Why ISO 27001 Compliance Software is Critical for Cyber Security
Security teams chase operational velocity while boards, auditors, and enterprise buyers tighten scrutiny. Tool sprawl scatters proofs of control. Third-party dependencies expand the blast radius if ownership is unclear. Audit sprints drain capacity and leave brittle systems that crack under the next questionnaire.
- Tooling sprawl fragments evidence across SIEM, EDR, SCA, and ticketing.
- Manual evidence hunts delay enterprise deals and stall procurement approvals.
- Undefined owners erode accountability and blur remediation priorities.
- Audit sprints cause burnout, brittle processes, and recurring fire drills.
- Scattered repositories weaken your Statement of Applicability and confuse reviewers.
An ISO-first operating system resolves these pains by linking risks, controls, assets, owners, and evidence into one narrative, making ownership visible and readiness continuous.
Regulatory Alignment – ISO 27001 & NIST CSF & CIS Controls & SOC 2 & PCI DSS
Boards and auditors care about resilience they can verify—not slideware. ISO 27001’s risk-based backbone translates into the operational discipline buyers expect. When ownership, cadence, and evidence stay visible, responses land faster and third-party exposure narrows.
How ISO-First Maps to NIST CSF
- Identify → Protect: Risk-based controls align with asset inventories, baselines, and impact classes so security plans stay current and defensible.
- Detect → Respond: Incident response, exercises, and post-incident reviews show operational readiness that withstands scrutiny.
- Recover: Linked actions and CAPA logs prove lessons learned and continuous improvement over time.
How ISO-First Maps to CIS Controls
- Inventory & Control of Assets/Software: Service/asset scoping and change history reduce audit noise and improve control accuracy.
- Vulnerability Management & Secure Configuration: Recurring checks and exportable packs show test cadence, patch SLAs, and deviations.
- Access Control & Training: Role matrices, attestations, and training evidence centralize accountability.
How ISO-First Maps to SOC 2 & PCI DSS
- SOC 2 (Security, Availability, Confidentiality): Dynamic SoA with linked evidence accelerates auditor Q&A and follow-ups.
