ISO 27001 A.5.32 Intellectual Property Rights Checklist
A.5.32 Intellectual Property Rights within the context of ISO 27001:2022 focuses on ensuring that an organisation’s intellectual property (IP) is protected and managed effectively. Intellectual property includes assets such as patents, trademarks, copyrights, trade secrets, and other proprietary information.
Properly managing and protecting IP is critical for maintaining competitive advantage, fostering innovation, and ensuring compliance with legal and regulatory requirements. This involves a comprehensive approach that encompasses identification, protection, legal compliance, monitoring, enforcement, awareness, documentation, and incident response.

ISO 27001 made easy
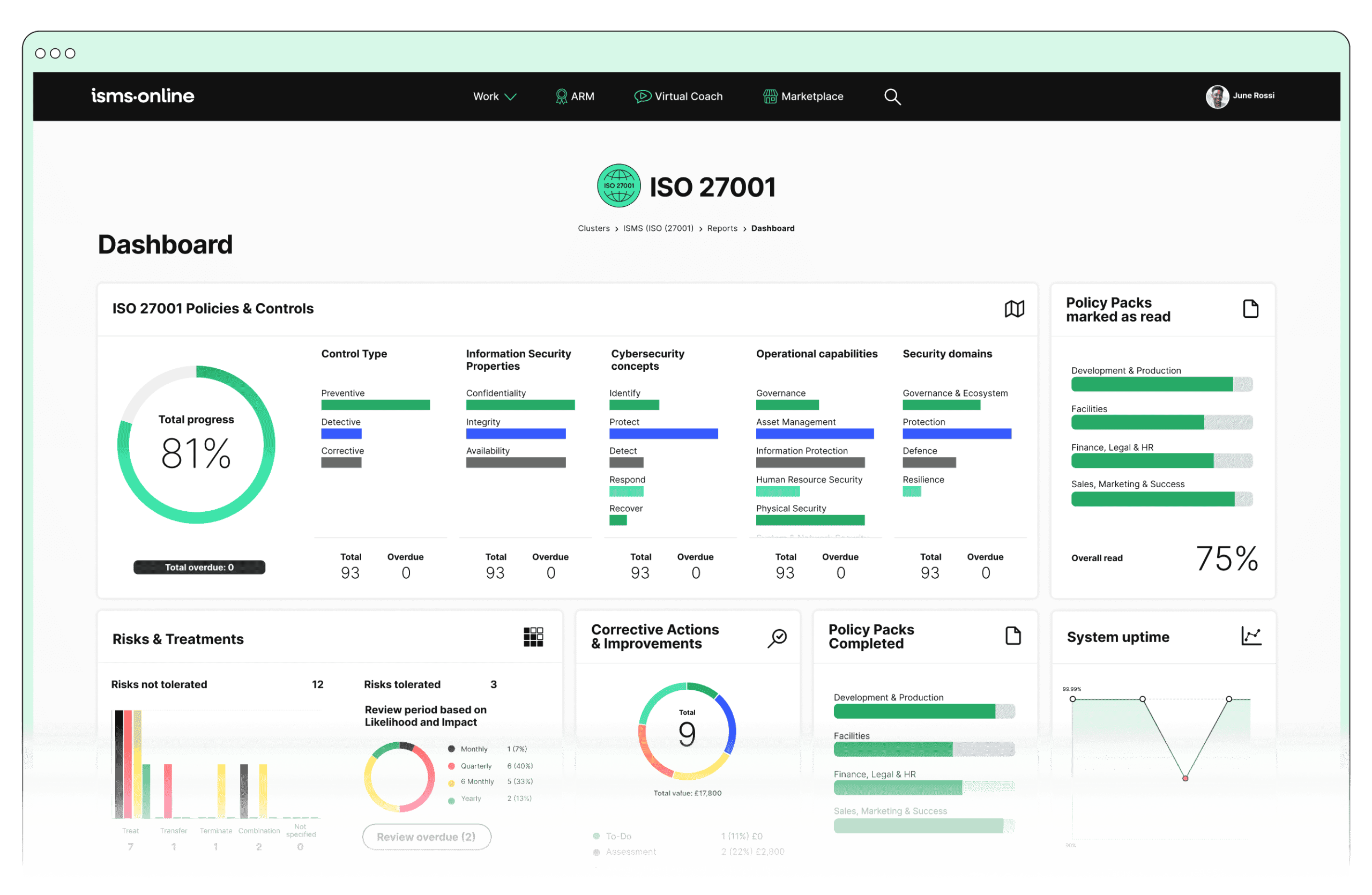
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.5.32? Key Aspects and Common Challenges
1. Identification of Intellectual Property
Common Challenges: Accurately identifying and cataloguing all IP assets can be difficult due to the diversity and scope of IP. Overlooked IP assets can lead to vulnerabilities.
Solution: Utilise the ISMS.online Asset Registry to maintain a comprehensive inventory and classification of IP assets.
Compliance Checklist:
- Identify and catalogue all IP assets.
- Classify IP assets based on sensitivity and value.
- Regularly update the IP asset registry to reflect changes.
Related ISO 27001 Clauses: Understanding the organisation and its context, Operational planning and control.
2. Protection Measures
Common Challenges: Implementing appropriate protection measures can be complex, especially with varying levels of sensitivity and different types of IP.
Solution: Leverage ISMS.online’s Asset Management features to apply technical controls like encryption and administrative controls like access policies effectively.
Compliance Checklist:
- Implement technical controls (e.g., encryption) for IP protection.
- Establish physical controls (e.g., secure storage) for sensitive IP.
- Develop and enforce administrative controls (e.g., access policies).
