ISO 27001 A.7.4 Physical Security Monitoring Checklist
A.7.4 Physical Security Monitoring is a critical control within ISO/IEC 27001:2022 that ensures the security of physical environments through continuous and effective monitoring. This control focuses on detecting and responding to unauthorised access, breaches, and other security incidents in real-time.
Effective implementation of A.7.4 helps organisations protect their physical assets, maintain the integrity of their information systems, and ensure the safety of personnel.
In this comprehensive guide, we will delve into the key aspects of A.7.4 Physical Security Monitoring, outline common challenges faced by CISOs, and provide solutions for each challenge. Additionally, we will provide a detailed compliance checklist and explore how ISMS.online features can be leveraged to demonstrate compliance effectively.

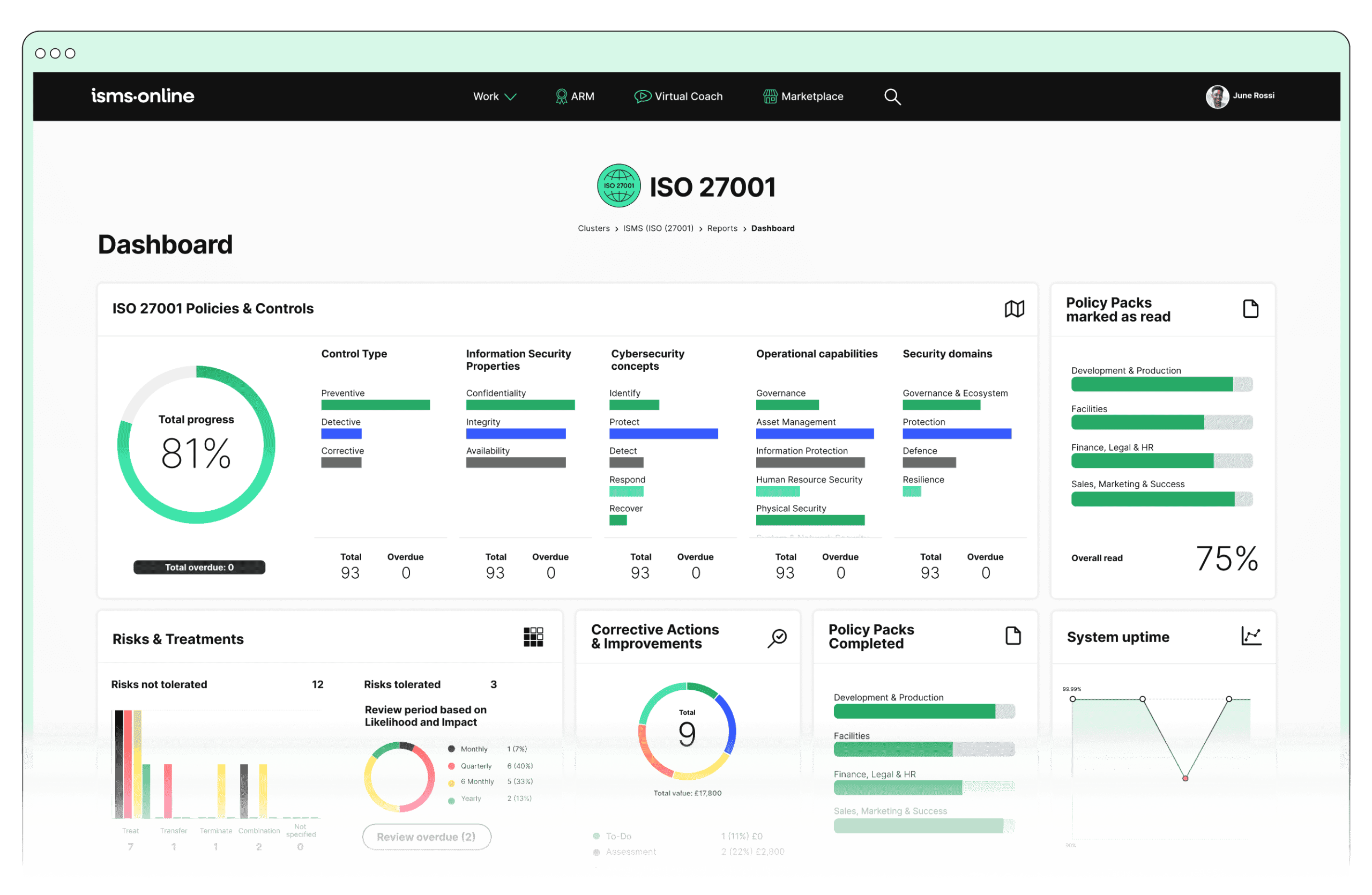
ISO 27001 made easy
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.7.4? Key Aspects and Common Challenges
Monitoring Measures
- High implementation costs for surveillance systems and advanced sensors.
