ISO 27001 A.5.15 Access Control Checklist
Access control is a fundamental aspect of information security, ensuring that only authorised individuals can access information and associated assets. This control helps minimise the risk of unauthorised access, data breaches, and other security incidents by regulating who can access specific resources and under what conditions.
Key Components of Annex A.5.15
- Policy Definition: Establishing clear access control policies that outline how access rights are determined, granted, and reviewed.
- Role-Based Access Control (RBAC): Implementing RBAC to assign access rights based on roles within the organisation, ensuring that users only have access to the information necessary for their job functions.
- Least Privilege Principle: Ensuring that users have the minimum level of access required to perform their duties, thereby reducing potential security risks.
- Access Control Mechanisms: Utilising technological solutions such as authentication systems, access control lists (ACLs), and physical security measures to enforce access control policies.
- Regular Review and Monitoring: Conducting regular reviews and audits of access rights to ensure compliance with policies and identify any anomalies or unauthorised access attempts.

ISO 27001 made easy
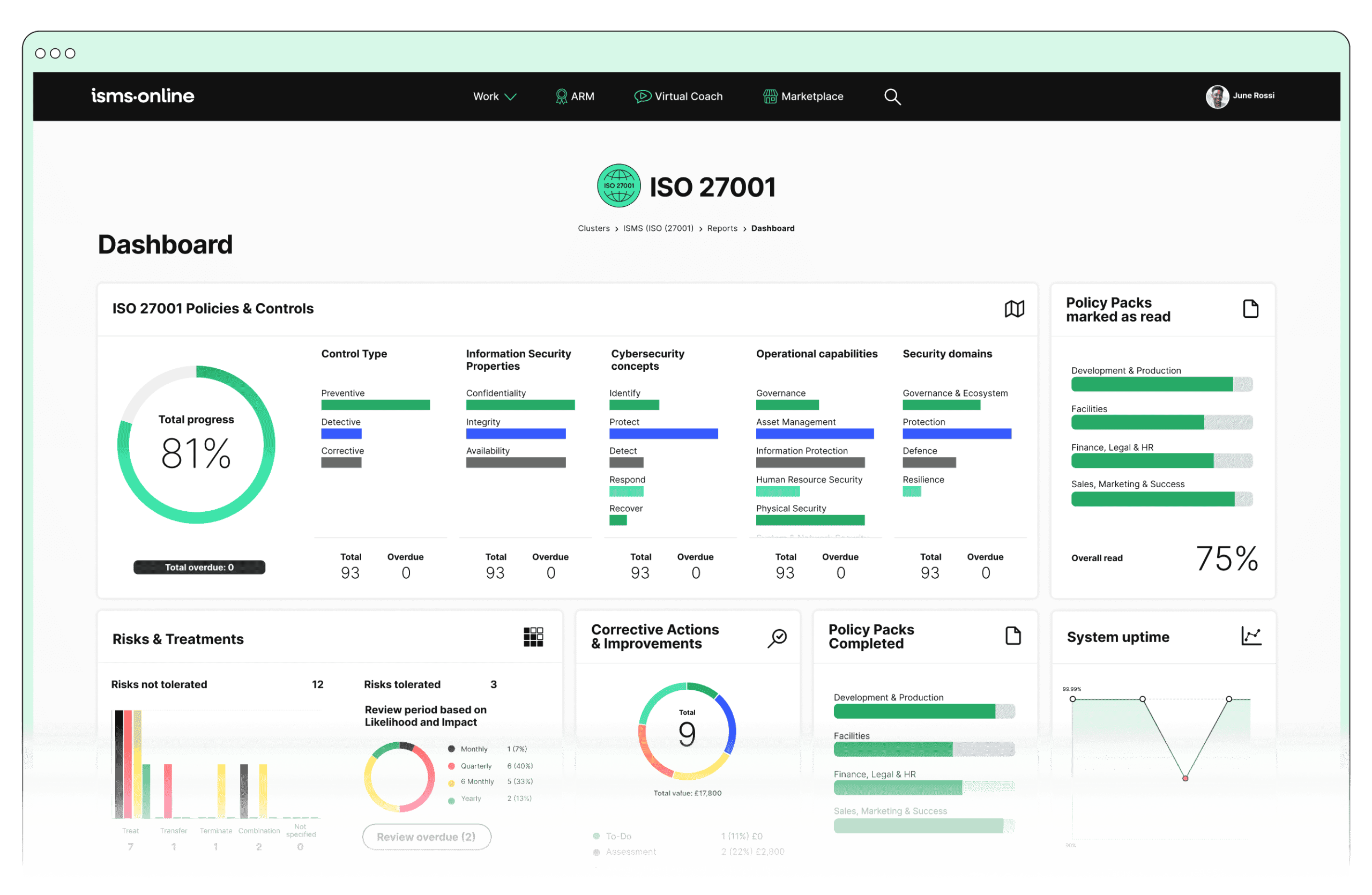
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.5.15? Key Aspects and Common Challenges
1. Develop Access Control Policies:
Common Challenges:
- Policy Alignment: Ensuring policies align with organisational objectives and other regulatory requirements can be complex.
- Stakeholder Buy-In: Gaining approval and buy-in from all stakeholders, including management and employees, can be challenging.
Solutions:
- Policy Alignment: Conduct a thorough context analysis to understand external and internal issues, as well as stakeholder requirements. Use this information to align access control policies with organisational objectives and regulatory requirements.
