What is Cyber Essentials Plus and how is it different from basic Cyber Essentials?
Cyber Essentials Plus is the higher tier of the UK Government’s Cyber Essentials scheme, administered by the National Cyber Security Centre (NCSC) and delivered through IASME and its network of certification bodies. It covers the same five technical control areas as the basic certification, but with one critical difference: an independent assessor verifies that the controls are actually in place and working on your live systems, rather than relying on a self-assessment questionnaire.
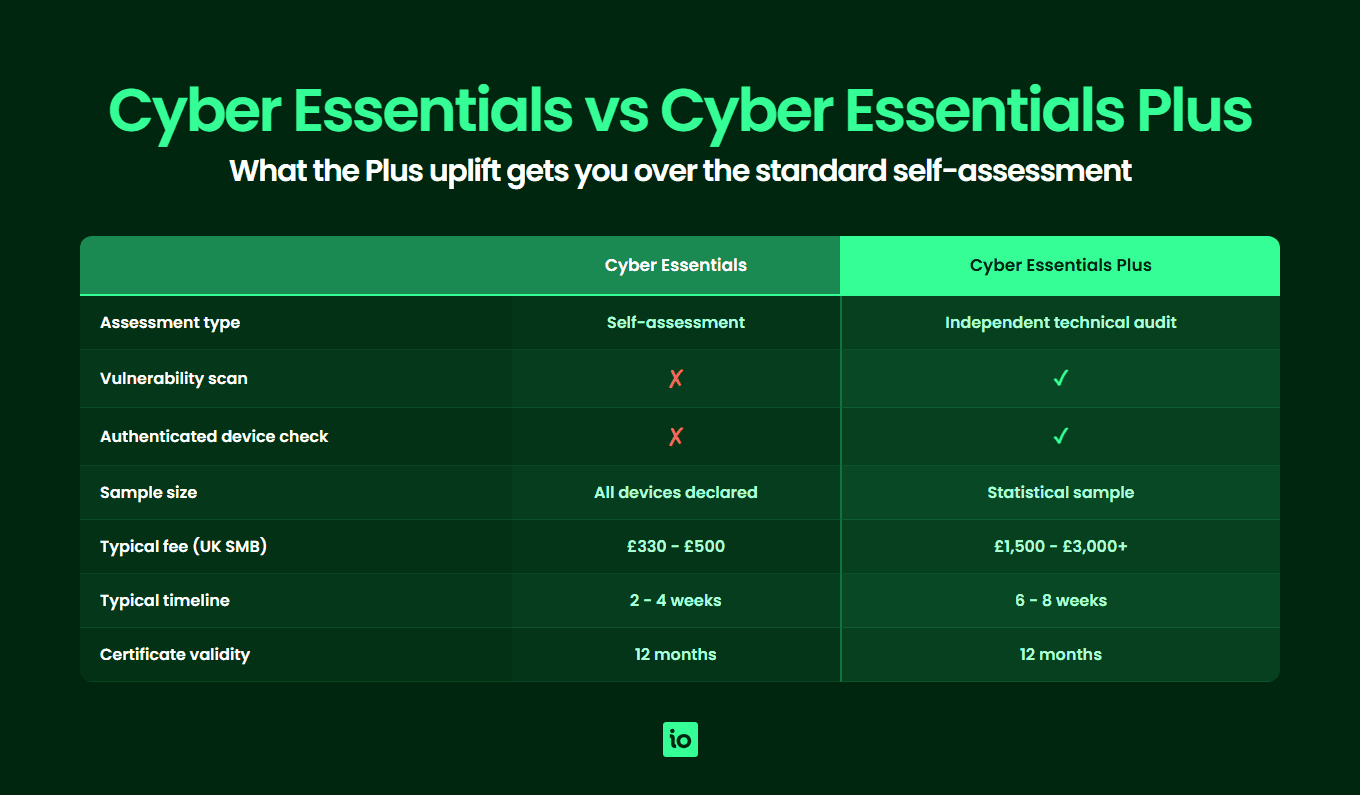
Basic Cyber Essentials is a self-assessed certification. You answer roughly eighty questions about how your organisation handles firewalls, secure configuration, user access, malware protection and security update management, and a qualified assessor reviews your answers. It is fast, affordable and well suited to smaller organisations that want a recognised baseline.
