ISO 27001 A.8.10 Information Deletion Checklist
A.8.10 Information Deletion in ISO 27001:2022 is a pivotal control focusing on the secure and complete removal of information that is no longer needed. This control is essential for preventing unauthorised access to sensitive data, mitigating the risk of data breaches, and ensuring compliance with regulatory obligations.
Implementing A.8.10 requires a structured approach, encompassing detailed policies, advanced deletion methods, thorough verification, clear responsibility assignment, and regular reviews.

ISO 27001 made easy
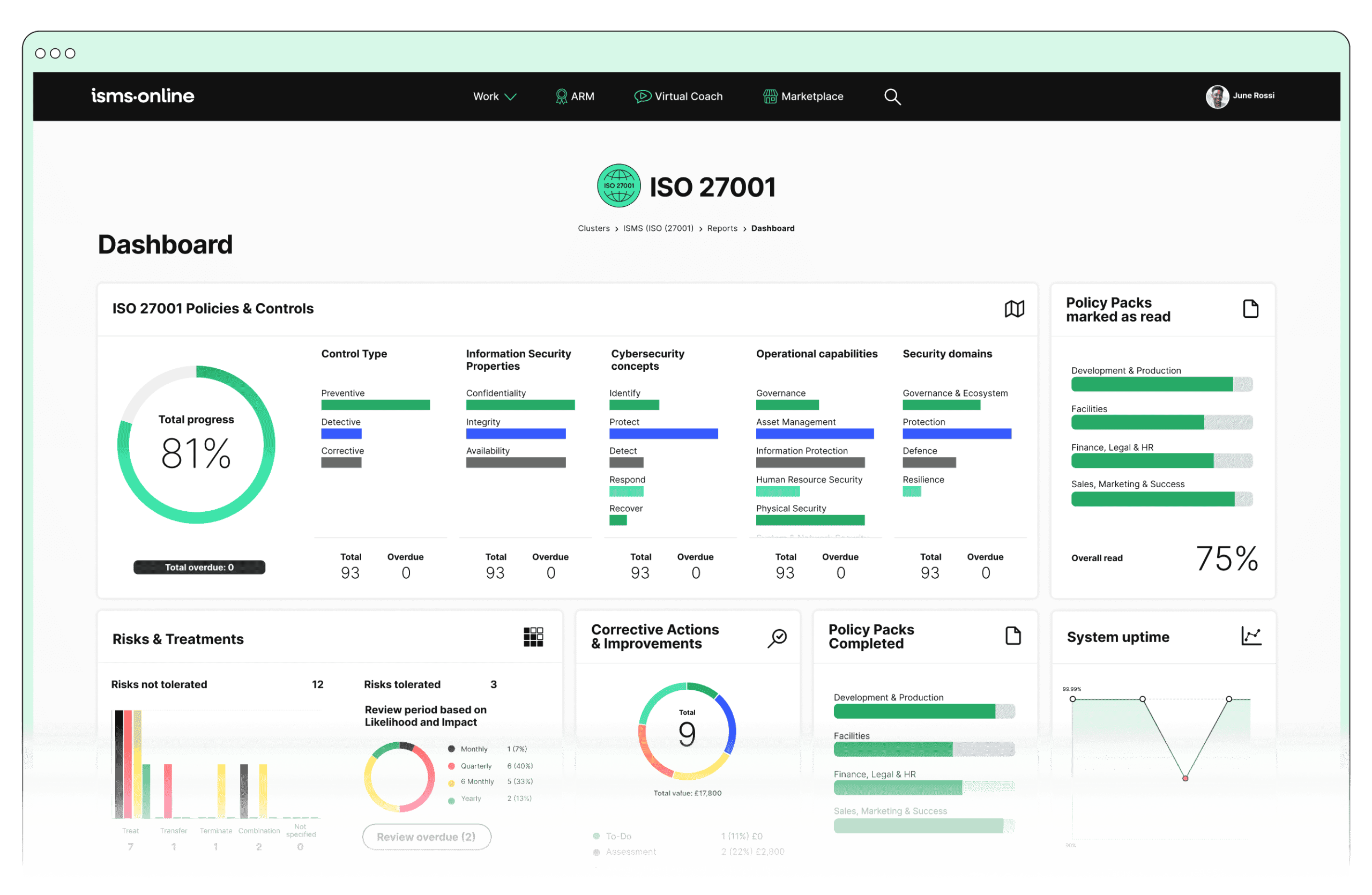
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.8.10? Key Aspects and Common Challenges
Data Retention Policy
- Solution: Utilise ISMS.online’s Policy Templates and Pack to establish robust data retention and deletion policies. These templates ensure comprehensive coverage, and Version Control and Document Access features maintain up-to-date policies accessible to all relevant stakeholders, ensuring compliance and accountability.
- Related ISO 27001 Clauses: Context of the Organisation, Leadership, and Planning
Challenge: Crafting a comprehensive data retention policy that aligns with diverse legal, regulatory, and business requirements across various data types and jurisdictions. Inconsistent policies can lead to accidental retention or premature deletion of critical data.
Secure Deletion Methods
- Solution: ISMS.online’s Asset Management features, such as the Asset Registry and Labelling System, assist in identifying and classifying information assets. This enables the selection of appropriate deletion methods, such as data wiping, degaussing, and physical destruction, ensuring thorough and secure data disposal.
