ISO 27001 A.5.36 Compliance With Policies, Rules, and Standards for Information Security Checklist
Objective: Ensure adherence to internal policies, external rules, and industry standards regarding information security to maintain the integrity, confidentiality, and availability of information while fulfilling legal, regulatory, and contractual obligations.
Importance of Compliance: Compliance is crucial for safeguarding sensitive data, maintaining customer trust, and fostering a culture of security awareness.
Non-compliance can lead to data breaches, financial losses, and reputational damage, making a structured approach essential for organisational health and sustainability.

ISO 27001 made easy
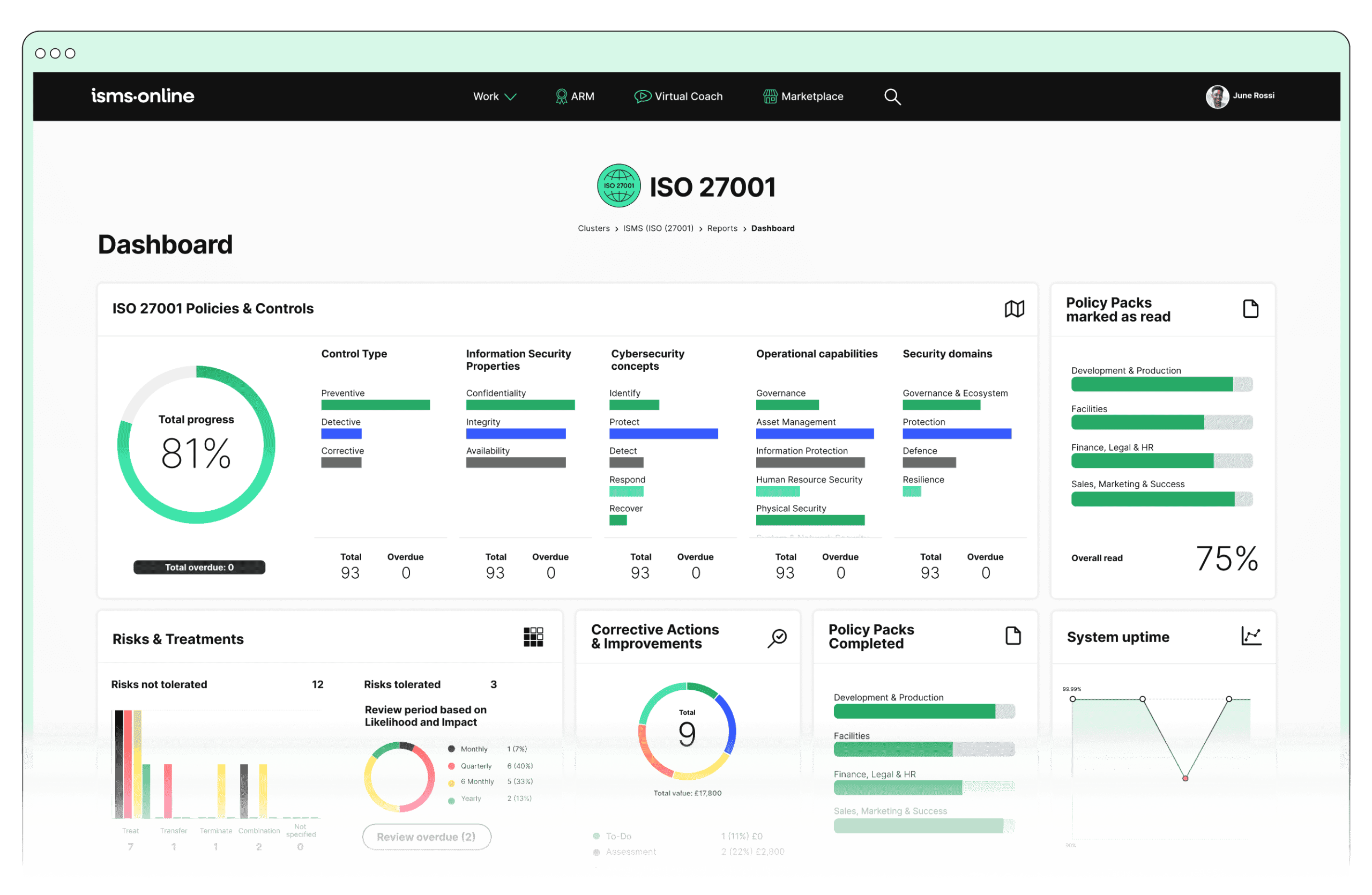
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.5.36? Key Aspects and Common Challenges
1. Policy Development and Maintenance:
Creation and Documentation:
- Solution: Utilise ISMS.online’s Policy Templates and Regulatory Database.
- Checklist:
- Related ISO 27001 Clauses: 5.2 (Information security policy), 7.5.1 (Documented information)
Challenge: Ensuring policies are comprehensive and up-to-date.