- Integration issues with existing security infrastructure.
- Ensuring comprehensive coverage without blind spots.
- Solutions:
- Scalable Implementation: Start with high-priority areas and expand as budget allows.
- Infrastructure Assessment: Conduct thorough assessments to integrate new systems with minimal disruption.
- Regular Site Assessments: Identify and eliminate blind spots to ensure full coverage.
- Related ISO 27001 Clauses:
- Clause 8: Operation.
Common Challenges:
Incident Detection
- Difficulty in promptly identifying and distinguishing real incidents from false alarms.
- Ensuring timely reporting and logging of incidents.
- Training security personnel effectively to recognise and report incidents.
- Solutions:
- Advanced Analytics: Use machine learning to differentiate between real incidents and false alarms.
- Automated Systems: Implement automated incident reporting and logging.
- Regular Training Programmes: Conduct comprehensive training, including simulations and drills.
- Related ISO 27001 Clauses:
- Clause 8.2: Risk Assessment.
Common Challenges:
Response Procedures
- Developing clear, actionable response procedures that are understood and followed by all relevant personnel.
- Regularly updating and testing response procedures to keep them effective.
- Coordinating responses across different teams and locations.
- Solutions:
- Detailed Procedures: Develop with input from all stakeholders.
- Regular Updates and Tests: Schedule reviews and updates, incorporating lessons learned.
- Centralised Coordination: Establish a centralised incident response team.
- Related ISO 27001 Clauses:
- Clause 8.3: Risk Treatment.
Common Challenges:
Access Control Integration
- Integrating physical security monitoring systems with access control systems smoothly.
- Managing and auditing access logs effectively to ensure they are accurate and useful.
- Ensuring that integration does not compromise the performance or security of either system.
- Solutions:
- Compatible Systems: Choose systems designed for seamless integration or use middleware.
- Automated Log Management: Implement solutions for accuracy and ease of auditing.
- Regular Assessments: Conduct performance and security assessments to avoid vulnerabilities.
- Related ISO 27001 Clauses:
- Clause 9.1: Monitoring, Measurement, Analysis and Evaluation.
Common Challenges:
Data Retention and Analysis
- Balancing the need for data retention with privacy concerns and regulatory requirements.
- Storing and managing large volumes of surveillance data securely and efficiently.
- Analysing data effectively to identify patterns and improve security measures.
- Solutions:
- Clear Retention Policies: Ensure compliance with regulatory requirements and balance privacy concerns.
- Secure Storage Solutions: Use cloud-based services with encryption and access controls.
- Advanced Analytics Tools: Regularly review and analyse monitoring data for actionable insights.
- Related ISO 27001 Clauses:
- Clause 7.5: Documented Information.
Common Challenges:
Continuous Improvement
- Establishing a culture of continual improvement and learning from incidents.
- Implementing feedback mechanisms that provide actionable insights.
- Keeping up with evolving security threats and adapting measures accordingly.
- Solutions:
- Culture Promotion: Regular training, awareness programmes, and leadership support.
- Structured Feedback Mechanisms: Post-incident reviews and regular performance audits.
- Threat Intelligence Services: Stay informed and adapt security measures proactively.
- Related ISO 27001 Clauses:
- Clause 10: Improvement.
