How is Annex A structured in ISO 27701:2025?
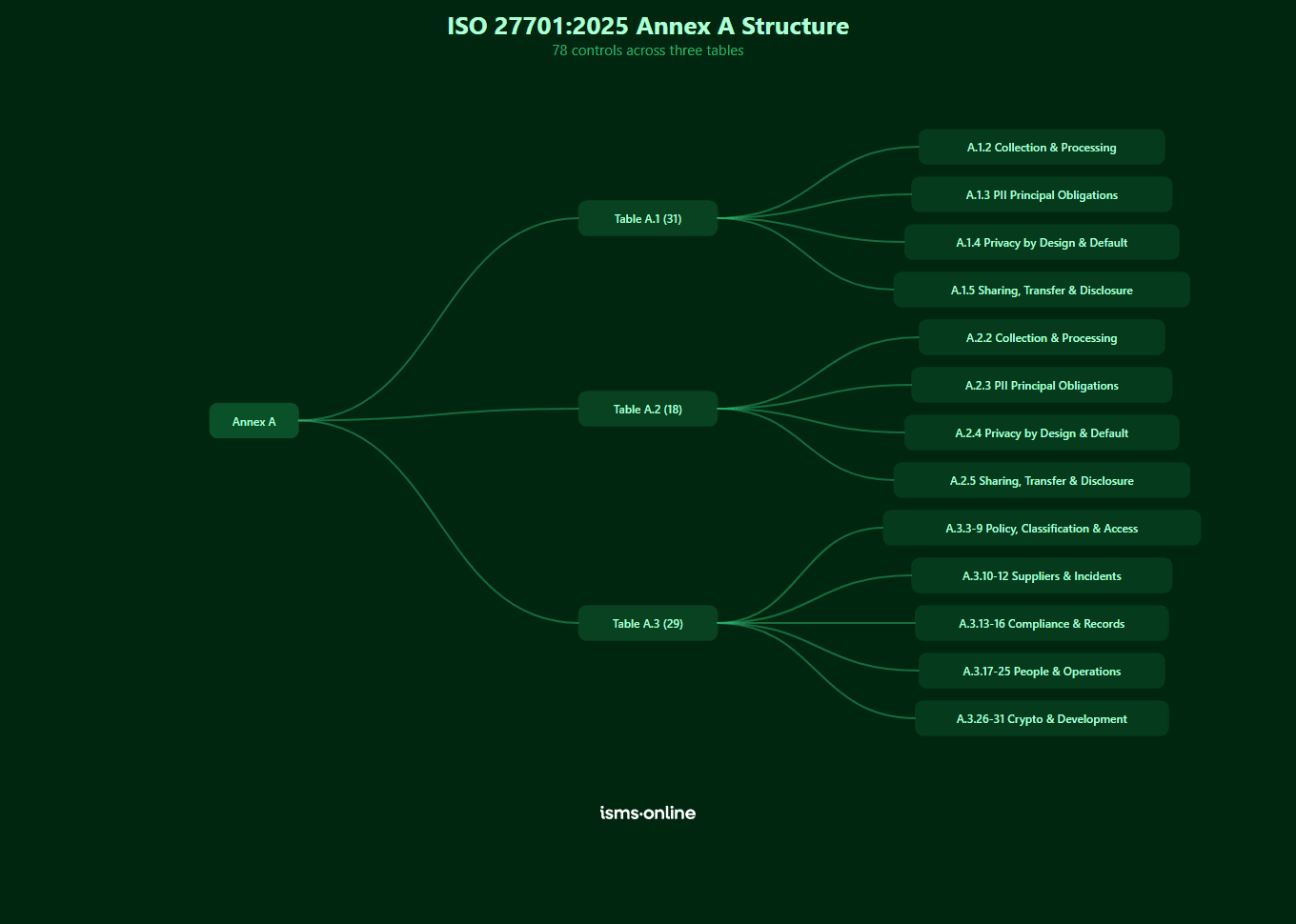
Annex A is normative, meaning its controls are requirements (not optional guidance). It is organised into three tables based on the organisation’s role in processing personally identifiable information (PII):
| Table | Applies to | Controls | Focus areas |
|---|---|---|---|
| Table A.1 | PII controllers | 31 | Lawful basis, consent, PII principal rights, privacy by design, data transfers |
| Table A.2 | PII processors | 18 | Customer agreements, processing purposes, subcontractor management, disclosures |
| Table A.3 | Both controllers and processors | 29 | Information security policies, access control, incident management, cryptography, development security |
Every Annex A control has corresponding implementation guidance in Annex B (e.g. guidance for control A.1.2.2 Identify and Document Purpose is found in B.1.2.2). Organisations must include all applicable controls in their statement of applicability, with justification for any exclusions [Clause 6.1.3 e)].
What does Table A.1 cover? (PII controller controls)
Table A.1 contains 31 controls grouped into four objectives. These apply to any organisation that determines the purposes and means of PII processing.
