ISO 27001 A.5.27 Learning From Information Security Incidents Checklist
ISO 27001:2022, A.5.27 is pivotal for ensuring that organisations learn from information security incidents to bolster their security posture. This control emphasises thorough analysis, lesson extraction, and continuous improvement, thereby strengthening the Information Security Management System (ISMS).
Below is an in-depth exploration of A.5.27, the common challenges CISOs face, actionable solutions, relevant ISMS.online features, and a detailed compliance checklist.
Purpose of Annex A.5.27
The primary objective of A.5.27 is to facilitate systematic learning from information security incidents to prevent recurrence, enhance security measures, and fortify the ISMS.
This encompasses conducting detailed post-incident reviews, identifying lessons learned, implementing necessary improvements, and persistently monitoring and reviewing these changes.

ISO 27001 made easy
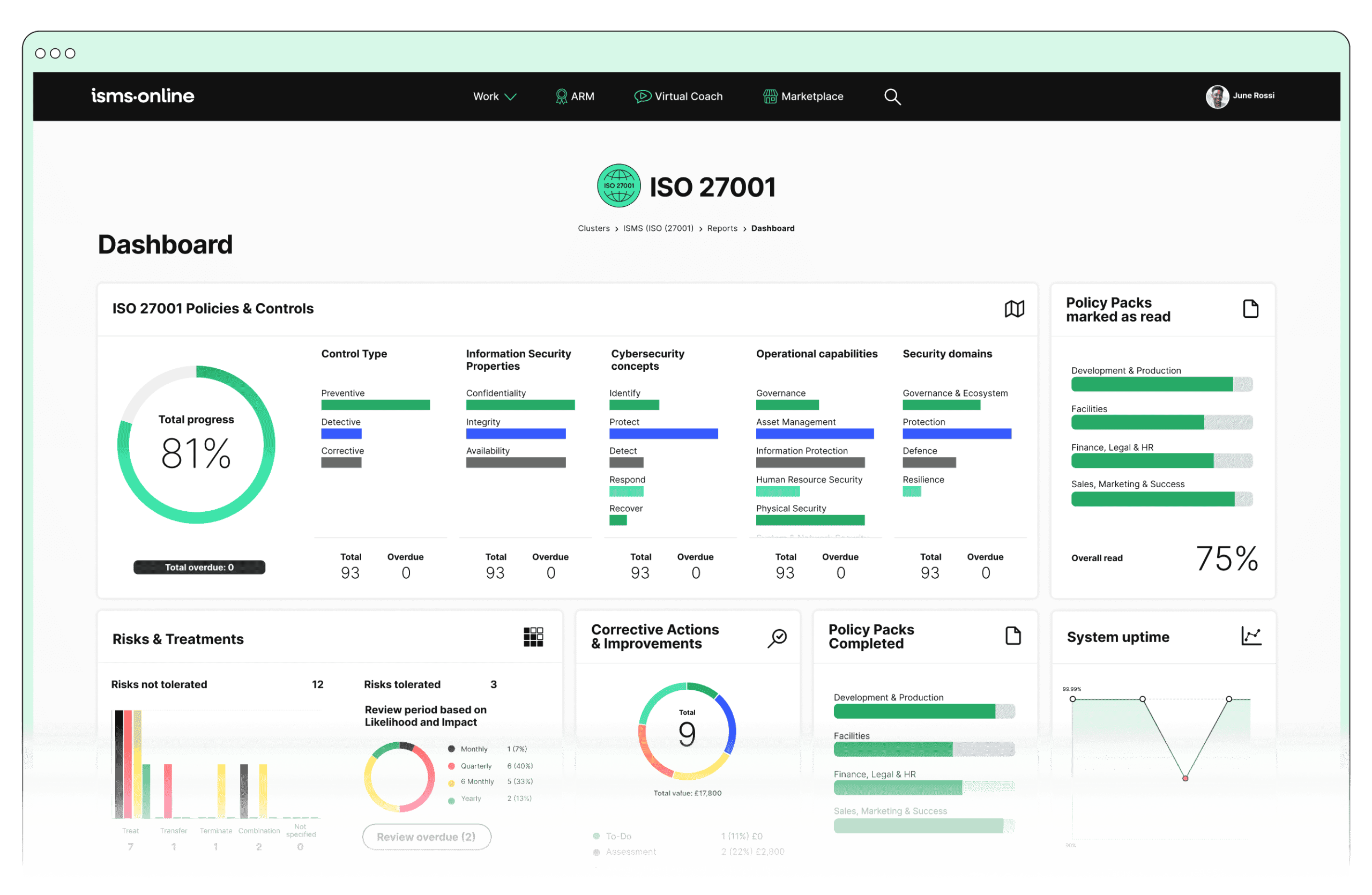
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.5.27? Key Aspects and Common Challenges
1. Post-Incident Review
- Conduct Thorough Analysis: After an incident, it is essential to perform a comprehensive analysis to understand the root causes, impacts, and sequence of events.