- Stakeholder Buy-In: Engage stakeholders early in the policy development process. Conduct workshops and provide clear communication on the benefits and necessity of access control policies.
Steps:
- Define and document access control policies, including roles, responsibilities, and procedures for granting, modifying, and revoking access rights.
- Ensure policies are communicated to all relevant stakeholders.
Compliance Checklist:
Associated Clauses: 4.1, 4.2, 5.2, 6.1
2. Implement Access Control Measures:
Common Challenges:
- Technical Integration: Integrating new access control measures with existing IT infrastructure can be technically challenging.
- User Resistance: Users may resist changes, especially if they perceive new measures as cumbersome.
Solutions:
- Technical Integration: Conduct a thorough assessment of existing IT infrastructure and develop a detailed implementation plan. Use pilot programmes to test new access control measures before full-scale deployment.
- User Resistance: Provide training and awareness programmes highlighting the importance of access control and how it protects both the organisation and its employees. Simplify access control processes to minimise user inconvenience.
Steps:
- Use RBAC and the principle of least privilege to assign access rights.
- Implement technical controls such as multi-factor authentication (MFA), password policies, and encryption.
Compliance Checklist:
Associated Clauses: 6.1.2, 6.1.3, 7.2, 8.1
3. Monitor and Audit Access:
Common Challenges:
- Resource Allocation: Allocating sufficient resources for regular monitoring and auditing can be difficult.
- Data Overload: Managing and analysing large volumes of access logs can be overwhelming.
Solutions:
- Resource Allocation: Ensure resource planning includes the necessary personnel and tools for continuous monitoring and auditing. Automate monitoring processes where possible.
- Data Overload: Implement log management solutions and use analytics tools to process and analyse access logs efficiently. Prioritise critical access logs for manual review.
Steps:
- Regularly monitor access logs and conduct audits to detect unauthorised access attempts.
- Review user access rights periodically to ensure they are appropriate and revoke access for users who no longer need it.
Compliance Checklist:
Associated Clauses: 9.1, 9.2, 9.3
4. Training and Awareness:
Common Challenges:
- Engagement: Ensuring high levels of engagement and participation in training programmes can be difficult.
- Relevance: Tailoring training content to be relevant to different roles within the organisation.
Solutions:
- Engagement: Use interactive training methods such as e-learning modules, quizzes, and simulations to increase engagement. Offer incentives for training completion.
- Relevance: Customise training programmes based on the specific roles and responsibilities of employees to ensure the content is relevant and applicable.
Steps:
- Provide training for employees on access control policies and best practices.
- Raise awareness about the importance of safeguarding access credentials.
Compliance Checklist:
Associated Clauses: 7.2, 7.3
5. Response and Improvement:
Common Challenges:
- Incident Response: Developing effective and timely incident response strategies.
- Continuous Improvement: Ensuring continuous improvement based on feedback and incident learnings.
Solutions:
- Incident Response: Establish a clear incident response plan, train employees on their roles within the plan, and conduct regular incident response drills.
- Continuous Improvement: Implement a feedback loop to gather insights from audits, incidents, and training sessions. Use this information to continually refine and improve access control measures.
Steps:
- Establish procedures for responding to access control incidents.
- Continuously improve access control measures based on audit findings and incident reports.
Compliance Checklist:
Associated Clauses: 10.1, 10.2

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.5.15
- Policy Management:
- Policy Templates: Utilise pre-built policy templates to quickly establish access control policies.
- Version Control: Track changes to policies over time, ensuring that the latest versions are always in use.
- Document Access: Control who can view and edit access control policies, maintaining strict oversight.
- User Management:
- Role Definition: Define and manage user roles and associated access rights within the system.
- Access Control: Implement and enforce access control measures, including RBAC and least privilege principles.
- Identity Management: Ensure secure identity verification and management practices are in place.
- Audit Management:
- Audit Templates: Use predefined templates to conduct regular access control audits.
- Audit Plan: Schedule and execute audits, ensuring thorough and regular reviews of access rights.
- Corrective Actions: Document and track corrective actions taken in response to audit findings.
- Training and Awareness:
- Training Modules: Provide targeted training programmes on access control policies and best practices.
- Training Tracking: Monitor employee participation and completion of training modules, ensuring compliance.
- Assessment: Assess employee understanding and awareness of access control measures.
- Incident Management:
- Incident Tracker: Log and track access control incidents, ensuring timely and effective responses.
- Workflow: Automate incident response processes, coordinating activities and ensuring thorough documentation.
- Notifications: Set up notifications to alert relevant stakeholders of access control incidents and required actions.
By leveraging ISMS.online’s comprehensive features, organisations can effectively implement and demonstrate compliance with Annex A.5.15 Access Control. This ensures robust protection of sensitive information and assets. Overcoming common challenges through strategic planning and effective use of technology will lead to a more secure and compliant organisation. Additionally, the detailed compliance checklists provided for each step ensure a thorough and systematic approach to implementing and maintaining access control measures.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.5.15
To ensure your organisation meets the highest standards of information security and compliance, it’s crucial to have the right tools and support. ISMS.online offers a comprehensive platform that simplifies the implementation of ISO 27001:2022 controls, including Annex A.5.15 Access Control.
With features designed to streamline policy management, user access control, audit management, training, and incident response, ISMS.online empowers you to protect your sensitive information and maintain robust security practices.
Ready to elevate your information security management system? Contact ISMS.online today and book a demo to see how our platform can help you achieve and maintain ISO 27001:2022 compliance with ease.