ISO 27001 A.6.4 Disciplinary Process Checklist
Annex A.6.4 in ISO 27001:2022 refers to the Disciplinary Process control. This control ensures that there are established and communicated disciplinary processes in place for employees who have violated information security policies or procedures.
The objective is to enforce compliance with the organisation’s information security policies and procedures, maintaining high information security awareness and adherence among employees.
Effective implementation involves clear policy establishment, thorough communication, meticulous documentation, fair investigation, proportional response, corrective actions, and regular review and improvement.

ISO 27001 made easy
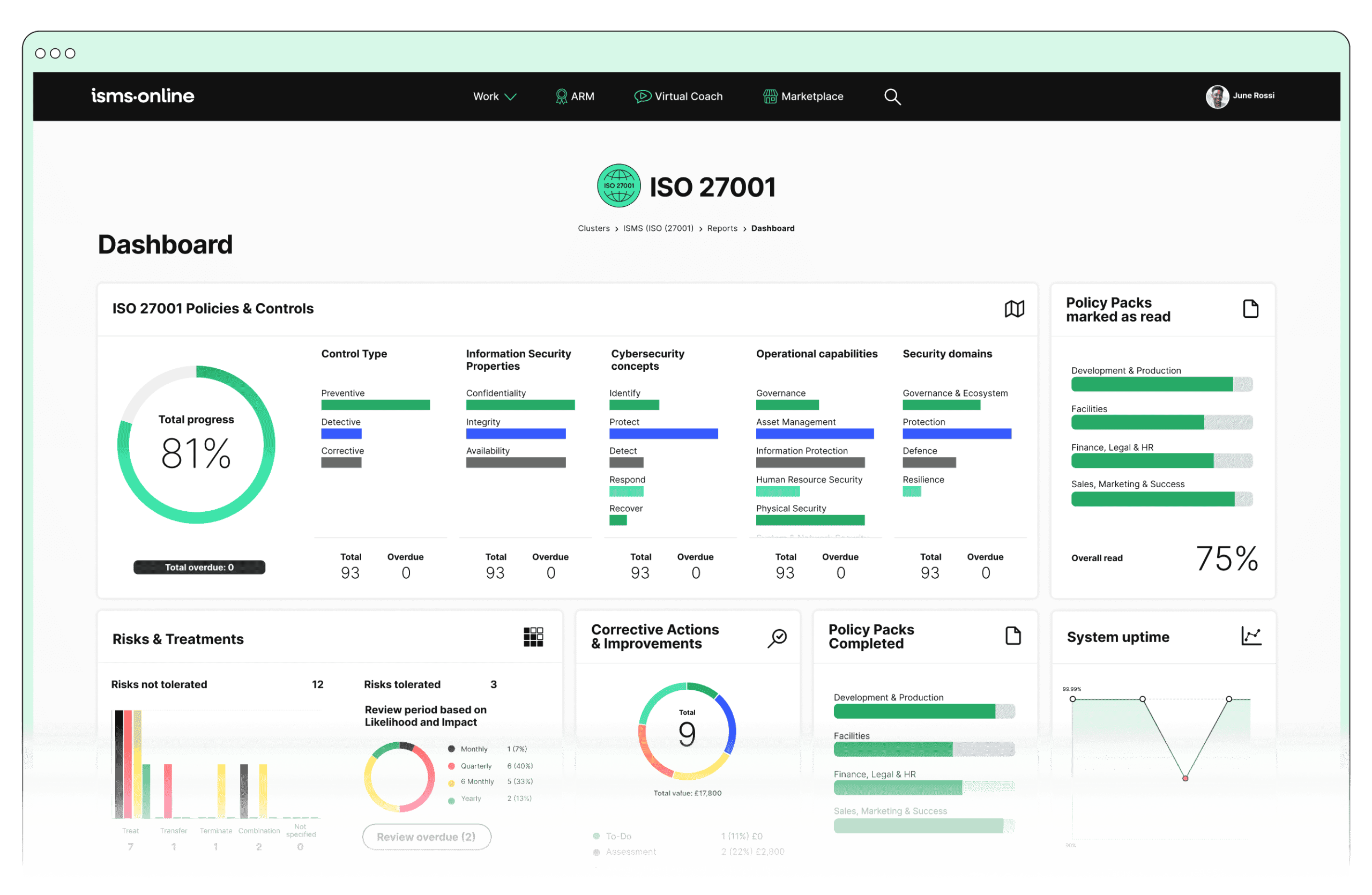
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.6.4? Key Aspects and Common Challenges
Policy Establishment
- Solution:
- Utilise pre-built policy templates to quickly establish a comprehensive disciplinary policy.
- Track changes and updates to policies to ensure the latest version is always accessible and legally compliant.
- Control who can view and edit policies to ensure only authorised personnel can make changes.
- Related ISO 27001 Clauses: Policy, Documented Information
Challenge: Ensuring the disciplinary policy is comprehensive, legally compliant, and aligns with organisational standards.
Compliance Checklist:
Communication
- Solution:
- Quickly communicate policy changes and important information regarding the disciplinary process through an alert system.
- Ensure timely notifications are sent to relevant stakeholders.
- Develop and deliver training programmes on the disciplinary process and information security policies.
- Track employee acknowledgment of the disciplinary policy.
- Related ISO 27001 Clauses: Awareness, Communication
Challenge: Effectively communicating the disciplinary process to all employees and ensuring understanding and acknowledgment.
Compliance Checklist:
Documentation
- Solution:
- Log and track all information security incidents, including details of investigations and outcomes.
- Use templates to standardise documentation of incidents, investigations, and disciplinary actions.
- Ensure all documentation is up-to-date and reflects the latest procedures and policies.