Conditions for collection and processing (A.1.2)
Objective: To demonstrate that processing is lawful, with a legal basis per applicable jurisdictions, and with clearly defined and legitimate purposes.
| Control | Title |
|---|---|
| A.1.2.2 Identify and Document Purpose | Identify and document purpose |
| A.1.2.3 Identify Lawful Basis | Identify lawful basis |
| A.1.2.4 Determine Consent | Determine when and how consent is to be obtained |
| A.1.2.5 Obtain and Record Consent | Obtain and record consent |
| A.1.2.6 Privacy Impact Assessment | Privacy impact assessment |
| A.1.2.7 Contracts with PII Processors | Contracts with PII processors |
| A.1.2.8 Joint PII Controller | Joint PII controller |
| A.1.2.9 Records of Processing PII | Records related to processing PII |
Obligations to PII principals (A.1.3)
Objective: To ensure PII principals are provided with appropriate information about the processing of their PII and to meet any other applicable obligations.
| Control | Title |
|---|---|
| A.1.3.2 Obligations to PII Principals | Determining and fulfilling obligations to PII principals |
| A.1.3.3 Information for PII Principals | Determining information for PII principals |
| A.1.3.4 Providing Information | Providing information to PII principals |
| A.1.3.5 Modify or Withdraw Consent | Providing mechanism to modify or withdraw consent |
| A.1.3.6 Object to PII Processing | Providing mechanism to object to PII processing |
| A.1.3.7 Access, Correction or Erasure | Access, correction or erasure |
| A.1.3.8 Inform Third Parties | PII controllers’ obligations to inform third parties |
| A.1.3.9 Providing Copy of PII | Providing copy of PII processed |
| A.1.3.10 Handling Requests | Handling requests |
| A.1.3.11 Automated Decision Making | Automated decision making |
Privacy by design and privacy by default (A.1.4)
Objective: To ensure that processes and systems are designed such that the collection and processing of PII are limited to what is necessary for the identified purpose.
| Control | Title |
|---|---|
| A.1.4.2 Limit Collection | Limit collection |
| A.1.4.3 Limit Processing | Limit processing |
| A.1.4.4 Accuracy and Quality | Accuracy and quality |
| A.1.4.5 PII Minimisation | PII minimization objectives |
| A.1.4.6 De-identification and Deletion | PII de-identification and deletion at the end of processing |
| A.1.4.7 Temporary Files | Temporary files |
| A.1.4.8 Retention | Retention |
| A.1.4.9 Disposal | Disposal |
| A.1.4.10 PII Transmission Controls | PII transmission controls |
PII sharing, transfer and disclosure (A.1.5)
Objective: To determine whether, and document when, PII is shared, transferred or disclosed in accordance with applicable obligations.
| Control | Title |
|---|---|
| A.1.5.2 Basis for PII Transfer | Identify basis for PII transfer between jurisdictions |
| A.1.5.3 Countries for PII Transfer | Countries and international organizations to which PII can be transferred |
| A.1.5.4 Records of PII Transfer | Records of transfer of PII |
| A.1.5.5 Records of PII Disclosures | Records of PII disclosures to third parties |

Get started easily with a personal product demo
One of our onboarding specialists will walk you through our platform to help you get started with confidence.

What does Table A.2 cover? (PII processor controls)
Table A.2 contains 18 controls grouped into four objectives. These apply to any organisation that processes PII on behalf of a PII controller.
Conditions for collection and processing (A.2.2)
| Control | Title |
|---|---|
| A.2.2.2 Customer Agreement | Customer agreement |
| A.2.2.3 Organisation Purposes | Organization’s purposes |
| A.2.2.4 Marketing and Advertising | Marketing and advertising use |
| A.2.2.5 Infringing Instruction | Infringing instruction |
| A.2.2.6 Customer Obligations | Customer obligations |
| A.2.2.7 Records of Processing PII | Records related to processing PII |
Obligations to PII principals (A.2.3)
| Control | Title |
|---|---|
| A.2.3.2 Obligations to PII Principals | Comply with obligations to PII principals |
Privacy by design and privacy by default (A.2.4)
| Control | Title |
|---|---|
| A.2.4.2 Temporary Files | Temporary files |
| A.2.4.3 Return, Transfer or Disposal | Return, transfer or disposal of PII |
| A.2.4.4 PII Transmission Controls | PII transmission controls |
PII sharing, transfer and disclosure (A.2.5)
| Control | Title |
|---|---|
| A.2.5.2 Basis for PII Transfer | Basis for PII transfer between jurisdictions |
| A.2.5.3 Countries for PII Transfer | Countries and international organizations to which PII can be transferred |
| A.2.5.4 Records of PII Disclosures | Records of PII disclosures to third parties |
| A.2.5.5 PII Disclosure Requests | Notification of PII disclosure requests |
| A.2.5.6 Legally Binding Disclosures | Legally binding PII disclosures |
| A.2.5.7 Disclosure of Subcontractors | Disclosure of subcontractors used to process PII |
| A.2.5.8 Engaging Subcontractors | Engagement of a subcontractor to process PII |
| A.2.5.9 Change of Subcontractor | Change of subcontractor to process PII |
What does Table A.3 cover? (Shared security controls)
Table A.3 contains 29 controls that apply to both PII controllers and PII processors. These are information security controls with specific PII processing requirements.