- Related ISO 27001 Clauses: Support, Operation, and Performance Evaluation
Challenge: Implementing secure deletion methods that are effective across various storage media, including HDDs, SSDs, and cloud services. Ensuring that deleted data is irretrievable poses a technical challenge, especially with advanced data recovery techniques.
Verification and Documentation
- Solution: The Incident Tracker in ISMS.online’s Incident Management module provides detailed documentation of the deletion process, including who authorised and executed the deletion, the methods used, and the verification steps taken. This ensures that all actions are recorded and can be reviewed during audits, enhancing transparency and accountability.
- Related ISO 27001 Clauses: Documented Information, Monitoring, Measurement, Analysis, and Evaluation
Challenge: Ensuring comprehensive verification and documentation of information deletion processes, which is critical for audit readiness and compliance verification.
Responsibility Assignment
- Solution: ISMS.online’s Policy Management facilitates clear role definitions and responsibilities. This includes specifying who is authorised to perform deletions, who verifies them, and who audits the processes, ensuring that all personnel are trained and aware of their duties.
- Related ISO 27001 Clauses: Organisational Roles, Responsibilities, and Authorities, and Awareness
Challenge: Clearly defining and communicating roles and responsibilities within the information deletion process to prevent gaps or unauthorised actions.
Periodic Review
- Solution: ISMS.online’s Audit Management features, including Audit Templates and Documentation, support regular audits and reviews of deletion processes. The Compliance Management tools, such as the Regs Database and Alert System, ensure that the organisation stays informed about regulatory changes, enabling timely updates to policies and procedures.
- Related ISO 27001 Clauses: Internal Audit, Management Review, and Continual Improvement
Challenge: Regularly reviewing and updating deletion procedures to adapt to new technological advancements, emerging security threats, and evolving regulatory landscapes.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.8.10
- Policy Management:
- Policy Templates and Pack: Create comprehensive data retention and deletion policies, covering all necessary aspects and aligning with legal requirements.
- Version Control and Document Access: Maintain up-to-date policies and ensure they are accessible to all stakeholders, supporting transparency and accountability.
- Incident Management:
- Incident Tracker: Record and manage all incidents related to data deletion, documenting each step to ensure proper handling and verification.
- Asset Management:
- Asset Registry and Labelling System: Track and classify information assets, ensuring appropriate deletion methods are applied and documented.
- Monitoring and Access Control: Control access to data, ensuring that only authorised personnel can perform or verify deletions.
- Audit Management:
- Audit Templates and Documentation: Conduct regular audits to verify compliance with information deletion procedures and document findings.
- Corrective Actions: Implement and track corrective actions to address any identified issues, ensuring continuous improvement.
- Compliance Management:
- Regs Database and Alert System: Stay informed about changes in laws and regulations related to data retention and deletion.
- Reporting and Training Modules: Provide training on secure deletion practices and generate compliance reports to demonstrate adherence to policies.
Detailed Annex A.8.10 Compliance Checklist
- Data Retention Policy
- Develop a comprehensive data retention policy covering all data types and retention periods.
- Ensure the policy aligns with relevant legal, regulatory, and business requirements.
- Regularly review and update the policy to reflect changes in laws, regulations, or business needs.
- Secure Deletion Methods
- Identify all information assets and classify them according to sensitivity and storage media type.
- Implement secure deletion methods appropriate for each type of storage medium, such as data wiping, degaussing, or physical destruction.
- Test deletion methods periodically to ensure they are effective and data cannot be recovered.
- Verification and Documentation
- Document all deletion processes, including the methods used, verification steps taken, and any issues encountered.
- Maintain a log of who authorised and performed the deletions, with timestamps.
- Regularly audit deletion records to ensure compliance with the policy and identify any areas for improvement.
- Responsibility Assignment
- Clearly define and assign roles and responsibilities for all aspects of the information deletion process.
- Ensure all personnel involved are trained and aware of their responsibilities.
- Provide ongoing training and updates as policies and procedures evolve.
- Periodic Review
- Schedule and conduct regular reviews of deletion procedures to ensure they remain effective and compliant.
- Update procedures as needed to address new technologies, threats, or regulatory requirements.
- Document and communicate any changes in procedures to all relevant stakeholders.
By addressing these common challenges with the comprehensive features offered by ISMS.online, a Chief Information Security Compliance Officer (CICSO) can ensure the secure and compliant deletion of information, protecting the organisation from potential data breaches and compliance issues. This detailed approach not only meets but exceeds the requirements of ISO 27001:2022, ensuring robust information security practices are in place.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.8.10
Ready to elevate your information security practices to the next level?
Discover how ISMS.online can streamline your compliance with ISO 27001:2022, including the critical A.8.10 Information Deletion control. Our comprehensive platform offers everything you need to implement and manage secure deletion processes, ensuring your organisation remains compliant and protected against data breaches.
Take the first step towards robust information security management today!
Contact ISMS.online to schedule a personalised demo and see how our features can transform your compliance efforts. Our experts are ready to guide you through the platform and answer any questions you may have. Secure your data, streamline your compliance, and empower your team with ISMS.online.