- Solution: Implement a standardised incident analysis protocol to ensure consistency and objectivity.
- Relevant ISO Clauses:
- Risk Assessment
- Monitoring, Measurement, Analysis, and Evaluation
- ISMS.online Feature: Incident Tracker – Facilitates detailed recording and tracking of incidents, enabling thorough analysis and documentation.
- Compliance Checklist:
Document incident details and timeline.Perform root cause analysis.Identify affected systems and data.Evaluate incident response effectiveness.
Common Challenge: Ensuring a thorough and unbiased analysis can be difficult due to time constraints and potential biases.
- Document Findings: Capture all findings, including what went wrong, what was done correctly, and areas for improvement.
- Solution: Use automated tools and templates to streamline the documentation process.
- Relevant ISO Clauses:
- Documented Information
- Corrective Action
- ISMS.online Feature: Documentation – Ensures meticulous recording of incident details and analysis.
- Compliance Checklist:
Record findings in a structured format.Include both what went wrong and what was done correctly.Ensure documentation is stored securely.
Common Challenge: Comprehensive documentation can be overwhelming and time-consuming.
2. Identification of Lessons Learned
- Extract Key Lessons: Identify lessons from the incident, focusing on gaps in processes, policies, and controls.
- Solution: Facilitate workshops with cross-functional teams to gain diverse insights and develop comprehensive lessons.
- Relevant ISO Clauses:
- Management Review
- Improvement
- ISMS.online Feature: Lessons Learned Tracker – Captures and analyses lessons learned systematically.
- Compliance Checklist:
Analyse gaps in processes, policies, and controls.Identify actionable improvements.Document lessons learned in an accessible format.
Common Challenge: Extracting actionable lessons from incidents can be complex, especially if the incident is multifaceted.
- Communicate Lessons: Share these lessons with relevant stakeholders to raise awareness and drive improvements.
- Solution: Establish a communication plan that includes regular updates and feedback mechanisms.
- Relevant ISO Clauses:
- Communication
- Awareness
- ISMS.online Feature: Communication Tools – Enables effective dissemination of lessons learned across the organisation.
- Compliance Checklist:
Develop a communication plan for stakeholders.Disseminate lessons learned to relevant parties.Schedule follow-up meetings to discuss improvements.
Common Challenge: Ensuring effective communication and stakeholder engagement can be challenging.
3. Implementing Improvements
- Update Policies and Procedures: Based on the lessons learned, update existing policies, procedures, and controls to prevent similar incidents in the future.
- Solution: Engage stakeholders early in the process and provide clear rationales for changes to gain buy-in.
- Relevant ISO Clauses:
- Planning
- Control of Documented Information
- ISMS.online Feature: Policy Management – Facilitates easy updating and version control of policies and procedures to incorporate improvements.
- Compliance Checklist:
Revise policies based on lessons learned.Implement changes in a timely manner.Communicate policy updates to all employees.
Common Challenge: Resistance to change and ensuring timely updates to policies and procedures.
- Enhance Training and Awareness: Provide additional training and awareness programmes to employees to reinforce the improvements.
- Solution: Implement a comprehensive training schedule with assessments to verify understanding.
- Relevant ISO Clauses:
- Competence
- Awareness
- ISMS.online Feature: Training Modules – Customisable training modules to educate employees on new policies and lessons learned.
- Compliance Checklist:
Update training materials to reflect new policies.Schedule and conduct training sessions.Track employee participation and comprehension.
Common Challenge: Ensuring that all employees receive and understand the necessary training.
4. Monitoring and Review
- Track Implementation: Ensure that the identified improvements are implemented and tracked for effectiveness.
- Solution: Use key performance indicators (KPIs) and regular monitoring to assess the impact of changes.
- Relevant ISO Clauses:
- Monitoring, Measurement, Analysis, and Evaluation
- Internal Audit
- ISMS.online Feature: Performance Tracking – Tracks the implementation and effectiveness of improvements.