- PCI DSS: Scoped services, change logs, and supplier obligations demonstrate control boundary clarity without parallel paperwork.
- Third-party risk: Tiering, SLAs, and monitoring narrow concentration and performance risk.
An ISO-first operating system lets cyber teams show real operational resilience across NIST CSF, CIS Controls, SOC 2, PCI DSS, and NIS 2—without parallel paperwork.

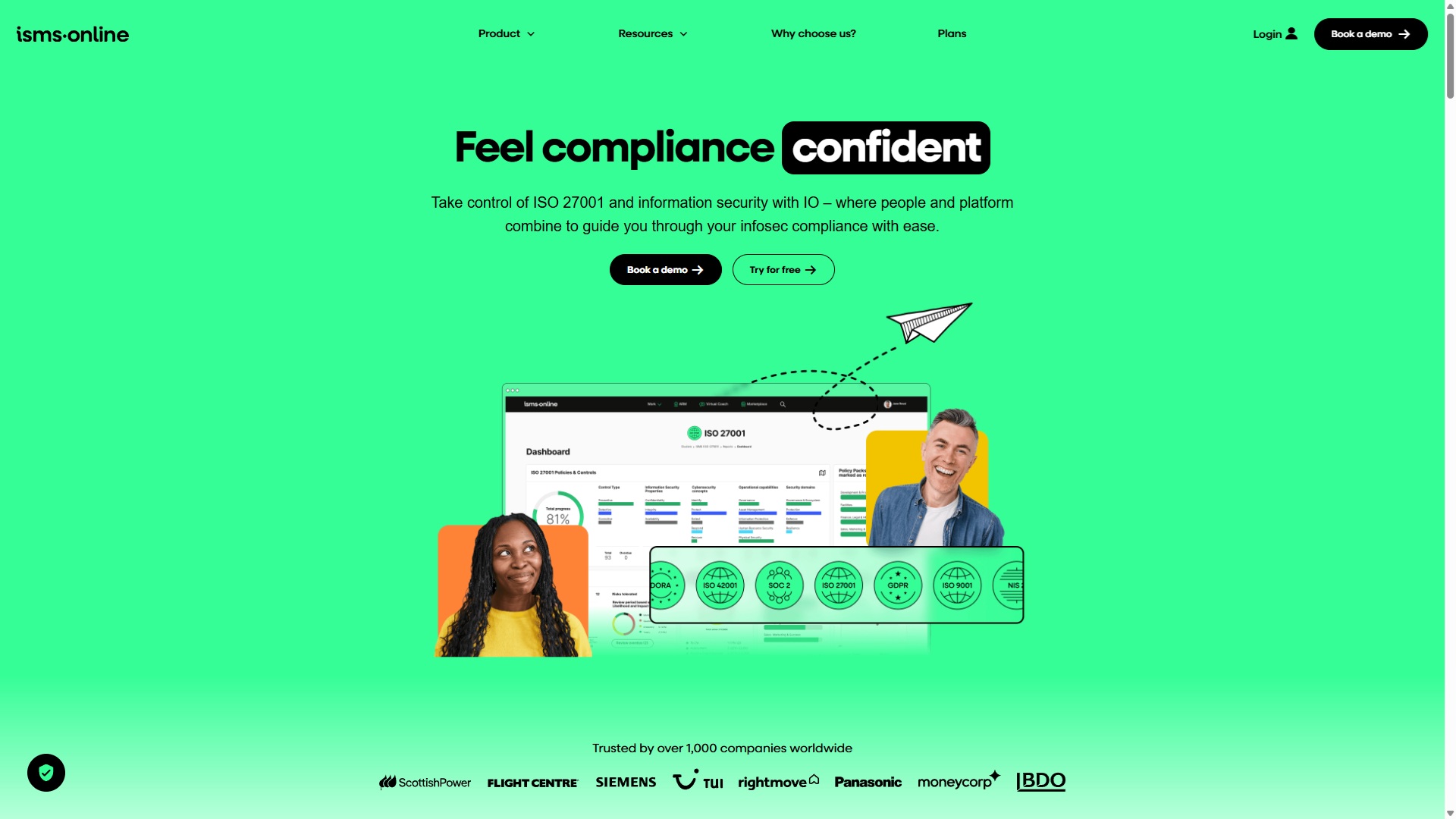
ISO 27001 made easy
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Risk Management for the Cyber Security Sector
Risk work should move every week, not just at audit time. Linked risks, controls, assets, and owners clarify accountability; consolidated views improve board decisions. Evidence reuse speeds renewals, while management reviews drive continuous improvement without fire drills.
- Identify: Capture risks at service/asset level; tie to threat models, detections, and business impact.
- Treat: Assign actions, map to controls and CAPA, set due dates; keep a traceable history that becomes ready-made evidence.
- Monitor: Run recurring checks (e.g., vulnerability scans, control tests) and collect artifacts; reuse evidence across risks and controls.
- Review: Hold scheduled management reviews; record decisions, risk acceptances, and exceptions to steer priorities.
- Report: Use consolidated risk views, MTTR trends, and patch SLAs to brief executives and focus funding where exposure is rising.
- Renew: Roll forward linked evidence and SoA changes so certification and customer assessments move faster.
An ISO-first operating system turns risk into a weekly workflow—ownership stays clear, evidence stays current, and decisions stay defensible.
A Checklist — What You Should Look For By Role
CTO / VP Engineering
- ISO-first backbone prevents evidence sprawl and keeps one source of truth.
- Integrations act as data feeders; the ISMS governs cadence and ownership.
- Environment scoping and change history protect delivery velocity during audits.
- Exportable architecture and control views speed technical due diligence.
CISO / Head of SecOps
- Linked risks, controls, assets, owners, and evidence clarify status.
