ISO 27001 A.8.12 Data Leakage Prevention Checklist
A.8.12 Data Leakage Prevention within ISO/IEC 27001:2022 is a vital aspect of an organisation’s information security management system (ISMS). It involves implementing measures and controls to prevent unauthorised or accidental disclosure of sensitive information, ensuring data protection both within and outside the organisation. The objective is to safeguard sensitive data from unintended access, sharing, or leakage, thereby maintaining its confidentiality, integrity, and availability.
This section outlines a comprehensive approach required for effective data leakage prevention, addressing technical, administrative, and procedural controls. It emphasises a structured and proactive strategy to identify, monitor, and protect sensitive data from unauthorised access or leakage.

ISO 27001 made easy
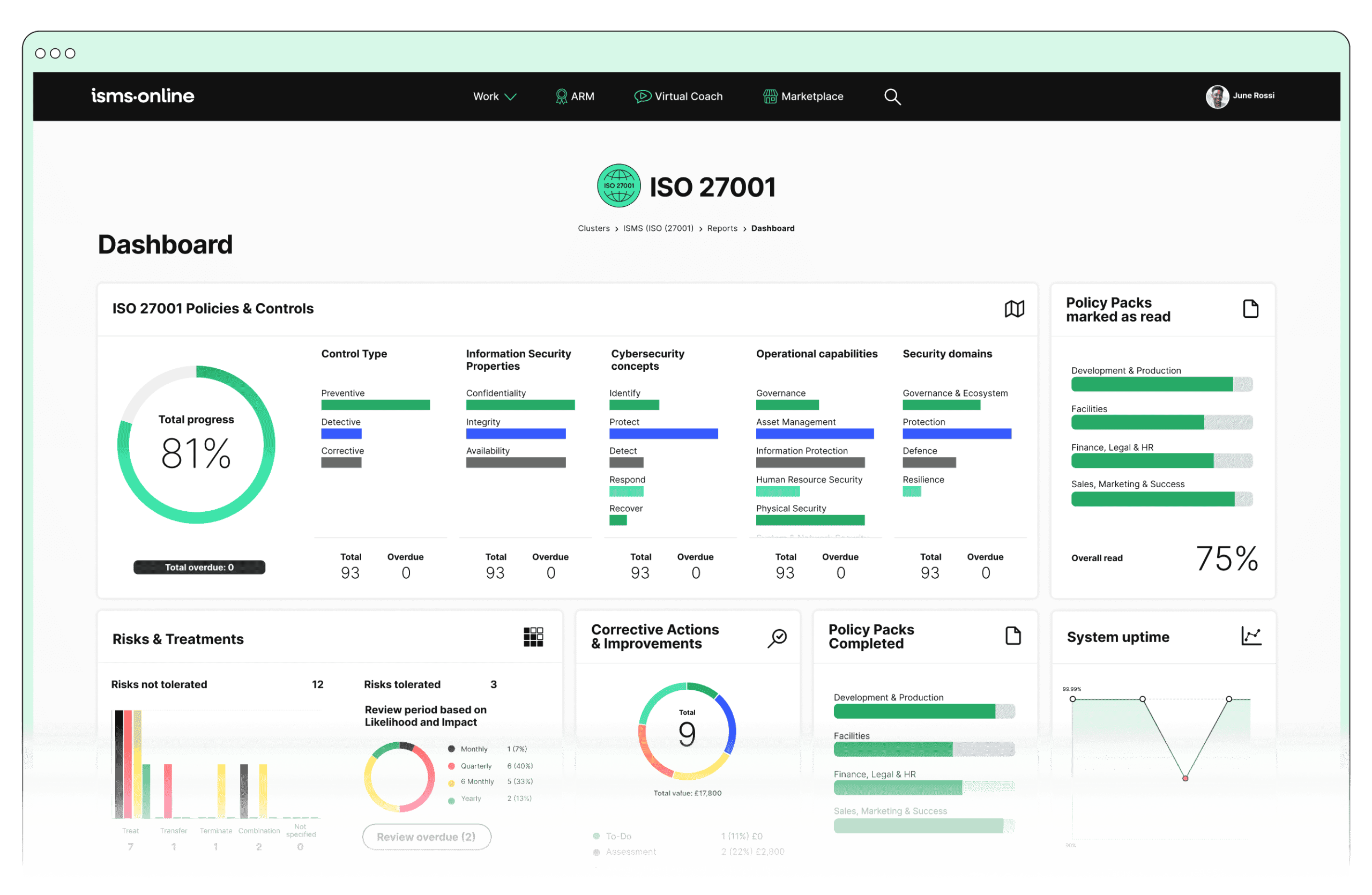
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.8.12? Key Aspects and Common Challenges
1. Data Identification and Classification
Challenge: Determining which data is sensitive or critical can be complex, especially in large organisations with diverse data sets. Inconsistent or inadequate classification can lead to gaps in data protection.