Related ISO 27001 Clauses: Risk treatment, Information security risk assessment.
3. Compliance and Legal Requirements
Common Challenges: Keeping up with diverse and evolving legal and regulatory requirements related to IP across different jurisdictions can be overwhelming.
Solution: Use the Regs Database and Alert System in ISMS.online to stay updated on relevant IP laws and regulations.
Compliance Checklist:
- Identify all applicable IP-related legal and regulatory requirements.
- Ensure policies and procedures comply with these requirements.
- Regularly review and update compliance documentation.
Related ISO 27001 Clauses: Understanding the needs and expectations of interested parties, Leadership and commitment.
4. Monitoring and Enforcement
Common Challenges: Continuous monitoring for IP breaches and enforcement of IP rights can be resource-intensive and require specialised skills.
Solution: Implement ISMS.online’s Incident Management features to monitor IP protection, log incidents, and automate workflows for consistent handling.
Compliance Checklist:
- Monitor IP assets for potential breaches continuously.
- Log all IP-related incidents promptly.
- Automate incident response workflows for consistency.
- Enforce IP rights through appropriate legal channels.
Related ISO 27001 Clauses: Monitoring, measurement, analysis, and evaluation, Nonconformity and corrective action.
5. Awareness and Training
Common Challenges: Ensuring all employees are aware of IP policies and their responsibilities can be challenging, especially in large or dispersed organisations.
Solution: Utilise ISMS.online’s Training Modules to provide comprehensive training and track completion to ensure all employees understand IP protection.
Compliance Checklist:
- Develop and distribute IP awareness training materials.
- Conduct regular training sessions for all employees.
- Track training completion and assess understanding.
Related ISO 27001 Clauses: Competence, Awareness.
6. Documentation and Procedures
Common Challenges: Maintaining up-to-date and accurate documentation of IP management procedures is essential but can be laborious.
Solution: Use ISMS.online’s Policy Management features to create, update, and control access to IP management documents, ensuring consistency and compliance.
Compliance Checklist:
- Document all IP management procedures clearly.
- Implement a version control system for procedure documents.
- Regularly review and update documentation to reflect current practices.
Related ISO 27001 Clauses: Documented information, Operational planning and control.
7. Incident Response
Common Challenges: Developing and implementing effective incident response plans for IP-related incidents requires coordination and expertise.
Solution: Employ ISMS.online’s Incident Tracker and Workflow to plan, prepare, and execute responses to IP incidents swiftly and effectively.
Compliance Checklist:
- Develop a comprehensive incident response plan for IP incidents.
- Train relevant personnel on incident response procedures.
- Regularly test and update the incident response plan.
- Document and review all incidents and responses for continuous improvement.
Related ISO 27001 Clauses: Actions to address risks and opportunities, Continual improvement.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.5.32
ISMS.online provides several features that are instrumental in demonstrating compliance with A.5.32:
1. Asset Management
- Asset Registry: Maintain a detailed registry of IP assets, ensuring all are identified and catalogued.
- Labeling System: Implement classification and labeling of IP assets to ensure appropriate protection measures are in place.
- Access Control: Manage and monitor access to IP assets, ensuring only authorised personnel have access.
2. Policy Management
- Policy Templates: Utilise pre-built policy templates to create comprehensive IP protection policies.
- Policy Pack: Bundle relevant policies and ensure they are communicated effectively across the organisation.
- Version Control: Keep track of policy updates and maintain a history of changes to ensure compliance and accountability.
- Document Access: Control who can view and edit policies, ensuring sensitive IP-related policies are protected.
3. Incident Management
- Incident Tracker: Log and track IP-related incidents, ensuring a prompt and effective response.
- Workflow: Define and automate workflows for incident management, ensuring consistent handling of IP incidents.
- Notifications: Set up notifications for IP incidents to ensure relevant stakeholders are informed immediately.
- Reporting: Generate reports on IP incidents to monitor trends and improve incident response strategies.
4. Compliance Management
- Regs Database: Access a database of regulations and ensure compliance with IP-related legal requirements.
- Alert System: Receive alerts on changes to IP laws and regulations to stay compliant.
- Reporting: Generate compliance reports to demonstrate adherence to IP protection standards.
5. Training
- Training Modules: Provide training on IP protection, ensuring employees are aware of their roles and responsibilities.
- Training Tracking: Monitor and track training completion to ensure all employees have received necessary education.
- Assessment: Assess the effectiveness of training programmes and identify areas for improvement.
Detailed Annex A.5.32 Compliance Checklist
1. Identification of Intellectual Property
2. Protection Measures
3. Compliance and Legal Requirements
4. Monitoring and Enforcement
5. Awareness and Training
6. Documentation and Procedures
7. Incident Response
By leveraging these ISMS.online features, organisations can effectively manage and protect their intellectual property, ensuring compliance with ISO 27001:2022 A.5.32 and safeguarding their valuable IP assets. This approach helps address common challenges faced by CISOs in implementing IP protection, streamlining processes, and enhancing organisational security.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.5.32
Are you ready to elevate your organisation’s intellectual property protection and ensure compliance with ISO 27001:2022? With ISMS.online, you can streamline your processes, safeguard your valuable IP assets, and confidently meet regulatory requirements.
Our comprehensive suite of tools and features is designed to address the challenges faced by CISOs and security professionals, providing you with the support and resources needed to implement robust IP protection measures.
Contact us today to book a demo and see how ISMS.online can transform your IP management and compliance strategy. Our experts are here to guide you through the process, demonstrating how our platform can help you achieve your security goals. Don’t wait—take the first step towards a more secure and compliant future.