How long does Cyber Essentials take to get in the UK?
The honest answer is that Cyber Essentials typically takes between two and eight weeks end to end, with the average UK business landing in the four to six week range. If your technical controls are already in good shape and a dedicated owner runs the project, certification can be achieved in as little as three to five working days. If your environment is messy or scope is unclear, the timeline can stretch well beyond eight weeks.
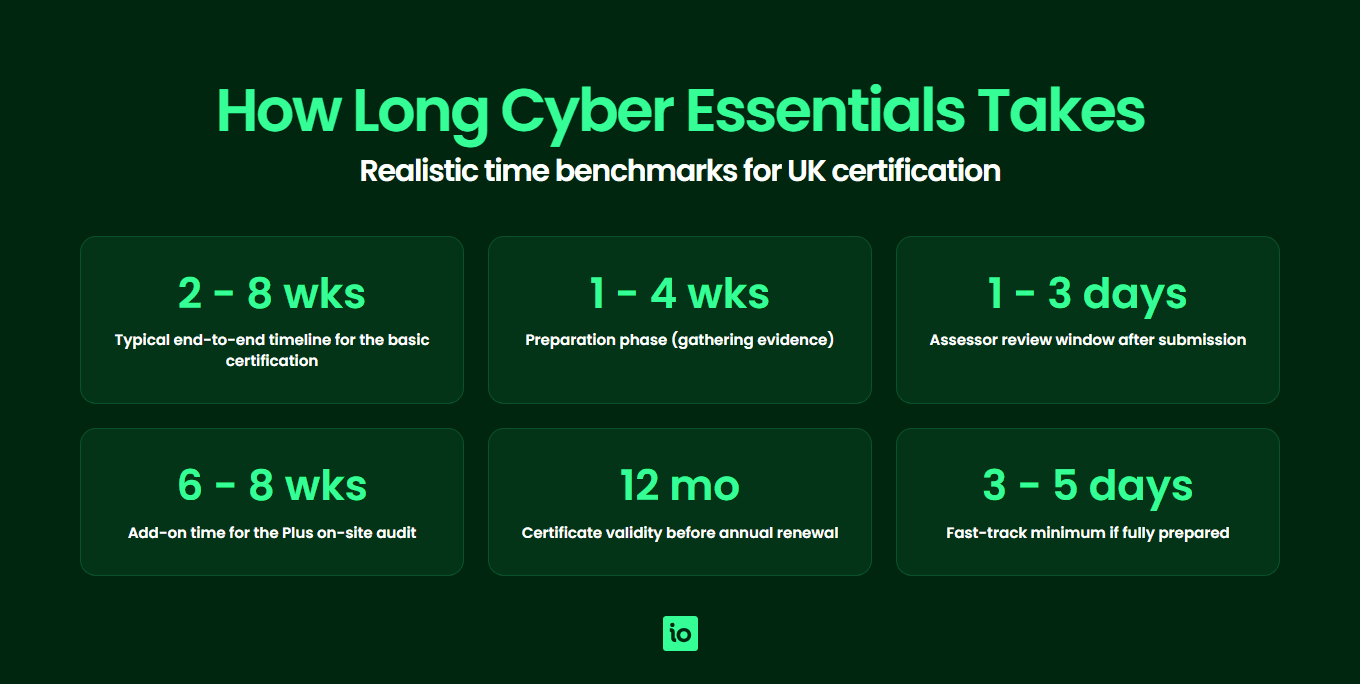
Most of that variation sits in the preparation phase rather than the assessment itself. Once your self-assessment questionnaire is submitted to an IASME-accredited certification body, the assessor review is usually completed within one to three working days, and the certificate is normally issued within 24 hours of a pass. The real question is how long it takes you to get ready to submit with confidence.
This guide breaks the journey down phase by phase, explains how Cyber Essentials Plus requirements add a separate audit window of four to six weeks on top, and shows the practical factors that either accelerate or stall UK businesses working back from a contract or tender deadline.
What does the phase breakdown actually look like?