Solutions:
- Implement a thorough data inventory process to identify and catalogue all data assets.
- Develop and maintain a comprehensive data classification policy that categorises data based on sensitivity, criticality, and regulatory requirements.
- Conduct regular training and awareness programmes for employees to ensure proper data handling practices.
Related ISO 27001 Clauses: Clause 7.5 (Documented Information), Clause 8.2 (Risk Assessment), Clause 8.3 (Risk Treatment).
2. Monitoring and Detection
Challenge: Implementing comprehensive monitoring systems can be resource-intensive and may require advanced technical expertise. Balancing thorough monitoring with privacy concerns and regulatory compliance is also challenging.
Solutions:
- Utilise data loss prevention (DLP) tools and network monitoring systems to detect potential data leaks.
- Establish clear guidelines for monitoring sensitive data flows, including data transfers, uploads, and downloads.
- Implement automated alert systems for unusual or unauthorised activities and integrate with incident response protocols.
Related ISO 27001 Clauses: Clause 9.1 (Monitoring, Measurement, Analysis and Evaluation), Clause 10.1 (Continual Improvement).
3. Access Control and Authorisation
Challenge: Establishing and maintaining strict access controls can be challenging, particularly in dynamic environments where roles and responsibilities change frequently. Ensuring that access rights are regularly reviewed and updated is crucial but often overlooked.
Solutions:
- Implement role-based access controls (RBAC) and enforce the principle of least privilege, ensuring users only have access to the data necessary for their role.
- Regularly audit and review access rights, adjusting permissions as necessary to reflect changes in roles or responsibilities.
- Utilise multi-factor authentication (MFA) to enhance security for accessing sensitive data.
Related ISO 27001 Clauses: Clause 9.2 (Internal Audit), Clause 9.3 (Management Review), Clause 6.1 (Actions to Address Risks and Opportunities).
4. Data Encryption
Challenge: Implementing encryption effectively requires understanding the data flow and identifying all points where data is at rest or in transit. Ensuring that encryption keys are managed securely and efficiently is another critical challenge.
Solutions:
- Deploy encryption technologies for data at rest and data in transit, using industry-standard cryptographic algorithms.
- Implement robust encryption key management practices, including secure storage, access control, and regular key rotation.
- Regularly review and update encryption protocols to align with current best practices and evolving threats.
Related ISO 27001 Clauses: Clause 8.2 (Risk Assessment), Clause 8.3 (Risk Treatment), Clause 7.5 (Documented Information).
5. Policy Enforcement
Challenge: Enforcing DLP policies consistently across all departments and systems can be difficult. Resistance to change and lack of awareness or understanding among staff can hinder effective policy implementation.
Solutions:
- Develop clear and comprehensive DLP policies, including acceptable use policies and guidelines for data handling.
- Use technical controls, such as DLP software, to enforce policies and prevent unauthorised data transfers.
- Conduct regular training and awareness sessions to ensure all employees understand and adhere to DLP policies.
Related ISO 27001 Clauses: Clause 5.2 (Policy), Clause 7.2 (Competence), Clause 7.3 (Awareness).
6. Incident Response
Challenge: Developing and executing a comprehensive incident response plan for data leakage incidents requires coordination across various teams. Ensuring timely detection, accurate assessment, and swift response can be challenging, particularly in complex or large-scale incidents.
Solutions:
- Establish a detailed incident response plan, outlining roles, responsibilities, and actions to be taken in the event of a data leak.
