ISO 27001 A.8.18 Use of Privileged Utility Programs Checklist
The control A.8.18 Use of Privileged Utility Programs within ISO 27001:2022 is essential for ensuring the secure usage and control of utility programs that have elevated privileges. These programs, due to their extensive access and control over systems, can pose significant security risks if misused or compromised.
Effective management of privileged utility programs is crucial to maintaining the integrity, confidentiality, and availability of information systems. Below is a comprehensive explanation of this control, including common challenges faced by a Chief Information Security Compliance Officer (CISCO), relevant ISMS.online features, a detailed compliance checklist, and solutions for common challenges. Relevant ISO 27001:2022 clauses and requirements are integrated into each section to ensure comprehensive coverage.

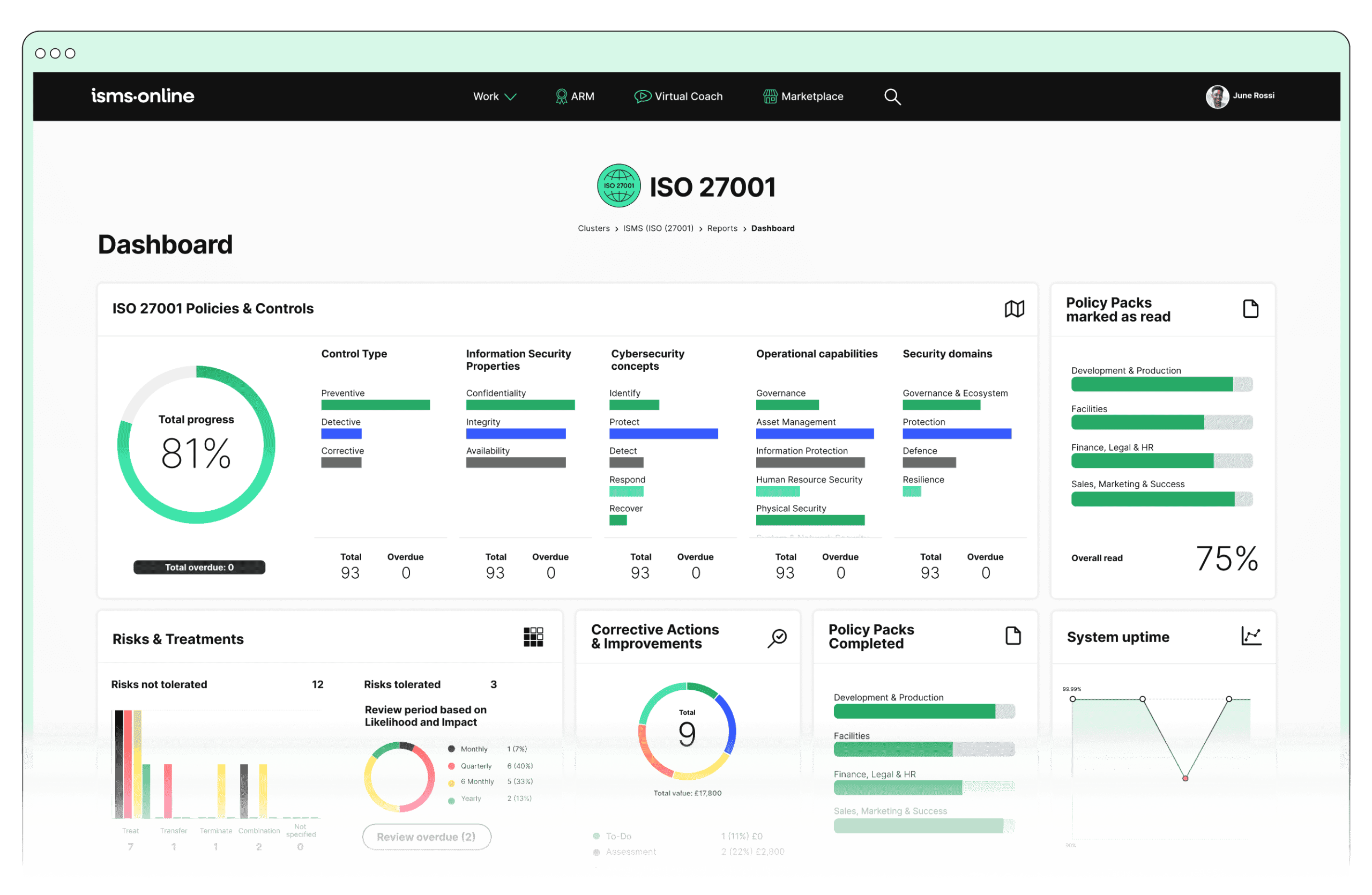
ISO 27001 made easy
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.8.18? Key Aspects and Common Challenges
1. Identification and Documentation
Task: Identify all privileged utility programs within the organisation.