- A dynamic Statement of Applicability improves auditor confidence and responses.
- Scheduled management reviews sustain governance cadence and measurable improvements.
- Incident/vulnerability workflows and exceptions keep remediation on course.
GRC / Compliance
- Evidence reuse accelerates renewals and enterprise assessments.
- Policy lifecycle with versioning, approvals, and attestations maintains consistency.
- Exportable overviews accelerate diligence and internal reporting.
- Mapping across NIST CSF, CIS Controls, SOC 2, PCI DSS, NIS 2 reduces rework.
Founder / RevOps
- One evidence source reduces audit fatigue and shortens enterprise deal cycles.
- Clear owners and milestones keep momentum through procurement gates.
- Framework expansion supports market entry without parallel tooling.
- Commercial predictability improves as fire drills give way to steady cadence.
Capability Comparison for Cyber Security
| Capability | Why it Matters to Cyber Security | What Good Looks Like |
|---|---|---|
| ISO-first system of record | Reduces evidence sprawl; keeps a single narrative for buyers/auditors | One repository linking risks, controls, assets, owners, and evidence |
| Dynamic Statement of Applicability | Improves auditor confidence and speeds Q&A | Live SoA with statuses, rationales, and change history |
| Linked risks–controls–evidence | Clarifies ownership and strengthens decisions | Bi-directional links; assignees; deadlines; traceable CAPA |
| Management reviews workspace | Sustains governance cadence and measurable improvement | Scheduled reviews with decisions, exceptions, and actions captured |
| Evidence reuse & audit packs | Accelerates renewals and enterprise assessments | On-demand export sets mapped to controls, periods, and requests |
| Supplier/TPRM oversight | Reduces third-party concentration and performance risk | Tiering, assessments, obligations, and monitoring tied to services |
| Policy lifecycle & approvals | Prevents drift and inconsistent execution | Versioning, approvals, attestations, review reminders |
| Change log & scope management | Protects delivery speed during audits | Service/asset scoping, release notes, audit-ready diffs |
| Executive/board overviews | Accelerate diligence and funding decisions | Concise summaries of risk, control health, and actions |
| Framework expansion (NIST, CIS, SOC 2, PCI, NIS 2) | Avoids parallel paperwork and fragmented assurance | Reuse of core assets and evidence across frameworks without rework |

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

How You Will See Benefits in 90 to 180 Days
Shift from audit sprints to a steady operating rhythm that compounds value across sales, audits, and oversight.
- Faster enterprise approvals: Linked work shortens security questionnaires and consolidates due-diligence responses.
- Lower audit drag: Continuous readiness reduces audit costs and removes last-minute scrambles.
- Stronger buyer trust: One narrative of control increases confidence with security reviewers and strategic partners.
- Predictable renewals: A stable cadence and reusable evidence stabilise capacity planning and budgets.
- Team momentum: Clear owners, scheduled reviews, and CAPA tracking keep improvements moving week by week.
- Framework reuse: The same risks, controls, and evidence carry across NIST CSF, CIS Controls, SOC 2, PCI DSS, and NIS 2—without parallel paperwork.
- Tighter supplier assurance: Structured oversight tied to services reduces third-party exposure and review cycles.
When risks, controls, and evidence live in one system of record, audit packs assemble from the work itself and stakeholders can verify readiness at a glance.
Best ISO 27001 Compliance Software for Cyber Security — A Quick Shortlist
ISMS.online
An ISO-first system of record designed to run the ISMS—not just pass an audit. Guided workflows link risks, assets, controls, owners, and evidence so questionnaires shrink and reviews stay predictable.
A dynamic SoA, management reviews, and exportable auditor packs keep readiness continuous across ISO 27001 today and NIST, CIS, SOC 2, PCI DSS and NIS 2 tomorrow. Connectors can feed artifacts; the ISMS keeps the governance cadence.