Cyber Essentials is a self-assessment scheme governed by the NCSC and delivered through IASME and its network of certification bodies. The certification is a single questionnaire, but the work behind it falls into five clearly distinct phases.
Phase 1: Preparation and scoping (1 to 4 weeks)
This is where almost all of the variability lives. You need to define the boundary of certification (whole organisation or a sub-set), inventory in-scope devices, cloud services and users, and verify that the five technical controls (firewalls, secure configuration, user access control, malware protection and security update management) are in place across every asset. Most delays in Cyber Essentials projects originate here, not in assessment.
Phase 2: Questionnaire completion and submission (1 to 2 days)
Once preparation is complete, the actual Cyber Essentials self-assessment questionnaire takes a competent owner roughly half a day to a full day to complete. Submission is electronic via the certification body’s portal and is normally instantaneous.
Phase 3: Assessor review (1 to 3 working days)
An IASME-accredited assessor reviews every answer against the published Cyber Essentials requirements. They will either issue a pass, ask clarifying questions, or flag specific controls as non-compliant. Most assessors aim to complete a first review within two working days, although demand peaks (typically late spring and end of financial year) can extend this.
Phase 4: Remediation if needed (variable, often 1 to 3 weeks)
If the assessor flags issues, you are given a window (commonly two working days under the standard scheme, longer under some certification bodies’ resubmission terms) to either supply additional evidence or fix the underlying problem. Genuine remediation, especially patching unsupported software or rolling out multi-factor authentication, can take longer than the assessment itself.
Phase 5: Certificate issuance (under 24 hours after pass)
Once the assessor confirms a pass, your certificate and badge are issued electronically, usually within the same working day. You are listed on the public IASME certificate search and can immediately use the certification for tenders, insurance applications and public sector procurement.

Start your free trial
Want to explore?
Sign up for your free trial today and get hands on with all the compliance features that ISMS.online has to offer

What is the typical Cyber Essentials timeline by phase?
The table below summarises the typical duration of each phase for a UK SME aiming for basic Cyber Essentials certification. Use it to plan backwards from your contract or tender deadline.
| Phase | Fast-track (prepared) | Typical SME | Slow (messy environment) |
|---|---|---|---|
| 1. Preparation and scoping | 1 to 2 days | 2 to 3 weeks | 4 to 8 weeks |
| 2. Questionnaire completion | Half a day | 1 day | 2 to 3 days |
| 3. Assessor review | 1 to 2 working days | 2 to 3 working days | 3 to 5 working days |
| 4. Remediation (if needed) | None | 2 to 5 working days | 1 to 3 weeks |
| 5. Certificate issuance | Same day | Within 1 working day | Within 1 working day |
| End-to-end total | 3 to 5 working days | 4 to 6 weeks | 8 to 12 weeks |
These ranges are deliberately realistic rather than aspirational. Plenty of certification bodies advertise “Cyber Essentials in 24 hours”, and that is technically possible — but only if you arrive with a clean, in-scope environment, complete evidence and an experienced owner. For most UK businesses doing this for the first time, plan for four to six weeks and treat anything faster as a bonus.
What factors speed up Cyber Essentials certification?
If you need to compress the timeline, the levers that move the needle most are environmental and organisational, not procedural. The questionnaire itself cannot be made shorter; the work to be ready for it absolutely can.
- Pre-existing security controls — If you already enforce strong passwords, MFA, automatic patching and endpoint malware protection through Group Policy, Intune or equivalent, much of the questionnaire becomes a documentation exercise rather than a remediation project.
- Mobile device management and single sign-on in place — MDM tools (Intune, Jamf, Kandji) and SSO providers (Microsoft Entra ID, Google Workspace, Okta) give you instant, defensible evidence of secure configuration and access control across every device and user.
- A clear and bounded scope — A whole-organisation scope is simpler to defend than a carved-out sub-scope with network segmentation. If you can certify the whole business, do.
- A dedicated owner with authority — Projects with a single named owner who can make decisions about scope, evidence and budget consistently finish faster than projects spread across IT, security and compliance.
- An experienced certification body — Established IASME-accredited assessors review faster and ask sharper, more useful questions when something is unclear.
