ISO 27001 A.7.10 Storage Media Checklist
A.7.10 Storage Media within ISO 27001:2022 focuses on the comprehensive management and protection of storage media throughout its lifecycle, ensuring the confidentiality, integrity, and availability of the information it holds.
Effective implementation of this control requires meticulous planning, robust procedures, and continuous monitoring to safeguard against unauthorised access, loss, and damage.
We will delve into the key aspects of A.7.10 Storage Media, common challenges a CISO might face during implementation, ISMS.online features for demonstrating compliance, a detailed compliance checklist, and associated ISO 27001:2022 clauses and requirements.

ISO 27001 made easy
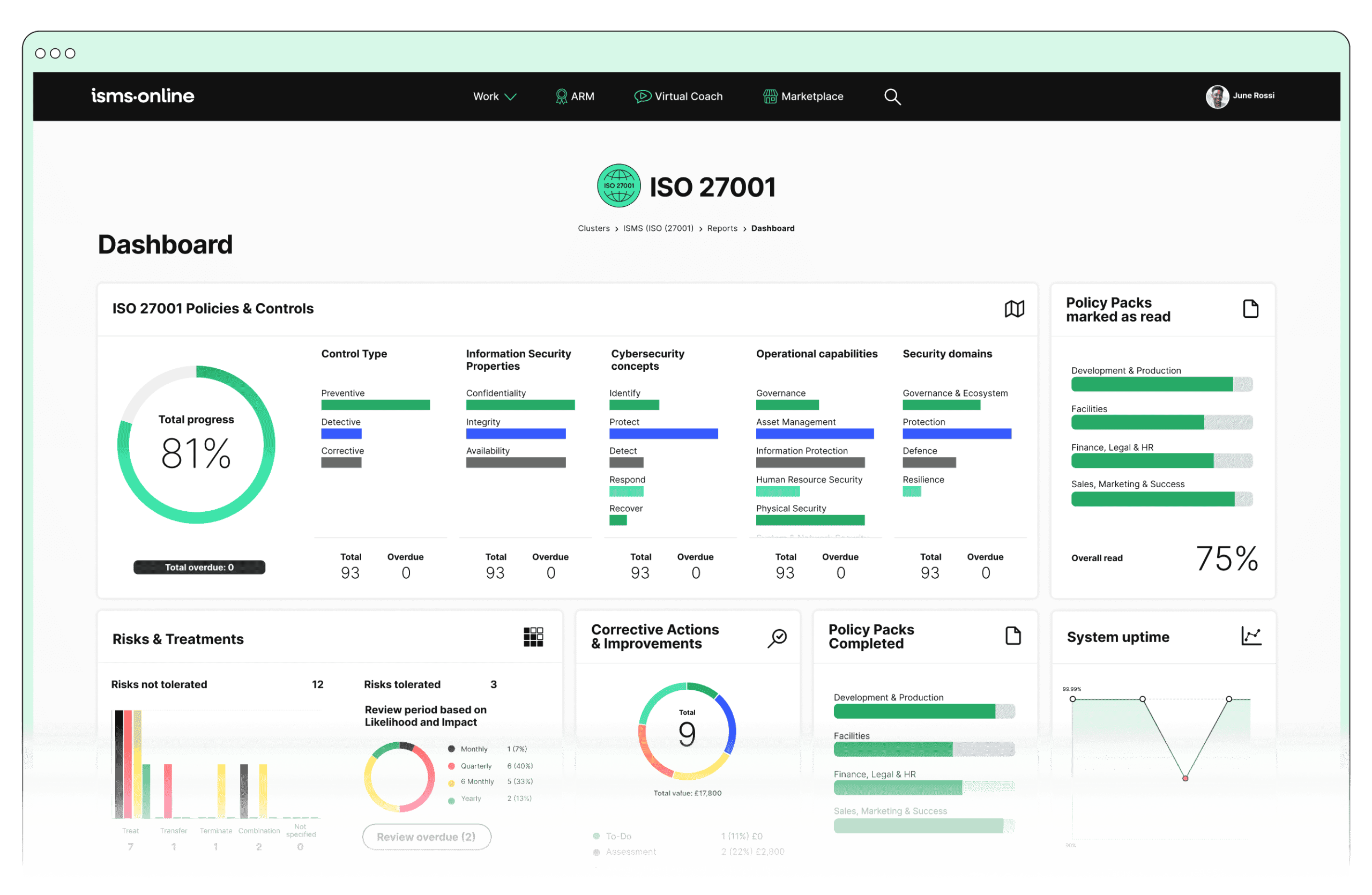
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.7.10? Key Aspects and Common Challenges
Media Handling
Definition: Procedures for securely handling and transporting storage media to prevent unauthorised access, loss, or damage.
Common Challenges: Ensuring consistent adherence to handling procedures across all personnel, especially in large organisations.
Solutions:
- Conduct regular training sessions and awareness programmes to reinforce secure media handling practices.
- Implement secure methods for transferring data, including encryption and physical security measures.
Related ISO 27001:2022 Clauses:
- Clause 7.2: Competence – Training personnel on secure handling procedures.
- Clause 8.2: Operational Planning and Control – Documenting and implementing handling procedures.
Media Storage
Definition: Secure storage locations with adequate access controls to protect against theft, unauthorised access, and environmental threats.
Common Challenges: Finding and maintaining secure storage locations and managing access controls efficiently.
Solutions:
- Implement a centralised inventory system to manage storage media locations.
- Conduct regular audits to ensure compliance with storage procedures.
Related ISO 27001:2022 Clauses:
- Clause 7.5: Documented Information – Maintaining documentation on secure storage locations.