| Control | Title |
|---|---|
| A.3.3 Information Security Policies | Policies for information security |
| A.3.4 Security Roles | Information security roles and responsibilities |
| A.3.5 Classification of Information | Classification of information |
| A.3.6 Labelling of Information | Labelling of information |
| A.3.7 Information Transfer | Information transfer |
| A.3.8 Identity Management | Identity management |
| A.3.9 Access Rights | Access rights |
| A.3.10 Supplier Agreements | Addressing information security within supplier agreements |
| A.3.11 Incident Management | Information security incident management planning and preparation |
| A.3.12 Security Incident Response | Response to information security incidents |
| A.3.13 Legal and Regulatory Requirements | Legal, statutory, regulatory and contractual requirements |
| A.3.14 Protection of Records | Protection of records |
| A.3.15 Independent Review | Independent review of information security |
| A.3.16 Compliance with Policies | Compliance with policies, rules and standards for information security |
| A.3.17 Security Awareness and Training | Information security awareness, education and training |
| A.3.18 Confidentiality Agreements | Confidentiality or non-disclosure agreements |
| A.3.19 Clear Desk and Clear Screen | Clear desk and clear screen |
| A.3.20 Storage Media | Storage media |
| A.3.21 Secure Disposal of Equipment | Secure disposal or re-use of equipment |
| A.3.22 User Endpoint Devices | User endpoint devices |
| A.3.23 Secure Authentication | Secure authentication |
| A.3.24 Information Backup | Information backup |
| A.3.25 Logging | Logging |
| A.3.26 Use of Cryptography | Use of cryptography |
| A.3.27 Secure Development Life Cycle | Secure development life cycle |
| A.3.28 Application Security | Application security requirements |
| A.3.29 Secure System Architecture | Secure system architecture and engineering principles |
| A.3.30 Outsourced Development | Outsourced development |
| A.3.31 Test Information | Test information |

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

How do Annex A and Annex B work together?
Annex A defines the control objectives and control statements (the “what”). Annex B provides implementation guidance (the “how”). Each Annex A control has a matching Annex B clause with the same numbering:
- Control A.1.2.2 Identify and Document Purpose (Identify and document purpose) → Guidance at B.1.2.2
- Control A.2.2.2 Customer Agreement (Customer agreement) → Guidance at B.2.2.2
- Control A.3.3 Information Security Policies (Policies for information security) → Guidance at B.3.3
When implementing a control, read both the Annex A requirement and the Annex B guidance together. Annex B is classified as normative, though it uses ‘should’ language rather than ‘shall’, but auditors will expect your implementation to be consistent with its intent.
How does Annex A relate to other annexes?
The standard includes four additional mapping annexes that connect Annex A controls to external frameworks:
- Annex C — Maps controls to the 11 privacy principles in ISO/IEC 29100
- Annex D — Maps controls to GDPR articles (Articles 5–35 and 44–49)
- Annex E — Maps controls to ISO/IEC 27018 (cloud processors) and ISO/IEC 29151 (PII protection)
- Annex F — Maps 2025 controls to ISO 27701:2019 equivalents
These mappings are informative (not normative), but they are invaluable for organisations that need to demonstrate compliance with multiple frameworks simultaneously.
Why choose ISMS.online for ISO 27701:2025 Annex A?
ISMS.online gives you a structured, auditable way to implement every Annex A control:
- Pre-built control sets — All 78 controls mapped and ready for your statement of applicability
- Evidence linking — Attach policies, risk assessments, audit results and records directly to each control
- Role-based views — Filter controls by your role (controller, processor or both) so you see only what applies
- Gap tracking — Mark each control as implemented, partially implemented or not applicable with justification
- Cross-framework mapping — See how each control maps to GDPR, ISO 27001 and other frameworks you operate
- Audit-ready exports — Generate your statement of applicability and evidence packs for external auditors
FAQs
Do I need to implement all 78 Annex A controls?
Not necessarily. You must include all controls that are applicable to your role (controller, processor or both) in your statement of applicability. Any exclusions must be justified. Controls may be excluded where they are not deemed necessary by your risk assessment or where they are not required by applicable legal requirements.
What is the difference between Annex A and Annex B?
Annex A contains the control objectives and control statements (the requirements). Annex B provides implementation guidance for each control. Annex A is normative (mandatory); Annex B guidance is normative and uses ‘should’ language to provide implementation recommendations that auditors expect to see addressed.
How do I know which table applies to my organisation?
If you determine the purposes and means of PII processing, Table A.1 (controller controls) applies. If you process PII on behalf of another organisation, Table A.2 (processor controls) applies. Table A.3 (shared controls) applies to both roles. Many organisations act as both controllers and processors for different processing activities.
How do the 2025 controls map to the 2019 edition?
Annex F provides a complete correspondence table in both directions. Table F.1 maps 2025 controls to their 2019 equivalents. Table F.2 maps 2019 controls to their 2025 equivalents. See our Annex F correspondence guide for the full mapping.