Challenge: Ensuring comprehensive identification and documentation of all utility programs, especially in large or complex IT environments where undocumented tools may exist. Overlooking any utility program could lead to significant security gaps.
Solution: Implement a thorough inventory process and use automated discovery tools to ensure all utility programs are identified and documented. Regularly review and update the inventory to reflect changes in the IT environment.
Related ISO 27001 Clauses: 7.5.1 – Documented Information
Task: Maintain comprehensive documentation, including the purpose and usage of each utility program.
Challenge: Keeping documentation up-to-date with changes in software and user roles, and ensuring it is accessible yet secure.
Solution: Establish a document management system with version control and access restrictions. Assign responsibility for maintaining documentation to specific roles to ensure accountability.
Related ISO 27001 Clauses: 7.5.2 – Creating and Updating
2. Access Control
Task: Restrict access to privileged utility programs to authorised personnel only.
Challenge: Managing and verifying access rights, especially in dynamic environments where roles and responsibilities frequently change.
Solution: Implement role-based access control (RBAC) and conduct regular access reviews to ensure that only authorised personnel have access. Use automated access management tools to streamline the process.
Related ISO 27001 Clauses: 9.2 – Internal Audit
Task: Implement strong authentication methods to verify the identity of users accessing these programs.
Challenge: Balancing security and usability to ensure robust authentication without hindering productivity.
Solution: Use multi-factor authentication (MFA) for accessing privileged utility programs. Regularly review authentication methods to ensure they meet current security standards.
Related ISO 27001 Clauses: 9.3 – Management Review
Task: Apply the principle of least privilege, granting access only to those who require it for their job functions.
Challenge: Determining and enforcing least privilege can be complex, requiring constant review and adjustment.
Solution: Use access control tools that support the principle of least privilege and automate the process of granting and revoking access based on job roles and responsibilities.
Related ISO 27001 Clauses: 6.1.2 – Information Security Risk Assessment
3. Usage Monitoring and Logging
Task: Monitor and log the use of privileged utility programs to detect and respond to unauthorised or inappropriate usage.
Challenge: Implementing effective monitoring systems that generate actionable insights without overwhelming administrators with false positives.
Solution: Deploy advanced security information and event management (SIEM) systems that can filter and prioritise alerts. Use machine learning algorithms to detect anomalies and reduce false positives.
Related ISO 27001 Clauses: 9.1 – Monitoring, Measurement, Analysis and Evaluation
Task: Ensure logs are protected from unauthorised access and tampering.
Challenge: Securing log data while ensuring it is readily available for review and analysis.
Solution: Use encryption and access controls to protect log data. Implement regular log integrity checks to detect and address any tampering.
Related ISO 27001 Clauses: 7.5.3 – Control of Documented Information
4. Training and Awareness
Task: Provide training to users on the proper and secure use of privileged utility programs.
Challenge: Ensuring training is comprehensive, up-to-date, and engaging to encourage user participation.
Solution: Develop interactive and scenario-based training modules. Regularly update training content to reflect new threats and best practices. Track training completion and effectiveness through assessments.
Related ISO 27001 Clauses: 7.2 – Competence
Task: Raise awareness about the potential risks and security implications associated with these programs.
Challenge: Maintaining a high level of awareness and vigilance among users, particularly in large or geographically dispersed organisations.
Solution: Conduct regular awareness campaigns using various communication channels (e.g., emails, posters, workshops). Use gamification to make learning engaging and effective.