- A compliance platform doing the heavy lifting — A platform that maps your evidence to the five controls, tracks gaps and stores responses centrally avoids the classic spreadsheet-and-email scramble that loses days at a time.
What slows Cyber Essentials certification down?
Equally, there are well-known stalling factors. Recognising these early means you can either address them or build them into your timeline from the start.
- Unsupported software still in use — Out-of-support operating systems, browsers or applications fail Cyber Essentials outright. Either remove them from scope (via segmentation) or upgrade — both take time.
- Untrained users and inconsistent practices — If half the team has admin rights they should not have, or password practices vary by department, expect remediation before you can submit.
- BYOD without a clear policy — Personal devices accessing organisational data are in scope. Without an MDM-enforced policy or a defensible carve-out, BYOD will block certification.
- Cloud services without a proper inventory — Shadow IT and uncatalogued SaaS apps make the questionnaire genuinely hard to answer truthfully and increase the risk of an assessor finding.
- Last-minute submission ahead of a tender deadline — Submitting with unresolved issues to “see what comes back” almost always costs more time than fixing the issues first.
- Misunderstanding scope — Treating Cyber Essentials as an IT-only project and forgetting cloud admin accounts, contractors or remote workers leads to late rescoping and resubmission.

Get started easily with a personal product demo
One of our onboarding specialists will walk you through our platform to help you get started with confidence.

How long does Cyber Essentials Plus take on top?
Cyber Essentials Plus is the audited tier of the scheme. It uses the same five controls and the same questionnaire, but adds a hands-on technical audit conducted by an IASME-accredited assessor. The audit involves sampling devices, running authenticated vulnerability scans, testing malware protection, validating MFA and confirming that what the questionnaire claims is true in practice.
You should plan for an additional four to six weeks on top of basic Cyber Essentials, broken down roughly as:
- Scheduling the audit — Most certification bodies need one to three weeks of lead time, especially for on-site or hybrid audits.
- Audit itself — One to three working days depending on device sample size and complexity.
- Remediation of audit findings — Up to 30 days under the IASME scheme to fix anything the assessor identifies.
- Final sign-off and Plus certificate issuance — Within a few working days of remediation being verified.
You must hold a valid basic Cyber Essentials certificate at the point your Plus certificate is issued, and the Plus audit must be completed within three months of your basic certification date. That window is non-negotiable, so it is worth booking the Plus audit at the same time you start the basic certification process.
How long does a Cyber Essentials certification last?
A Cyber Essentials certificate is valid for 12 months from the date of issue. There is no mid-term surveillance audit; once you have it, you have it for a full year. To maintain continuous certification you must renew before the expiry date by completing a fresh self-assessment that reflects your current environment.
The renewal questionnaire is not lighter than the original, and the requirements update annually (the question set is reviewed by IASME and the NCSC every year). The practical implication is that the controls you needed to pass last year may not be sufficient this year — for example, MFA requirements and bring-your-own-device rules have tightened in recent annual updates. Treat renewal as a deliberate exercise rather than a copy-paste. The detailed mechanics are covered in our guide to Cyber Essentials renewal.
Costs scale with organisation size and are tier-based; see our breakdown of the cost of Cyber Essentials certification for the current IASME fee bands.
What are the most common Cyber Essentials timeline mistakes?
Working with thousands of UK organisations going through the scheme, the same mistakes show up again and again. Avoid these and you avoid most of the surprise delays.
- Waiting until the last minute — Starting the project two weeks before a tender deadline almost guarantees a failed first submission. Build in a six-week buffer minimum.
- Underestimating scope — Forgetting cloud services, remote workers, contractors or personal devices in scope leads to late discovery and rescoping.
- Weak or missing evidence — Answering “yes” to a question without being able to back it up with policy, configuration or logs invites assessor follow-up and slows the review.
- Treating it as paperwork — Cyber Essentials checks reality, not documentation. If the technical controls are not genuinely in place, the assessor will find out.
- Choosing the wrong certification body for your timing — Some bodies have multi-week backlogs at peak times. Confirm assessor availability before you commit to a deadline.