- Compliance Checklist:
Establish metrics to measure the effectiveness of changes.Regularly review performance against metrics.Document any issues and corrective actions.
Common Challenge: Continuously monitoring and measuring the effectiveness of implemented changes.
- Regular Reviews: Regularly review the implemented changes to ensure they are working as intended and make further adjustments if necessary.
- Solution: Schedule periodic reviews and allocate dedicated resources to ensure consistency.
- Relevant ISO Clauses:
- Management Review
- Continual Improvement
- ISMS.online Feature: Audit Management – Conducts regular audits and reviews to ensure continual improvement and effectiveness of changes.
- Compliance Checklist:
Schedule regular reviews of implemented changes.Conduct audits to ensure compliance.Update improvement plans based on review findings.
Common Challenge: Allocating time and resources for regular reviews.
Benefits of Compliance
- Continuous Improvement: Promotes a culture of continuous improvement by learning from past incidents and adapting accordingly.
- Enhanced Security Posture: Strengthens the organisation’s defences against future incidents through improved policies, procedures, and awareness.
- Risk Reduction: Reduces the likelihood and impact of future incidents by addressing root causes and implementing preventive measures.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.5.27
- Incident Tracker: Facilitates detailed recording, tracking, and analysis of incidents.
- Documentation: Ensures comprehensive recording of incident details and analysis.
- Lessons Learned Tracker: Captures and analyses lessons learned systematically.
- Communication Tools: Enables effective dissemination of lessons learned across the organisation.
- Policy Management: Allows easy updating and version control of policies and procedures.
- Training Modules: Provides customisable training to reinforce new policies and lessons learned.
- Performance Tracking: Tracks the implementation and effectiveness of improvements.
- Audit Management: Conducts regular audits and reviews for continual improvement.
Common Challenges for a CISO
- Post-Incident Review:
- Ensuring thorough and unbiased analysis despite time constraints and potential biases.
- Managing the overwhelming task of comprehensive documentation.
- Identification of Lessons Learned:
- Extracting actionable lessons from complex incidents.
- Effectively communicating and engaging stakeholders with the lessons learned.
- Implementing Improvements:
- Overcoming resistance to change and ensuring timely updates to policies and procedures.
- Guaranteeing that all employees receive and understand the necessary training.
- Monitoring and Review:
- Continuously monitoring and measuring the effectiveness of implemented changes.
- Allocating time and resources for regular reviews.
Detailed Annex A.5.27 Compliance Checklist
- Post-Incident Review:
- Conduct Thorough Analysis:
Document incident details and timeline.Perform root cause analysis.Identify affected systems and data.Evaluate incident response effectiveness. - Document Findings:
Record findings in a structured format.Include both what went wrong and what was done correctly.Ensure documentation is stored securely.
- Conduct Thorough Analysis:
- Identification of Lessons Learned:
- Extract Key Lessons:
Analyse gaps in processes, policies, and controls.Identify actionable improvements.Document lessons learned in an accessible format. - Communicate Lessons:
Develop a communication plan for stakeholders.Disseminate lessons learned to relevant parties.Schedule follow-up meetings to discuss improvements.
- Extract Key Lessons:
- Implementing Improvements:
- Update Policies and Procedures:
Revise policies based on lessons learned.Implement changes in a timely manner.Communicate policy updates to all employees. - Enhance Training and Awareness:
Update training materials to reflect new policies.Schedule and conduct training sessions.Track employee participation and comprehension.
- Update Policies and Procedures:
- Monitoring and Review:
- Track Implementation:
Establish metrics to measure the effectiveness of changes.Regularly review performance against metrics.Document any issues and corrective actions. - Regular Reviews:
Schedule regular reviews of implemented changes.Conduct audits to ensure compliance.Update improvement plans based on review findings.
- Track Implementation:

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.5.27
Are you ready to transform your information security management and ensure compliance with ISO 27001:2022?
Discover how ISMS.online can help you seamlessly implement A.5.27 Learning From Information Security Incidents, and much more. Our platform provides all the tools you need to enhance your security posture, streamline processes, and drive continuous improvement.
Contact us today to learn more about how ISMS.online can support your organisation’s information security needs. Book a demo now and see first-hand how our comprehensive features can help you achieve compliance and strengthen your ISMS.
Don’t wait—secure your future today. Contact ISMS.online and book your demo now