ISO 27001 A.8.11 Data Masking Checklist
A.8.11 Data Masking in ISO 27001:2022 is essential for protecting sensitive data by transforming it into a format that is unusable by unauthorised individuals, yet still functional for business operations like development, testing, and analytics.
This practice helps maintain privacy, prevent data breaches, and ensure regulatory compliance.
Scope of Annex A.8.11
- Techniques: Includes substitution, shuffling, encryption, nulling out, and data averaging. These methods replace sensitive data with fictional, yet realistic values, protecting the data while maintaining its usability.
- Scope:
- Data at Rest: Stored data in databases or files.
- Data in Use: Data actively processed by applications.
- Data in Transit: Data being transferred over networks.
- Use Cases: Applies to development/testing environments, analytics/reporting, and outsourcing/cloud services.

ISO 27001 made easy
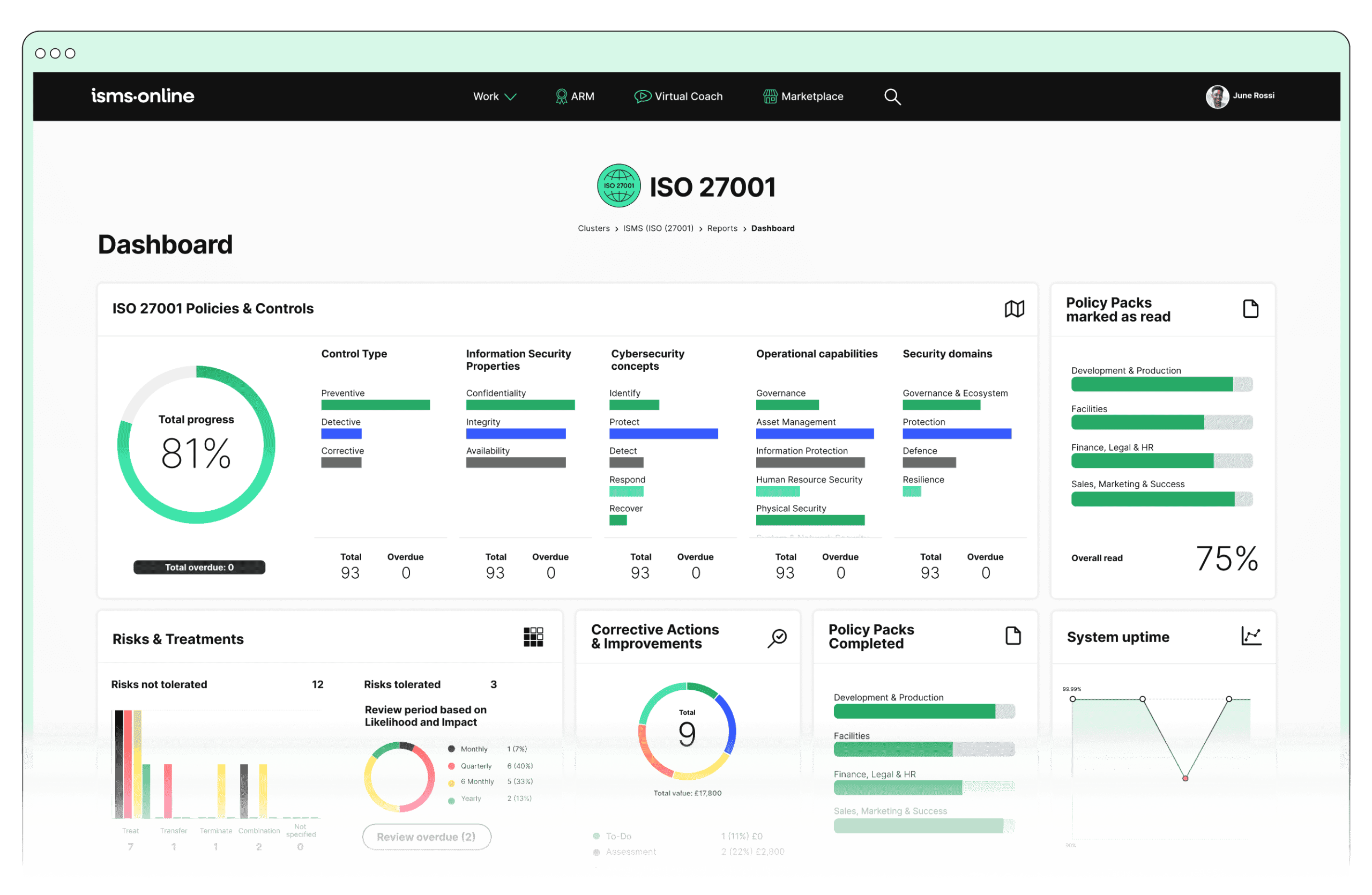
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.8.11? Key Aspects and Common Challenges
1. Policy Development
Challenge: Creating a comprehensive data masking policy aligned with organisational goals.
