ISO 27001 A.5.25 Assessment and Decision on Information Security Events Checklist
ISO 27001:2022 Annex A.5.25 focuses on the critical processes involved in assessing and making decisions about information security events. This control ensures that security events are identified, assessed, and managed effectively to mitigate potential risks.
Implementing this control requires robust policies, real-time monitoring, systematic assessment, and well-coordinated response strategies.
This guide provides an overview of key elements, common challenges, solutions, compliance checklists, and the role of ISMS.online in facilitating compliance with A.5.25.

ISO 27001 made easy
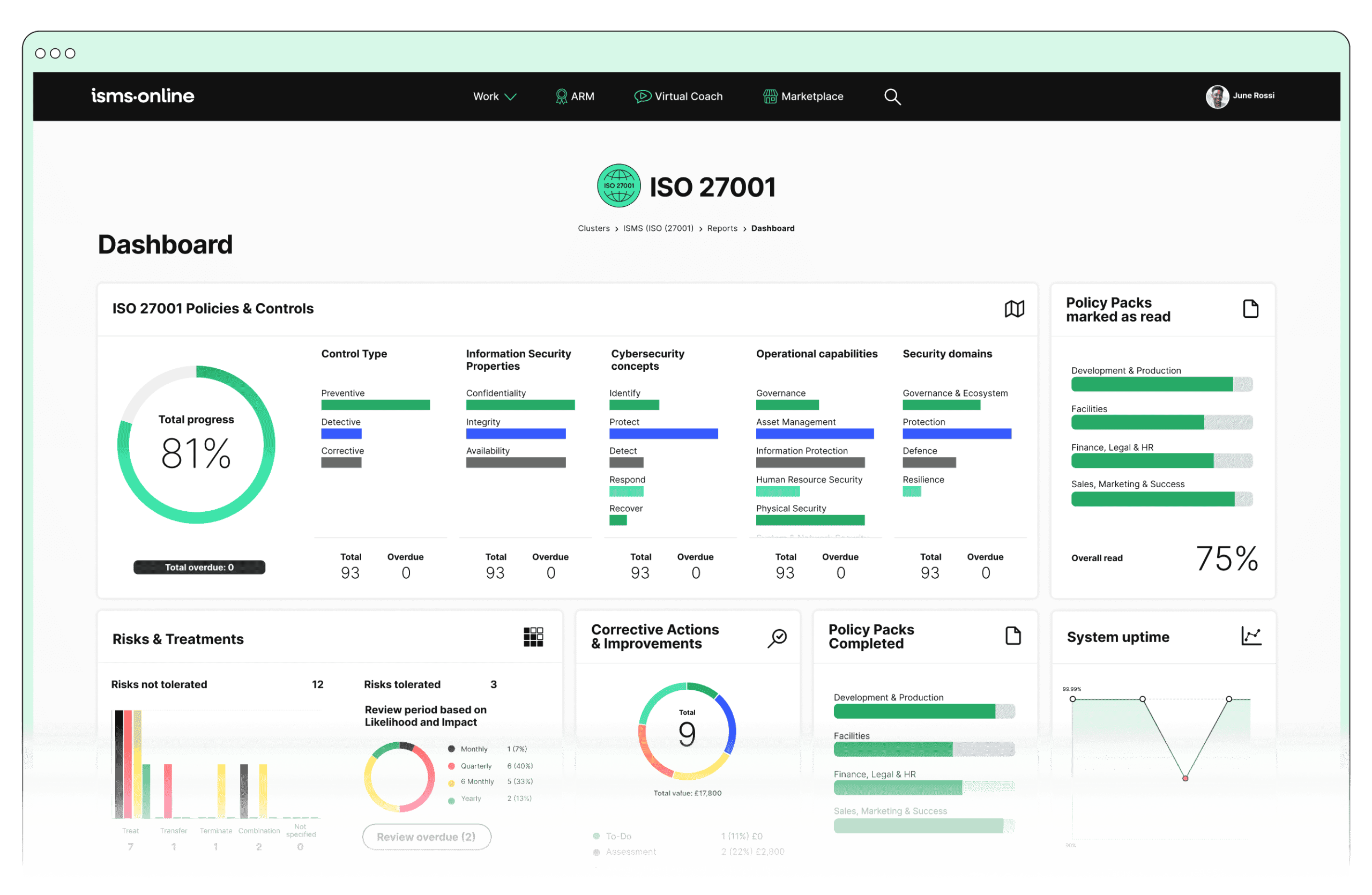
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.5.25? Key Aspects and Common Challenges
1. Identification of Events:
Continuous Monitoring:
Challenge: Ensuring real-time monitoring across diverse IT environments.
- Solution: Use robust monitoring tools integrated with ISMS.online’s incident tracker.
Compliance Checklist:
Related ISO Clause: 9.1 Monitoring, measurement, analysis and evaluation.
Event Logging:
Challenge: Managing large volumes of log data and ensuring relevant events are captured.
- Solution: Utilise automated logging and filtering features.
Compliance Checklist:
Related ISO Clause: 7.5 Documented information.