Cyber Essentials Plus takes that same baseline and adds an independent technical audit. A trained assessor connects to a sample of your devices, runs vulnerability scans, attempts to deliver simulated malware to test endpoint defences, and inspects configuration evidence directly. It is the assurance level UK Government departments, the Ministry of Defence (MOD) and NHS suppliers increasingly require from their supply chain, and it is becoming a standard expectation in enterprise procurement processes for any supplier handling sensitive data.
For a side-by-side breakdown of the two tiers, see our Cyber Essentials self assessment guide. If you are weighing Cyber Essentials Plus against a broader information security framework, our Cyber Essentials vs ISO 27001 comparison explains how the two complement each other. Before booking the audit, work through our Cyber Essentials checklist to confirm every control area is genuinely in place — Plus failures usually trace back to a single gap that a readiness check would have caught.
What are the five control areas reviewed under Cyber Essentials Plus?
The Cyber Essentials Plus audit reviews the same five technical control areas as the basic scheme, but with hands-on verification on your actual systems rather than a paper-based attestation. The auditor will not take your word for it — they will check.
1. Firewalls and internet gateways
The assessor confirms that every device in scope (including home and remote workers’ laptops) is protected by a correctly configured firewall. Default administrative passwords on boundary firewalls must be changed, unauthenticated inbound connections must be blocked by default, and any rule that permits inbound traffic must be documented with a business justification. Software firewalls on user devices are checked to confirm they are enabled and configured.
2. Secure configuration
Systems must be hardened from their out-of-the-box state. The auditor checks that unused software and services have been removed or disabled, default and guest accounts are disabled, and auto-run features are switched off on user devices. Devices that connect to corporate data must enforce a screen lock and credential requirements. The auditor will inspect representative devices and confirm the configuration against your build standard.
3. User access control
Access must be granted on a least-privilege basis. The auditor will verify that user accounts are created through a formal approval process, administrative privileges are separated from day-to-day accounts, and multi-factor authentication (MFA) is enforced on all cloud services and on administrative access. Accounts for leavers must be promptly disabled, and the assessor may sample joiner-mover-leaver records to test the process.
4. Malware protection
Every device in scope must run anti-malware software, application allow-listing, or operate in a sandboxed environment such as a managed mobile device profile. The auditor will attempt to deliver test malware samples (typically the EICAR test file and inert variants) by email and web download to confirm that endpoint protection actually detects and blocks threats in practice, not just on paper.
5. Security update management
All operating systems and high-risk software (browsers, email clients, office suites, PDF readers) must be vendor-supported and patched within fourteen days of a security update being released, when the update addresses a vulnerability rated high or critical. The auditor will run an authenticated vulnerability scan against sampled devices to confirm that no in-scope system is missing a qualifying patch, and that no end-of-life software is in use.
The full technical specification is maintained by NCSC and IASME and is updated periodically. For a deeper walk-through of each control, see our Cyber Essentials requirements guide.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

What does the Cyber Essentials Plus audit actually involve?
The Cyber Essentials Plus audit is a structured, evidence-based assessment carried out by a qualified assessor from an IASME-accredited certification body. The audit follows a defined test specification and is normally completed remotely, although on-site visits are sometimes used for larger or more complex estates. There are five distinct technical tests.
External vulnerability scan
The assessor runs an authenticated and unauthenticated scan of every internet-facing IP address in scope. The scan looks for missing patches, insecure services, misconfigured boundary devices and exposed administrative interfaces. Any vulnerability with a CVSS v3 score of 7.0 or above is treated as a fail unless it can be demonstrated as a false positive.
