controls against ISO 27701 requirements
- Determine whether you will pursue standalone or integrated certification
Phase 2: Risk assessment extension (weeks 5 to 8)
- Extend your risk assessment methodology to include privacy risk dimensions (impact on PII principals, not just organisational impact)
- Identify privacy-specific risks that your information security risk assessment may not currently capture
- Develop risk treatment plans for identified privacy risks
Phase 3: Control implementation (weeks 9 to 20)
- Implement or enhance controls to meet ISO 27701 Annex A requirements
- Update policies to incorporate privacy-specific requirements
- Establish or formalise data subject rights processes
- Implement privacy by design and default procedures
- Review and update third party agreements for PII processing
Phase 4: Operate and audit (weeks 21 to 24)
- Run the integrated management system for a minimum operating period
- Conduct internal audits covering the privacy scope
- Hold management review with privacy performance data included
- Address any nonconformities identified
How should CISOs report privacy governance to the board?
Board reporting on privacy needs to be strategic, concise and risk focused. CISOs should present privacy governance as a business risk issue, not a technical one. Effective board reporting includes:
| Metric category | Example metrics | Board relevance |
|---|---|---|
| Regulatory exposure | Number of jurisdictions, pending legislation changes, regulatory correspondence | Quantifies the legal risk landscape |
| Control maturity | Percentage of ISO 27701 controls implemented and evidenced | Shows progress toward certification readiness |
| Incident trends | Privacy incidents, near misses, data subject complaints, breach notifications | Indicates operational effectiveness of privacy controls |
| Third party risk | Processors assessed, outstanding due diligence, contract compliance rates | Highlights supply chain privacy risk |
| Data subject rights | Request volumes, response times, completion rates | Demonstrates operational compliance with GDPR obligations |
| Certification status | Audit findings, nonconformities open/closed, next audit date | Provides assurance that external validation is on track |
Present these metrics in the context of business outcomes: customer retention, contract wins, regulatory confidence and risk reduction. For a ready-made board presentation, see our executive summary for board members. Boards respond to the language of risk and opportunity, not technical compliance detail.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

What are the key challenges CISOs face with ISO 27701?
Based on common implementation experiences, CISOs should prepare for these challenges:
- Cultural shift — Security teams think in terms of organisational risk. Privacy requires thinking about impact on individuals. This shift in perspective takes time and training
- Cross functional coordination — Privacy touches every department that processes PII. CISOs must engage HR, marketing, sales, customer services and product teams, not just IT
- Legal interpretation — ISO 27701 requires organisations to identify applicable privacy legislation. CISOs need access to legal expertise to interpret requirements across multiple jurisdictions
- Data mapping complexity — Understanding where PII flows, who processes it and under what legal basis is often more complex than anticipated. Start early and iterate
- Balancing security and privacy — Security controls sometimes conflict with privacy principles (for example, extensive logging for security monitoring versus data minimisation). CISOs must find the right balance
For CISOs managing organisations that process personal data related to AI, IoT or biometric systems, additional privacy controls may be needed to address automated decision making, profiling and special category data.
Why choose ISMS.online for ISO 27701:2025?
ISMS.online gives CISOs a single platform to manage both information security and privacy:
- Integrated management system — Run ISO 27001 and ISO 27701 from one platform with shared processes, policies and evidence where appropriate
- Pre-configured framework — Start with all ISO 27701:2025 clauses and Annex A controls mapped and ready to implement, eliminating the blank page problem
- Unified risk register — Manage information security and privacy risks in a single register with distinct impact categories for organisational and individual harm
- Combined audit programme — Schedule and track audits across both standards, reducing audit fatigue and ensuring comprehensive coverage
- Board reporting dashboards — Generate privacy governance reports that translate control data into the risk language boards expect
- Cross-standard mapping — See how controls map across ISO 27001, ISO 27701 and GDPR requirements, reducing duplication of effort
- Team collaboration — Assign privacy tasks to process owners across the business, track progress and maintain accountability without email chains or spreadsheets
FAQs
Should the CISO own the PIMS or should it sit with the DPO?
This depends on your organisation’s structure. In many organisations, the CISO owns the management system (ISMS and PIMS) while the DPO provides independent advice and monitoring. This separation preserves the DPO’s independence under GDPR Article 38 while ensuring the PIMS benefits from the CISO’s operational management experience. In smaller organisations, one person may fulfil both roles, but independent audit arrangements should be established.
Can we achieve ISO 27701 certification during our next ISO 27001 surveillance audit?
This is possible but depends on your certification body and readiness. Some certification bodies offer combined audits where ISO 27701 certification can be assessed alongside an ISO 27001 surveillance or recertification audit. You will need to have the PIMS fully implemented and operational with evidence of at least one management review and internal audit cycle. Discuss timing with your certification body early to align schedules.
What additional audit days should we budget for ISO 27701?
For an integrated audit, ISO 27701 typically adds 1 to 3 days on top of your ISO 27001 audit for initial certification and 0.5 to 1.5 days for surveillance audits. The exact duration depends on the number of PII processing activities in scope, the number of jurisdictions and the complexity of your data flows. Your certification body will provide a formal audit time calculation based on your scope.
Do we need separate policies for ISO 27701 or can we extend our ISO 27001 policies?
You can extend existing policies in most cases. Your information security policy can be expanded to include privacy objectives and commitments. Your risk assessment methodology can be extended to include privacy risk dimensions. However, you will need some privacy-specific documents such as a PII processing register, data subject rights procedures and privacy notices. ISMS.online provides templates for all required documentation.
How does ISO 27701 help CISOs manage international data transfer obligations?
ISO 27701:2025 includes specific controls addressing the identification and documentation of international PII transfers, legal bases for transfers and contractual safeguards with receiving parties. For CISOs operating across multiple jurisdictions, the standard provides a structured approach to mapping transfer flows, assessing transfer risks and maintaining appropriate safeguards. The Annex D GDPR mapping links these controls directly to Chapter V transfer requirements.