Vanta
Automation-first and highly integrated — ideal for fast-paced SOC 2 audits. For ISO 27001, though, success depends on more than automated testing. You’ll still need structured policy governance, defined responsibilities, and review cycles to keep your management system effective over time.
Drata
Automation with wide-ranging integrations that simplify evidence gathering and monitoring. It’s a strong companion for SOC 2 readiness, but ISO 27001 requires an ongoing governance rhythm. Without disciplined oversight, improvement actions and audit readiness can drift out of sync with your ISMS objectives.
Sprinto
Price-forward automation with a wide integration surface that moves quickly from zero to audit. A pragmatic on-ramp; long-term outcomes rely on clear owners, milestones, and recurring management reviews.
Secureframe
Automation plus questionnaires and trust-center features at higher tiers can speed diligence. Ensure your internal cadence—reviews, internal audits, and CAPA—remains the backbone of maturity.
DataGuard
Hybrid software + services model is useful when internal capacity is thin. Weigh commercial complexity and keep one authoritative system of record for day-to-day operation.
Strike Graph
Automation/GRC-lite proposition with public pricing offers a solid entry point. Validate how risks, controls, and evidence roll up into a management-ready narrative stakeholders will trust.
HiComply
Template-led approach with transparent tiers speeds initial drafting. Lasting value comes from clear ownership, traceability, and a steady review cadence across the year.
Experience the ISMS.online Platform
A live ISMS.online walkthrough shows end-to-end traceability across risks, controls, owners, and evidence.
You’ll see how a linked Statement of Applicability speeds auditor responses, how a steady governance rhythm sustains improvement, and how cross-mapped evidence helps you reuse work across NIST CSF, CIS Controls, SOC 2, PCI DSS, and NIS 2—without duplicate projects.
Find out more by booking a demo.
Frequently Asked Questions
How Quickly Can Security Teams See Value?
Most teams establish cadence within 90–180 days when owners, reviews, and CAPA are scheduled from day one. Linked work shortens questionnaires and lowers audit effort.
How Does This Help With NIST CSF, CIS Controls, SOC 2, PCI DSS, and NIS 2?
Risk-based controls map to operational-resilience themes; review schedules support governance obligations; cross-mapped evidence lowers the time to add frameworks without duplicate projects.
What Should I See on a Demo to Confirm Traceability?
A live ISMS overview that links a risk → control → owner → current evidence—plus the corresponding SoA entry and rationale.
Will Integrations Be Enough on Their Own?
Connectors improve artifact collection speed, but an ISO-first backbone sustains maturity. The ISMS remains the source of truth for ownership, reviews, and improvements.
How Does the SoA Connect to Real Work?
A dynamic SoA linked to tasks, evidence, and applicability rationales lets auditors verify status in context and accelerates responses during reviews.
What About Vulnerability and Incident Workflows?
Service-level tracking, scheduled tests, and linked findings keep risk visible. CAPA and exceptions reduce exposure and shorten follow-ups.
Can We Reuse Effort Across ISO 27001, HIPAA, GDPR/ISO 27701, and SOC 2?
Yes. One narrative of control with mapped requirements allows evidence and owners to serve multiple frameworks—without parallel paperwork.
How Are Roles and Accountability Handled?
Clear owners, approvals, and management reviews sustain the governance rhythm. Dashboards and exportable overviews help boards see progress and exceptions.
What Are Typical Cost Drivers?
Seats, frameworks in scope, assurance depth (evidence history, SoA detail, supplier oversight), and any multi-entity structure.
What Does Implementation Look Like?
Scope services and assets, import policies and risks, link controls and evidence, set your review calendar, and assemble audit packs directly from the work.
Does This Replace Our GRC or Ticketing Tools?
Keep ticketing for engineering work management. Use integrations as feeders; let the ISMS hold the authoritative story of risks, controls, evidence, and ownership.
How Do We Prepare for the First Surveillance or Renewal?
Continuous reviews, internal audits, and corrective actions build re-usable auditor packs. Predictable cadence stabilises effort and timelines year over year.