Internal authenticated vulnerability scan
A sample of end-user devices is scanned with credentialed access, allowing the tool to enumerate installed software, missing patches and configuration weaknesses. As with the external scan, high or critical vulnerabilities are a fail. This is the test that most commonly catches organisations out, because it surfaces unpatched browser plug-ins, outdated PDF readers and older versions of office software that often slip through informal patching processes.
Simulated malware delivery via email
The assessor sends a series of test files (a mix of harmless EICAR samples and password-protected archives containing inert payloads) to a user mailbox. The expected behaviour is that the email security gateway, the mail client and the endpoint anti-malware engine combine to block or quarantine each sample. Any file that reaches the inbox and can be executed counts as a fail.
Simulated malware delivery via web browsing
Test files are hosted on a controlled web server and the assessor attempts to download them through a sampled device’s browser. The endpoint protection must prevent execution. The test also verifies that browsers are configured to block known-malicious sites and that any default download behaviours are sensible.
Configuration and account review
Beyond the automated scans, the assessor will inspect sampled devices interactively to confirm screen-lock policies, MFA enforcement, admin account separation, removal of unsupported software and the absence of default credentials on networking equipment.
How many devices does the auditor sample?
The sample size is defined by the IASME test specification and scales with the size of the estate. Larger organisations are not audited end-to-end on every device, but a statistically meaningful sample is chosen across each device type and operating system.
| In-scope device count | Sample size per device type | Notes |
|---|---|---|
| 1 — 10 | All devices | Every in-scope device is tested |
| 11 — 50 | 10 devices or 20%, whichever is greater | Sample stratified across operating systems and device roles |
| 51 — 200 | 15 devices per type | Includes a mix of corporate and BYOD where applicable |
| 201+ | Defined by assessor, minimum 20 per type | Sample agreed up front and recorded in the audit plan |
The sample must cover every operating system, every build type (corporate, contractor, BYOD) and every role profile (standard user, admin, developer). A single failure on a sampled device is treated as a failure of the population, so consistent build standards across the estate are critical.
What evidence will the auditor request before testing begins?
Before any scans run, the assessor will issue a scoping pack and a pre-audit evidence request. Getting this pack ready in advance is the single biggest lever for a smooth audit. Typical evidence includes:
- Asset inventory — A complete list of in-scope devices (servers, end-user devices, mobile devices), with hostnames, operating system versions and physical location or owner
- Network diagram — Showing internet gateways, internal segmentation and any cloud services in scope
- Build standards — Documented configuration baselines for each operating system in use
- Patch management policy and evidence — Including the most recent month’s patching report
- Joiner-mover-leaver records — For a sample of recent starters and leavers, evidence that accounts were created and disabled in line with policy
- MFA configuration evidence — Screenshots or admin-console exports confirming MFA enforcement on cloud services and privileged accounts
- Anti-malware coverage report — Confirming every in-scope device is reporting in to the management console
- Firewall rule base — Boundary firewall configuration or rule export, with business justifications for inbound rules
- BYOD policy — If personal devices access corporate data, the policy and the technical controls (typically MDM or app-level containerisation) that enforce it
Organisations that maintain this evidence as a living artefact — rather than scrambling to assemble it in the weeks before the audit — consistently complete Cyber Essentials Plus in the lower end of the typical timeline.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

How much does Cyber Essentials Plus cost in 2026?
Cyber Essentials Plus is materially more expensive than basic Cyber Essentials because of the assessor time required to conduct the technical audit. Pricing varies by certification body and by the size and complexity of the estate, but the indicative ranges below reflect typical 2026 quotes from IASME-accredited bodies in the UK.
| Certification | Typical fee (ex VAT) | What is included |
|---|---|---|
| Basic Cyber Essentials | £330 — £600 | Self-assessment questionnaire, assessor review, certificate valid 12 months. Fee is tiered by headcount band |
| Cyber Essentials Plus (small organisation, up to ~50 devices) | £1,500 — £2,200 | Basic Cyber Essentials plus the technical audit, vulnerability scans and simulated malware tests |
| Cyber Essentials Plus (medium organisation, 50 — 250 devices) | £2,200 — £3,500 | As above, with a larger sample and typically additional assessor days |
| Cyber Essentials Plus (larger or complex estates) | £3,500+ | Bespoke quote — multi-site, multi-OS or significant cloud footprint pushes the price up |
These are direct certification fees only. The real total cost of certification also includes internal effort to prepare evidence, remediate any pre-audit findings, and procure or upgrade tooling (for example MFA on legacy systems, or replacing end-of-life software). For a full breakdown of direct and indirect costs, see our Cyber Essentials cost guide.