2. Assessment of Events:
Initial Analysis:
Challenge: Rapidly analysing events to determine their significance.
- Solution: Employ ISMS.online’s workflow automation.
Compliance Checklist:
Related ISO Clause: 8.2 Information security risk assessment.
Risk Assessment:
Challenge: Accurately assessing the potential impact of events.
- Solution: Use the dynamic risk map and continuous risk monitoring features.
Compliance Checklist:
Related ISO Clause: 6.1 Actions to address risks and opportunities.
Categorisation:
Challenge: Consistently categorising events based on severity and urgency.
- Solution: Establish standardised categorisation criteria and use ISMS.online’s templates.
Compliance Checklist:
Related ISO Clause: 8.2 Information security risk assessment.
3. Decision-Making:
Response Strategy:
Challenge: Developing appropriate response strategies under time constraints.
- Solution: Leverage ISMS.online’s policy templates.
Compliance Checklist:
Related ISO Clause: 6.2 Information security objectives and planning to achieve them.
Notification:
Challenge: Ensuring timely and accurate communication to all relevant stakeholders.
- Solution: Implement ISMS.online’s notification system.
Compliance Checklist:
Related ISO Clause: 7.4 Communication.
Documentation:
Challenge: Keeping thorough and accurate records of all events and decisions.
- Solution: Use ISMS.online’s document control and collaboration tools.
Compliance Checklist:
Related ISO Clause: 7.5 Documented information.
4. Mitigation and Control Measures:
Immediate Actions:
Challenge: Quickly containing and mitigating the impact of security events.
- Solution: Predefine immediate action plans and integrate them into ISMS.online’s workflows.
Compliance Checklist:
Related ISO Clause: 8.1 Operational planning and control.
Follow-Up Actions:
Challenge: Ensuring follow-up actions address root causes and prevent recurrence.
- Solution: Track and manage follow-up actions using ISMS.online’s corrective action tracking.
Compliance Checklist:
Related ISO Clause: 10.1 Nonconformity and corrective action.
5. Review and Lessons Learned:
Post-Event Analysis:
Challenge: Conducting thorough and unbiased post-event reviews.
- Solution: Use ISMS.online’s audit templates and review tools.
Compliance Checklist:
Related ISO Clause: 9.2 Internal audit.
Lessons Learned:
Challenge: Integrating lessons learned into the ISMS for continuous improvement.
- Solution: Document lessons learned and update policies and procedures through ISMS.online’s version control.
Compliance Checklist:
Related ISO Clause: 10.2 Continual improvement.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.5.25
To demonstrate compliance with A.5.25, the following features of ISMS.online are particularly useful:
Incident Management:
- Incident Tracker: Logs and tracks information security events, ensuring comprehensive documentation and facilitating initial analysis.
- Workflow Automation: Manages the workflow from event detection to resolution, ensuring all steps are followed systematically.
- Notifications: Sends automatic notifications to relevant stakeholders to ensure timely communication.
Risk Management:
- Dynamic Risk Map: Provides a visual representation of risks, helping to assess the impact of security events in real time.
- Risk Monitoring: Continuously monitors risks and updates risk assessments based on new information from security events.
Policy Management:
- Policy Templates: Offers templates for incident response policies, ensuring standardised response strategies.
- Version Control: Maintains up-to-date policies and procedures, reflecting lessons learned from past incidents.
Audit Management:
- Audit Plan and Templates: Facilitates regular internal audits to review the effectiveness of the incident management process and identify areas for improvement.
- Corrective Actions: Tracks and manages corrective actions resulting from audits and post-event analyses.
Documentation:
- Document Control: Ensures all documents related to incident assessment and decision-making are securely stored and easily accessible.
- Collaboration Tools: Allows team members to collaborate effectively on documenting and analysing security events.
Training and Awareness:
- Training Modules: Provides training programmes to enhance awareness and competency in incident management.
- Training Tracking: Tracks training completion and effectiveness, ensuring continuous improvement in handling security events.
Benefits of Compliance
- Enhanced Preparedness: Improves the organisation’s readiness to handle information security events effectively.
- Risk Mitigation: Reduces the potential impact of security events on the organisation.
- Compliance: Ensures compliance with ISO 27001:2022 requirements and other relevant regulations.
- Continuous Improvement: Promotes a culture of continuous improvement in information security management.
By leveraging ISMS.online features and addressing common challenges, organisations can effectively implement and demonstrate compliance with A.5.25, ensuring a structured and effective approach to managing information security events. This leads to better protection of information assets and an overall enhanced security posture.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.5.25
Elevate Your Information Security with ISMS.online
Ready to take your information security management to the next level? Ensure compliance with ISO 27001:2022 Annex A.5.25 and other critical controls with the comprehensive tools and features offered by ISMS.online. Our platform simplifies the complex processes of monitoring, assessing, and responding to information security events, ensuring your organisation is always prepared.
Get Started
Discover how ISMS.online can transform your information security management. Contact us now to schedule a personalised demo and see our powerful features in action. Let us show you how easy it can be to achieve and maintain ISO 27001:2022 compliance while enhancing your overall security posture.