- Implement a communication plan for notifying stakeholders, including affected individuals, regulatory bodies, and partners.
- Conduct regular incident response drills and simulations to test and improve the effectiveness of the response plan.
- Document and analyse incidents to identify root causes and implement corrective actions to prevent recurrence.
Related ISO 27001 Clauses: Clause 10.1 (Continual Improvement), Clause 8.2 (Risk Assessment), Clause 8.3 (Risk Treatment).

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.8.12
1. Risk Management:
- Dynamic Risk Map: Visualise and manage risks related to data leakage, ensuring proactive identification and mitigation.
- Risk Bank: Store and access documented risks, including those specific to data leakage, with detailed assessments and treatments.
2. Policy Management:
- Policy Templates and Pack: Access pre-built templates for creating robust DLP policies, ensuring consistent application across the organisation.
- Version Control: Track and manage policy updates, ensuring that the latest DLP policies are always in place and communicated effectively.
3. Incident Management:
- Incident Tracker: Log and monitor incidents related to data leakage, facilitating quick response and resolution.
- Workflow and Notifications: Automate the incident management process, ensuring timely alerts and coordinated responses.
4. Audit Management:
- Audit Templates and Plan: Conduct audits to verify compliance with DLP policies and controls, identifying areas for improvement.
- Corrective Actions: Document and track actions taken to address non-conformities or weaknesses in DLP controls.
5. Compliance and Documentation:
- Regs Database and Alert System: Stay informed about regulatory requirements and updates related to data protection and leakage prevention.
- Documentation Tools: Maintain comprehensive records of policies, incidents, audits, and corrective actions, demonstrating due diligence in DLP.
Detailed Annex A.8.12 Compliance Checklist
1. Data Identification and Classification
Identify and catalogue all sensitive and critical data within the organisation.
Implement a data classification scheme that categorises data based on sensitivity and criticality.
Regularly review and update the data classification scheme to ensure it remains accurate and relevant.
Train staff on recognising and appropriately handling classified data.
2. Monitoring and Detection
Deploy monitoring tools to track data flows and detect potential data leaks.
Configure alerts for unusual or unauthorised data activities.
Ensure monitoring tools comply with privacy regulations and respect user privacy.
Regularly review and update monitoring configurations to adapt to new threats.
3. Access Control and Authorisation
Define and enforce strict access control policies based on roles and responsibilities.
Implement multi-factor authentication for accessing sensitive data.
Conduct regular access reviews to ensure only authorised personnel have access to sensitive data.
Update access rights promptly in response to role changes or employee departures.
4. Data Encryption
Identify all points where sensitive data is stored or transmitted.
Implement encryption for data at rest and in transit using strong cryptographic methods.
Securely manage and store encryption keys.
Regularly review and update encryption practices to align with current best practices.
5. Policy Enforcement
Develop and communicate clear DLP policies to all employees.
Use technical controls to enforce DLP policies across all systems and devices.
Conduct regular training sessions to reinforce the importance of DLP policies.
Monitor compliance with DLP policies and address any violations promptly.
6. Incident Response
Develop an incident response plan specifically for data leakage incidents.
Establish a clear process for detecting, assessing, and responding to data leaks.
Train response teams on their roles and responsibilities in the event of a data leak.
Conduct regular drills and simulations to test the effectiveness of the incident response plan.
Document and review each incident to identify lessons learned and improve future responses.
Using these ISMS.online features and following the compliance checklist, organisations can effectively demonstrate compliance with A.8.12 Data Leakage Prevention. This comprehensive approach ensures that sensitive information is protected against unauthorised access, minimising the risk of data breaches and enhancing the overall security posture of the organisation.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.8.12
Ready to take your data protection to the next level?
Don’t leave your sensitive information vulnerable to unauthorised access or accidental leaks. With ISMS.online, you can seamlessly implement and manage comprehensive Data Leakage Prevention measures, ensuring compliance with ISO/IEC 27001:2022 standards.
Book a demo today and discover how ISMS.online can transform your information security management. Our platform offers intuitive tools and expert support to help you safeguard your organisation’s critical data, streamline compliance processes, and stay ahead of evolving threats.