- Ignoring annual updates — The requirements change every year. Using last year’s answers without rechecking them against the current question set will trip you up at renewal.
The simplest way to avoid the first three is to work through our Cyber Essentials checklist before booking your assessment slot.
Why Choose ISMS.online for Faster Cyber Essentials Certification?
- Pre-mapped to all five controls — ISMS.online ships with the Cyber Essentials question set already aligned to your evidence, so you are not building a checklist from scratch.
- Centralised evidence library — Every policy, configuration screenshot, MDM export and screenshot lives in one place, ready to attach to the right control instantly — not scattered across drives and inboxes.
- Real-time gap visibility — A live dashboard shows which controls are green, amber and red so you know exactly what remains before submission rather than discovering surprises during assessor review.
- Multi-framework reuse — The same evidence supports ISO 27001, SOC 2 and NIS 2 so the time you invest in Cyber Essentials is not wasted when the next framework arrives.
- Assured Results Method — A proven implementation methodology that consistently shortens the path to certification by structuring the work, not just storing it.
- Collaborative workspace for owners and assessors — Assign questions, leave comments, track who answered what and present a clean evidence trail to the certification body in a fraction of the time it takes via email.
- Built for UK SMEs — ISMS.online is a UK-headquartered platform used by thousands of organisations to achieve compliance faster, with UK-based support.
Related Cyber Essentials guides
Continue your Cyber Essentials journey with the other guides in this series:
- Cyber Essentials Requirements — The five control areas, scope decisions and what evidence assessors look for.
- Cyber Essentials Cost — IASME pricing tiers, Plus costs, hidden costs and 3-year totals for UK businesses.
- Is Cyber Essentials Worth It? — An honest assessment of the benefits, drawbacks and who actually needs certification.
- Cyber Essentials Plus Requirements — The technical audit, vulnerability scans and what Plus delivers over the basic certification.
- Cyber Essentials Self Assessment — The SASQ workflow, scope, evidence and common pitfalls.
- Cyber Essentials Renewal — The 12-month cycle, 2026 control changes and how to prepare 60 days out.
- Cyber Essentials for Small Business — SMB-specific pricing, scope and the cost-benefit case.
- Cyber Essentials vs ISO 27001 — Scope, cost, time and recognition compared.
FAQs
How quickly can you realistically get Cyber Essentials?
If every one of the five technical controls is already in place, your scope is clear and a dedicated owner is driving the project, you can submit, be reviewed and receive your certificate in three to five working days. For a typical UK SME going through the scheme for the first time, four to six weeks is a more realistic plan.
How long does a Cyber Essentials certificate last?
Twelve months from the date of issue. There is no mid-cycle audit, but to remain continuously certified you must complete a fresh self-assessment and pass it before the certificate expires.
How long does Cyber Essentials Plus take compared to basic Cyber Essentials?
Plus adds roughly four to six weeks on top of basic Cyber Essentials to account for audit scheduling, the audit itself (one to three working days), any remediation of findings (up to 30 days under the IASME scheme) and final sign-off. The Plus audit must be completed within three months of your basic certification date.
What happens if I fail my Cyber Essentials assessment?
You are normally given a short window (typically two working days under the standard IASME scheme, longer under some certification bodies) to address the issues and resubmit. If you cannot remediate in that window, you may need to start a fresh submission, which extends the timeline. ISMS.online helps prevent this by surfacing gaps before you submit rather than after.
Can I get Cyber Essentials and ISO 27001 at the same time?
Yes, and many UK organisations do. Cyber Essentials is a useful early milestone on the path to ISO 27001 because the five technical controls overlap heavily with ISO 27001 Annex A. Running both in parallel on a single evidence base in ISMS.online avoids duplicate work.
Is the Cyber Essentials questionnaire actually difficult?
The questions are not technically complex, but answering them honestly and with evidence requires you to understand exactly what is in scope and how each of the five controls is implemented. The difficulty is operational, not intellectual — which is why a clear scope, a single owner and a structured platform make such a difference to the timeline.