Solution: Use ISMS.online’s policy templates to craft a detailed policy. Utilise Policy Communication tools to disseminate and ensure understanding organisation-wide.
Associated ISO 27001 Clauses: Information Security Policy; Management Direction for Information Security.
2. Technique Selection
Challenge: Choosing appropriate data masking techniques.
Solution: Conduct a risk assessment to determine the most effective techniques. Document the decision-making process in ISMS.online’s Documented Procedures for transparency and compliance.
Associated ISO 27001 Clauses: Risk Assessment; Treatment of Risks.
3. Integration with Existing Systems
Challenge: Integrating data masking with legacy systems.
Solution: Conduct compatibility assessments and plan the integration carefully. Utilise ISMS.online’s Data Handling Controls for seamless implementation.
Associated ISO 27001 Clauses: Information Security in Project Management; Secure Development.
4. Data Volume and Complexity
Challenge: Managing large, complex datasets while ensuring data integrity.
Solution: Apply consistent data masking procedures across all datasets using ISMS.online’s Data Protection tools. Regular audits ensure compliance and integrity.
Associated ISO 27001 Clauses: Asset Management; Data Masking Controls.
5. Training and Awareness
Challenge: Ensuring staff understand and implement data masking correctly.
Solution: Develop training programmes via ISMS.online’s Training Modules and conduct awareness sessions regularly.
Associated ISO 27001 Clauses: Competence, Training, and Awareness.
6. Audit and Compliance
Challenge: Demonstrating compliance with data masking requirements.
Solution: Maintain detailed logs of data masking activities using ISMS.online’s Audit Trail. Use Compliance Reporting tools for generating necessary reports.
Associated ISO 27001 Clauses: Internal Audit; Management Review; Compliance Obligations.
7. Performance Impact
Challenge: Avoiding negative impacts on system performance.
Solution: Regularly monitor system performance post-implementation using ISMS.online’s Performance Monitoring tools. Optimise processes as necessary to maintain system efficiency and effectiveness.
Associated ISO 27001 Clauses: Performance Evaluation; Continual Improvement.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.8.11
- Policy Management: Create and disseminate comprehensive data masking policies using ISMS.online’s templates and communication tools.
- Data Protection: Document and standardise masking techniques and procedures, ensuring consistent implementation.
- Training and Awareness: Offer targeted training programmes and ongoing awareness sessions to ensure staff are knowledgeable about data masking practices.
- Audit and Compliance Management: Maintain an audit trail and generate compliance reports to support internal and external audits.
Detailed Annex A.8.11 Compliance Checklist
Policy Development:
- Develop a comprehensive data masking policy using ISMS.online’s policy templates.
- Communicate the policy effectively across the organisation using Policy Communication tools.
Technique Selection:
- Identify sensitive data requiring masking.
- Select appropriate data masking techniques (substitution, shuffling, encryption) based on data type and usage context.
- Document selected techniques in ISMS.online’s Documented Procedures section.
Integration with Existing Systems:
- Evaluate compatibility of data masking solutions with existing systems.
- Implement data masking controls in coordination with Data Handling Controls to ensure seamless integration.
Data Volume and Complexity:
- Assess the volume and complexity of data to be masked.
- Apply data masking procedures consistently across all relevant datasets, utilising ISMS.online’s Data Protection tools.
Training and Awareness:
- Develop and deliver training programmes on data masking techniques via ISMS.online’s Training Modules.
- Conduct awareness sessions to ensure all employees understand the importance and implementation of data masking.
Audit and Compliance:
- Maintain detailed logs of data masking activities in the ISMS.online Audit Trail.
- Regularly review logs and generate compliance reports using Compliance Reporting features.
Performance Impact:
- Monitor system performance post-implementation of data masking.
- Optimise masking processes as necessary using ISMS.online’s Performance Monitoring tools.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.8.11
Ready to safeguard your sensitive information and ensure compliance with ISO 27001:2022?
At ISMS.online, we provide the tools and expertise to help you implement robust data masking practices, streamline your compliance efforts, and protect your organisation from potential data breaches.
Contact us today to learn more about how our comprehensive platform can support your information security needs. Book a demo and discover how ISMS.online can help you achieve compliance with A.8.11 Data Masking and beyond, while enhancing your overall security posture.