Regular Review:
- Solution: Implement ISMS.online’s Version Control.
- Checklist:
- Related ISO 27001 Clauses: 9.2 (Internal audit), 10.2 (Nonconformity and corrective action)
Challenge: Keeping policies updated with regulatory and organisational changes.
2. Communication and Awareness:
Policy Dissemination:
- Solution: Use ISMS.online’s Document Access and Policy Pack.
- Checklist:
- Related ISO 27001 Clauses: 7.3 (Awareness), 7.4 (Communication)
Challenge: Ensuring awareness and understanding of policies.
Training Programmes:
- Solution: Leverage ISMS.online’s Training Modules and Training Tracking.
- Checklist:
- Related ISO 27001 Clauses: 7.2 (Competence), 7.3 (Awareness)
Challenge: Conducting effective training programmes.
3. Implementation and Enforcement:
Roles and Responsibilities:
- Solution: Use ISMS.online’s Role Management.
- Checklist:
- Related ISO 27001 Clauses: 5.3 (Organisational roles, responsibilities, and authorities)
Challenge: Defining and communicating roles and responsibilities.
Compliance Monitoring:
- Solution: Utilise ISMS.online’s Compliance Monitoring and Audit Management.
- Checklist:
- Related ISO 27001 Clauses: 9.1 (Monitoring, measurement, analysis, and evaluation), 9.2 (Internal audit)
Challenge: Continuous monitoring of compliance.
Non-compliance Management:
- Solution: Employ ISMS.online’s Incident Management.
- Checklist:
- Related ISO 27001 Clauses: 10.1 (Nonconformity and corrective action), 10.2 (Continual improvement)
Challenge: Identifying and addressing non-compliance.
4. Assessment and Improvement:
Internal Audits:
- Solution: Use ISMS.online’s Audit Templates and Audit Plan.
- Checklist:
- Related ISO 27001 Clauses: 9.2 (Internal audit), 10.1 (Nonconformity and corrective action)
Challenge: Conducting thorough and regular audits.
Continuous Improvement:
- Solution: Implement ISMS.online’s Corrective Actions and Continuous Improvement tools.
- Checklist:
- Related ISO 27001 Clauses: 10.1 (Nonconformity and corrective action), 10.2 (Continual improvement)
Challenge: Improving policies and procedures based on feedback.
5. Documentation and Reporting:
Record Keeping:
- Solution: Use ISMS.online’s Documentation Management.
- Checklist:
- Related ISO 27001 Clauses: 7.5 (Documented information)
Challenge: Maintaining comprehensive records.
Reporting:
- Solution: Leverage ISMS.online’s Reporting Tools.
- Checklist:
- Related ISO 27001 Clauses: 9.3 (Management review)
Challenge: Providing accurate compliance reports.
Benefits of Compliance
- Risk Mitigation: Reduces the risk of security incidents by ensuring robust policies and controls are in place and followed.
- Regulatory Adherence: Helps the organisation comply with legal, regulatory, and contractual requirements, avoiding potential penalties and legal issues.
- Reputation Management: Enhances the organisation’s reputation by demonstrating a commitment to information security and responsible management of information assets.
- Operational Efficiency: Promotes a consistent and structured approach to information security, leading to more efficient and effective operations.
By leveraging the features of ISMS.online and addressing common challenges with a detailed checklist, organisations can effectively demonstrate compliance with A.5.36 Compliance With Policies, Rules, and Standards for Information Security.
This ensures that their information security management system (ISMS) remains robust, adaptive, and aligned with best practices and regulatory expectations, achieving operational excellence and comprehensive risk management.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

Detailed Annex A.5.36 Compliance Checklist
1. Policy Development and Maintenance:
2. Communication and Awareness:
3. Implementation and Enforcement:
4. Assessment and Improvement:
5. Documentation and Reporting:
By following this detailed compliance checklist and utilising the comprehensive features of ISMS.online, organisations can ensure that they meet the requirements of A.5.36 Compliance With Policies, Rules, and Standards for Information Security.
This systematic approach not only fosters a culture of security awareness and compliance but also enhances the overall security posture of the organisation, ensuring robust protection of information assets.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.5.36
Ensuring compliance with A.5.36 Compliance With Policies, Rules, and Standards for Information Security is critical for safeguarding your organisation’s sensitive data and maintaining trust with your stakeholders. By leveraging the powerful features of ISMS.online, you can streamline your compliance efforts, mitigate risks, and enhance operational efficiency.
Ready to elevate your information security management?
Contact ISMS.online today to schedule a personalised demo. See firsthand how our comprehensive platform can transform your compliance process and fortify your organisation’s security posture. Our experts are here to guide you through the features and demonstrate how ISMS.online can meet your unique needs.