How long does Cyber Essentials Plus take from start to finish?
For a well-prepared organisation that already holds basic Cyber Essentials, the Cyber Essentials Plus pathway typically takes six to eight weeks. The basic certification must be in place before the Plus audit can run, and it must be no more than three months old at the point the Plus assessment is booked.
| Stage | Typical duration | What happens |
|---|---|---|
| Scoping and engagement | 1 — 2 weeks | Certification body confirms scope, sample size and audit window. Pre-audit evidence pack issued |
| Evidence preparation and pre-audit remediation | 2 — 4 weeks | You collate evidence, run an internal vulnerability scan and close any high or critical findings before the formal audit |
| Audit fieldwork | 2 — 5 days | Assessor runs external and internal scans, simulated malware tests and configuration review on the sampled devices |
| Findings and remediation | 0 — 4 weeks | Any failures must be remediated and re-tested within the audit window (typically 30 days) |
| Certification issued | 1 week | Once all tests pass, IASME issues the certificate, valid for 12 months |
Organisations that fail the first audit attempt — usually because an authenticated internal scan surfaces a missed patch or an unsupported piece of software — can pay an additional remediation re-test fee rather than restarting the process, provided the issue is closed within thirty days. After the certificate is issued, plan ahead for annual renewal, which requires a fresh audit each year.
Who actually needs Cyber Essentials Plus?
Cyber Essentials Plus is a contractual requirement in a growing number of UK procurement scenarios and a competitive differentiator in many others. The clearest mandates come from the public sector:
- Central government contracts — Cyber Essentials is mandatory for any contract that involves the handling of personal information or the provision of ICT products and services. Plus is required where the contract involves sensitive or personal data at scale
- Ministry of Defence (MOD) — Under the Defence Cyber Protection Partnership (DCPP) and the Cyber Security Model, suppliers handling MOD identifiable information must hold Cyber Essentials Plus as a minimum, with higher-tier projects requiring additional controls
- NHS and health sector suppliers — The Data Security and Protection Toolkit explicitly recognises Cyber Essentials Plus, and many NHS trusts make it a procurement gate for suppliers touching patient data
- Local authorities and public bodies — Increasingly written into tender requirements for any contract involving citizen data or critical services
- Enterprise procurement — Many large private-sector organisations now ask for Cyber Essentials Plus from key suppliers, particularly in financial services, legal, and managed-service provider relationships
- Cyber insurance — Several UK insurers offer reduced premiums or improved cover terms for organisations holding Cyber Essentials Plus, reflecting the lower claims frequency among certified businesses
If your organisation already holds basic Cyber Essentials and is responding to tenders, expect Plus to appear as a requirement within twelve to twenty-four months. Acting before it becomes blocking is significantly cheaper and less disruptive than scrambling to certify against a deadline.
Why Choose ISMS.online for Cyber Essentials Plus?
Preparing for a Cyber Essentials Plus audit is fundamentally an evidence problem. The technical controls are not complex — what trips organisations up is the discipline of keeping configuration, patching and access records continuously audit-ready. ISMS.online helps you achieve and maintain Cyber Essentials Plus certification by turning the underlying control evidence into a living, shared system of record.