- Clause 9.2: Internal Audit – Conducting regular audits of storage compliance.
Media Classification
Definition: Classifying storage media based on the sensitivity and criticality of the information they contain.
Common Challenges: Consistently classifying large volumes of data accurately.
Solutions:
- Develop clear classification criteria and use automated tools to assist in the classification process.
- Train personnel on classification criteria and procedures.
Related ISO 27001:2022 Clauses:
- Clause 7.2: Competence – Training personnel on classification processes.
- Clause 8.2: Operational Planning and Control – Establishing classification criteria and tools.
Media Disposal
Definition: Secure disposal of storage media that contains sensitive information, ensuring data is irretrievably destroyed.
Common Challenges: Logistically ensuring secure disposal of all media containing sensitive information.
Solutions:
- Establish partnerships with certified disposal vendors.
- Implement stringent disposal procedures, including verification steps to confirm data destruction.
Related ISO 27001:2022 Clauses:
- Clause 8.3: Risk Management – Identifying and mitigating risks related to media disposal.
- Clause 10.1: Nonconformity and Corrective Action – Ensuring verification of data destruction.
Media Tracking
Definition: Maintaining an accurate inventory of all storage media, tracking their location, status, and movement.
Common Challenges: Keeping the inventory up-to-date and accurate in dynamic environments.
Solutions:
- Use advanced tracking systems and regular reconciliation processes.
- Update inventory records promptly following any changes.
Related ISO 27001:2022 Clauses:
- Clause 7.5: Documented Information – Maintaining an up-to-date inventory.
- Clause 8.2: Operational Planning and Control – Implementing tracking systems and processes.
Access Controls
Definition: Restricting access to storage media to authorised personnel only and monitoring access attempts.
Common Challenges: Implementing robust systems to control and monitor access effectively.
Solutions:
- Implement multi-factor authentication (MFA) and comprehensive access logging mechanisms.
- Regularly review and update access control policies and logs.
Related ISO 27001:2022 Clauses:
- Clause 9.1: Monitoring, Measurement, Analysis, and Evaluation – Monitoring access attempts.
- Clause 8.2: Operational Planning and Control – Implementing access controls and reviews.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.7.10
- Policy Management:
- Utilise Policy Templates to establish and communicate clear procedures for handling, storing, and disposing of storage media.
- Ensure continuous updates and version control to keep policies current with evolving security practices and regulatory requirements.
- Asset Management:
- Maintain a comprehensive Asset Registry to track all storage media, including their classification and status.
- Use the Labelling System to mark storage media according to their sensitivity and required protection measures.
- Implement Access Control measures to restrict media access to authorised personnel only and track access attempts.
- Risk Management:
- Conduct Risk Assessments specific to storage media handling, storage, and disposal.
- Utilise the Risk Bank to document identified risks and the associated mitigation strategies.
- Incident Management:
- Use the Incident Tracker to document any security incidents related to storage media, including loss, theft, or unauthorised access.
- Implement Workflow and Notification Systems to ensure timely response and resolution of incidents.
- Audit Management:
- Develop Audit Plans to regularly review storage media management practices.
- Use Audit Templates and Corrective Actions to ensure compliance and address any identified gaps.
- Compliance:
- Monitor compliance with storage media policies through the Compliance Monitoring tools.
- Keep track of regulatory requirements and ensure that storage media management practices align with applicable standards.
- Training Management:
- Deliver targeted Training Modules to educate staff on proper storage media handling, storage, and disposal procedures.
- Track training completion and assess competency through Training Tracking features.
By leveraging these ISMS.online features, organisations can systematically demonstrate compliance with A.7.10 Storage Media, ensuring robust management and protection of their information assets.
Detailed Annex A.7.10 Compliance Checklist
Media Handling
- Establish and document procedures for secure handling and transportation of storage media.
- Train personnel on handling procedures and conduct regular awareness sessions.
- Implement encryption for data transfer to and from storage media.
- Regularly review and update handling procedures to align with best practices.
Media Storage
- Identify and document secure storage locations for all types of media.
- Implement access control measures for storage locations (e.g., locked cabinets, restricted areas).
- Conduct regular audits of storage locations to ensure compliance.
- Ensure environmental conditions meet the necessary requirements for media preservation.
Media Classification
- Develop and document classification criteria for storage media.
- Implement automated tools to assist in the classification process.
- Train personnel on classification criteria and procedures.
- Regularly review and update classification criteria and tools.
Media Disposal
- Establish and document secure disposal procedures for storage media.
- Partner with certified disposal vendors and verify their compliance.
- Implement verification steps to confirm data destruction (e.g., certificates of destruction).
- Conduct regular reviews and audits of disposal processes.
Media Tracking
- Maintain a comprehensive inventory of all storage media, including location, status, and movement.
- Implement advanced tracking systems for real-time inventory management.
- Conduct regular reconciliation processes to ensure inventory accuracy.
- Update inventory records promptly following any changes.
Access Controls
- Implement multi-factor authentication (MFA) for access to storage media.
- Establish and document role-based access control policies.
- Monitor and log all access attempts to storage media.
- Regularly review and update access control policies and logs.
By following this detailed compliance checklist, organisations can effectively demonstrate their adherence to A.7.10 Storage Media requirements, ensuring robust management and protection of their information assets.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.7.10
Ready to streamline your compliance with A.7.10 Storage Media? Discover how ISMS.online can help you manage and protect your storage media with ease and efficiency.
Contact ISMS.online today to book a demo and see our powerful tools in action!
Let’s secure your organisation’s future together!