Common Challenges:

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.7.4
- Incident Management:
- Incident Tracker: Use this feature to log and track physical security incidents, ensuring prompt detection and documentation.
- Workflow: Manage response procedures effectively with predefined workflows for handling incidents.
- Notifications: Configure automatic notifications to alert relevant personnel immediately upon detection of a security incident.
- Reporting: Generate detailed reports on incidents and responses for review and continuous improvement.
- Audit Management:
- Audit Templates: Utilise customisable audit templates to periodically review and assess the effectiveness of physical security monitoring measures.
- Audit Plan: Schedule and manage audits to ensure regular evaluation of physical security controls.
- Corrective Actions: Document and track corrective actions to address any weaknesses identified during audits.
- Compliance Management:
- Regs Database: Access a comprehensive database of regulations and standards to ensure compliance with legal and organisational requirements for physical security monitoring.
- Alert System: Stay informed about changes in regulations and standards that may impact physical security measures.
- Reporting: Generate compliance reports to demonstrate adherence to A.7.4 and other relevant controls.
- Documentation Management:
- Doc Templates: Create and maintain documentation for physical security policies, procedures, and monitoring systems.
- Version Control: Manage document versions to ensure that the latest procedures and policies are always in use.
- Collaboration: Enable collaborative creation and review of documents related to physical security monitoring.
- Training and Awareness:
- Training Modules: Develop and deliver training programmes for security personnel on monitoring measures, incident detection, and response procedures.
- Training Tracking: Monitor and record the completion of training programmes to ensure all personnel are adequately prepared.
- Assessment: Evaluate the effectiveness of training through assessments and feedback mechanisms.
- Performance Tracking:
- KPI Tracking: Define and track key performance indicators related to physical security monitoring, such as response times and incident resolution rates.
- Trend Analysis: Analyse trends in security incidents and responses to identify areas for improvement and enhance overall security measures.
By leveraging these ISMS.online features, organisations can effectively demonstrate compliance with A.7.4 Physical Security Monitoring, ensuring robust security measures are in place, well-documented, and continuously improved.
Detailed Annex A.7.4 Compliance Checklist
Monitoring Measures
- Implement CCTV cameras at all critical entry points and sensitive areas.
- Install motion detectors and alarms in key locations.
- Ensure comprehensive coverage without blind spots.
- Regularly test and maintain all monitoring equipment.
Incident Detection
- Establish a process for prompt incident detection and logging.
- Train security personnel on recognising and reporting suspicious activities.
- Implement a system to distinguish between real incidents and false alarms.
- Ensure timely reporting of all incidents.
Response Procedures
- Define clear response procedures for physical security incidents.
- Communicate response procedures to all relevant personnel.
- Regularly test and update response procedures.
- Coordinate response efforts across different teams and locations.
Access Control Integration
- Integrate monitoring systems with access control systems.
- Maintain accurate logs of access events.
- Regularly audit access logs to ensure accuracy.
- Ensure the integration does not compromise system performance or security.
Data Retention and Analysis
- Retain surveillance footage and incident logs for a defined period.
- Ensure data retention practices comply with legal and organisational requirements.
- Store surveillance data securely and efficiently.
- Regularly analyse monitoring data to identify patterns and improve security measures.
Continuous Improvement
- Establish a culture of continual improvement in physical security.
- Implement feedback mechanisms for actionable insights.
- Regularly review and update physical security policies and controls.
- Adapt security measures to address evolving threats.
By following this compliance checklist, organisations can systematically address the challenges and demonstrate adherence to the requirements of A.7.4 Physical Security Monitoring in ISO/IEC 27001:2022.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.7.4
Ready to take your physical security monitoring to the next level? Contact ISMS.online today and book a demo to see how our comprehensive suite of tools can help you achieve and maintain compliance with ISO/IEC 27001:2022.
Our platform is designed to simplify the implementation of robust security measures, streamline compliance management, and ensure continuous improvement.
Reach out to our team directly to schedule your personalised demo. Let us help you secure your organisation’s physical environment and enhance your overall security posture.