- Pre-mapped Cyber Essentials control framework — Every requirement across the five control areas is built into the platform, so you assess against the official scheme without designing your own checklist
- Centralised evidence library — Store firewall rule exports, patch reports, build standards, MFA screenshots and joiner-mover-leaver records against the controls they evidence, so your audit pack assembles itself
- Asset register and scope management — Maintain a single in-scope device inventory, with owners, operating systems and lifecycle status, so the assessor’s sample is straightforward to define
- Policy and procedure templates — Cyber Essentials-aligned policy templates for acceptable use, access control, patching, BYOD and incident response, written for UK businesses and ready to adopt
- Joiner-mover-leaver workflow — Track new starters, role changes and leavers against access decisions, producing the evidence the assessor expects without manual spreadsheet wrangling
- Cross-framework reuse — The same control evidence supports ISO 27001, SOC 2 and other frameworks, so Cyber Essentials Plus becomes a stepping stone to broader certifications rather than a standalone exercise
- Trusted by thousands of UK organisations — ISMS.online supports businesses across the public sector supply chain, professional services, technology and managed-service provider markets on their path to certification
Related Cyber Essentials guides
Continue your Cyber Essentials journey with the other guides in this series:
- Cyber Essentials Requirements — The five control areas, scope decisions and what evidence assessors look for.
- Cyber Essentials Cost — IASME pricing tiers, Plus costs, hidden costs and 3-year totals for UK businesses.
- Is Cyber Essentials Worth It? — An honest assessment of the benefits, drawbacks and who actually needs certification.
- Cyber Essentials Self Assessment — The SASQ workflow, scope, evidence and common pitfalls.
- How Long Does Cyber Essentials Take? — Typical UK timeline, fast-track options and what slows the process.
- Cyber Essentials Renewal — The 12-month cycle, 2026 control changes and how to prepare 60 days out.
- Cyber Essentials for Small Business — SMB-specific pricing, scope and the cost-benefit case.
- Cyber Essentials vs ISO 27001 — Scope, cost, time and recognition compared.
FAQs
Do I need basic Cyber Essentials before I can get Cyber Essentials Plus?
Yes. Cyber Essentials Plus is built on top of the basic self-assessment and the basic certificate must be in place before the Plus audit can run. IASME requires the basic certification to be no more than three months old when the Plus assessment is booked, so most organisations complete the two within a single planned project rather than treating them as separate events.
What happens if we fail part of the Cyber Essentials Plus audit?
A failure on any individual test means the certificate cannot be issued in its current state, but it does not mean starting from scratch. The certification body will record the finding, you remediate the issue (typically a missing patch, an unsupported piece of software, or an MFA gap) and the assessor re-tests the affected control. As long as remediation and re-test are completed within thirty days of the original audit, you avoid a full re-audit and only pay a smaller re-test fee.
Does Cyber Essentials Plus cover cloud services?
Yes. Since 2022 the scheme explicitly includes cloud services in scope where you control the data, the user accounts or the configuration. Infrastructure as a Service (IaaS) and Platform as a Service (PaaS) are always in scope. Software as a Service (SaaS) is in scope where you administer accounts and configure security settings, which applies to most business productivity, identity and collaboration platforms. The auditor verifies MFA enforcement, admin separation and configuration in your tenant, not in the provider’s underlying infrastructure.
Can remote and home workers be included in scope?
Yes — and they must be. Any device that processes corporate data or accesses corporate cloud services is in scope, regardless of where the user works. The auditor expects to see the same firewall, patching, anti-malware and access controls applied to home and remote devices as to office-based ones, with the additional consideration that the home internet router is treated as the boundary device.
How long is Cyber Essentials Plus valid?
The certificate is valid for twelve months from the date of issue. To stay continuously certified you re-audit annually, and many organisations align the renewal with their financial year or with a major procurement cycle. ISMS.online maintains your control evidence continuously between audits, so the renewal becomes a refresh rather than a full restart.
Should I do Cyber Essentials Plus or go straight to ISO 27001?
For most UK organisations the answer is both, in sequence. Cyber Essentials Plus is a focused technical certification that proves your baseline controls work, and it is often a contractual requirement on its own. ISO 27001 is a broader management-system certification that covers governance, risk management and the full information security lifecycle. Plus is faster and cheaper to achieve and gives you most of the technical control evidence ISO 27001 will later expect, so it is a sensible first step on the path to a broader certification.