- Maintain access control to ensure documentation is accessible to authorised personnel.
- Related ISO 27001 Clauses: Documented Information, Operational Planning and Control
Challenge: Accurately documenting all incidents, investigations, and outcomes to ensure transparency and accountability.
Compliance Checklist:
Investigation
- Solution:
- Manage the steps involved in the investigation process, ensuring thorough and consistent handling of incidents.
- Define and manage the steps involved in the investigation process.
- Facilitate collaboration among teams during investigations and policy updates while maintaining confidentiality.
- Related ISO 27001 Clauses: Monitoring, Measurement, Analysis and Evaluation, Internal Audit
Challenge: Conducting thorough and fair investigations with authorised personnel and maintaining confidentiality.
Compliance Checklist:
Proportional Response
- Solution:
- Regularly review the effectiveness of the disciplinary process to ensure fairness and consistency.
- Schedule and plan audits to monitor the process.
- Track and document corrective actions taken in response to audit findings.
- Related ISO 27001 Clauses: Nonconformity and Corrective Action, Management Review
Challenge: Ensuring disciplinary actions are fair, consistent, and proportionate to the severity of the violation.
Compliance Checklist:
Corrective Actions
- Solution:
- Implement corrective actions to address the root cause of the violation and prevent future occurrences.
- Use findings from disciplinary processes to improve information security policies and training programmes.
- Track and document corrective actions taken and monitor their effectiveness.
- Related ISO 27001 Clauses: Continual Improvement
Challenge: Implementing effective corrective actions and ensuring they address the root cause of the violation.
Compliance Checklist:
Review and Improvement
- Solution:
- Regularly review and update the disciplinary process using audit management tools.
- Schedule and plan regular reviews of the disciplinary process.
- Use audit findings to enhance and improve the process continuously.
- Implement practices for ongoing improvement based on feedback and audit results.
- Related ISO 27001 Clauses: Continual Improvement
Challenge: Regularly reviewing and updating the disciplinary process to keep it effective and relevant.
Compliance Checklist:
Benefits of Compliance
- Deterrence: Establishing clear disciplinary processes acts as a deterrent to potential violators.
- Consistency: Ensures consistent and fair treatment of all employees in case of information security breaches.
- Accountability: Holds employees accountable for their actions, promoting a culture of responsibility and awareness.
- Improvement: Provides opportunities to identify weaknesses in current policies and procedures, enabling continuous improvement.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.6.4
- Policy Management:
- Utilise pre-built policy templates to quickly establish a formal disciplinary policy.
- Track changes and updates to policies, ensuring the latest version is always accessible.
- Control who can view and edit policies, ensuring only authorised personnel can make changes.
- Incident Management:
- Log and track all information security incidents, including details of investigations and outcomes.
- Define and manage the steps involved in the investigation process, ensuring thorough and consistent handling of incidents.
- Set up automatic notifications to alert relevant personnel when an incident is reported or requires action.
- Audit Management:
- Use audit templates to regularly review the effectiveness of the disciplinary process.
- Schedule and plan audits to ensure continuous monitoring and improvement.
- Track and document corrective actions taken in response to audit findings.
- Training Management:
- Develop and deliver training programmes on the disciplinary process and information security policies.
- Monitor employee participation in training sessions and ensure completion.
- Conduct assessments to evaluate understanding and compliance with the disciplinary process.
- Documentation:
- Use templates to standardise documentation of incidents, investigations, and disciplinary actions.
- Ensure all documentation is up-to-date and reflects the latest procedures and policies.
- Facilitate collaboration among teams during investigations and policy updates.
- Communication:
- Quickly communicate policy changes and important information regarding the disciplinary process.
- Ensure timely notifications are sent to relevant stakeholders during incidents and investigations.
- Use collaboration tools to discuss and resolve incidents efficiently.
Detailed Annex A.6.4 Compliance Checklist
- Policy Establishment:
Develop a formal disciplinary policy using policy templates.Ensure policy aligns with legal and regulatory requirements.Use version control to track changes and updates to the policy.Control document access to authorised personnel only. - Communication:
Communicate the disciplinary policy through the alert system.Ensure all employees receive notifications about the policy.Include the policy in employee handbooks and training sessions.Track acknowledgment of the policy by all employees. - Documentation:
Log and track all information security incidents in the incident tracker.Use standardised templates for documenting incidents and disciplinary actions.Maintain up-to-date documentation reflecting the latest procedures and policies.Ensure documentation is accessible to authorised personnel. - Investigation:
Define and manage investigation steps using the workflow feature.Ensure authorised personnel conduct investigations.Maintain confidentiality throughout the investigation process.Collaborate using secure tools to facilitate investigations. - Proportional Response:
Regularly review the effectiveness of the disciplinary process with audit templates.Schedule and plan audits to monitor the process.Track and document corrective actions in response to audit findings.Ensure disciplinary actions are consistent and proportionate. - Corrective Actions:
Implement corrective actions to address root causes of violations.Use training modules to improve policies and training programmes.Track and document corrective actions taken.Monitor the effectiveness of corrective actions. - Review and Improvement:
Regularly review the disciplinary process using audit management tools.Schedule and plan regular reviews and updates.Use findings from audits to enhance and improve the process.Implement continuous improvement practices.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.6.4
Ready to take your information security management to the next level? Ensure compliance with ISO 27001:2022 Annex A.6.4 and other critical controls with the powerful features of ISMS.online.
Experience firsthand how our platform can streamline your disciplinary processes, enhance policy management, and improve overall security posture.
Don’t miss out on the opportunity to transform your organisation’s information security practices. Contact ISMS.online today to book a demo and see how we can help you achieve and maintain ISO 27001:2022 compliance effortlessly.