Related ISO 27001 Clauses: 7.3 – Awareness
5. Regular Review and Audits
Task: Conduct regular reviews and audits of the usage and access controls of privileged utility programs.
Challenge: Allocating sufficient resources and expertise to conduct thorough and frequent audits.
Solution: Schedule periodic audits and reviews, leveraging both internal and external auditors. Use audit management software to streamline the process and ensure comprehensive coverage.
Related ISO 27001 Clauses: 9.2 – Internal Audit
Task: Ensure that the programs are used in compliance with the organisation’s security policies and procedures.
Challenge: Detecting and addressing non-compliance in a timely manner, particularly when faced with resource constraints.
Solution: Implement automated compliance monitoring tools that provide real-time alerts and reports on non-compliance. Establish a clear process for addressing and remediating compliance issues.
Related ISO 27001 Clauses: 10.1 – Nonconformity and Corrective Action
6. Policy Development
Task: Develop and enforce policies governing the use of privileged utility programs, detailing acceptable use, access control measures, and monitoring requirements.
Challenge: Creating policies that are both comprehensive and adaptable to evolving threats and organisational changes.
Solution: Involve stakeholders from various departments in the policy development process to ensure coverage of all relevant aspects. Regularly review and update policies to keep pace with technological advancements and emerging threats.
Related ISO 27001 Clauses: 5.2 – Information Security Policy

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.8.18
ISMS.online provides several features that are instrumental in demonstrating compliance with the control “A.8.18 Use of Privileged Utility Programs”:
- Risk Management:
- Risk Bank: Document and manage risks associated with the use of privileged utility programs.
- Dynamic Risk Map: Visualise and track risks in real-time to ensure they are adequately managed and mitigated.
- Policy Management:
- Policy Templates: Utilise pre-built templates to create comprehensive policies for the use of privileged utility programs.
- Policy Pack: Store, access, and manage policy documents with version control and easy distribution to relevant stakeholders.
- Access Control:
- Document Access: Control access to documentation and policies related to privileged utility programs, ensuring only authorised personnel can view or edit these documents.
- Training and Awareness:
- Training Modules: Develop and deliver training programmes on the secure use of privileged utility programs.
- Training Tracking: Monitor and track the completion of training sessions to ensure all relevant personnel are educated on the proper usage and risks.
- Incident Management:
- Incident Tracker: Log and track incidents related to the misuse of privileged utility programs, enabling quick response and resolution.
- Workflow and Notifications: Implement workflows for incident response and set up notifications to alert relevant personnel when incidents occur.
- Audit Management:
- Audit Templates: Conduct regular audits using predefined templates to assess compliance with policies and procedures.
- Audit Plan: Develop and execute audit plans to regularly review the use and control of privileged utility programs.
- Corrective Actions: Document and track corrective actions to address any identified issues during audits.
- Compliance Management:
- Regs Database: Maintain a database of regulatory requirements and ensure that policies for privileged utility programs are aligned with these requirements.
- Alert System: Receive alerts about changes in regulations or standards that may affect the management of privileged utility programs.
Detailed Annex A.8.18 Compliance Checklist
- Identification and Documentation:
- Conduct a thorough inventory of all privileged utility programs.
- Document the purpose and usage of each utility program.
- Regularly update the documentation to reflect changes in software and user roles.
- Ensure documentation is accessible yet secure.
- Access Control:
- Restrict access to privileged utility programs to authorised personnel only.
- Implement strong authentication methods (e.g., multi-factor authentication) for accessing privileged utility programs.
- Apply the principle of least privilege to all access controls.
- Regularly review and update access rights to reflect changes in roles and responsibilities.
- Usage Monitoring and Logging:
- Implement monitoring systems to log the use of privileged utility programs.
- Regularly review logs for unauthorised or inappropriate usage.
- Protect logs from unauthorised access and tampering.
- Ensure logs are readily available for review and analysis.
- Training and Awareness:
- Develop and deliver comprehensive training programmes on the secure use of privileged utility programs.
- Track and monitor the completion of training sessions.
- Regularly update training content to reflect evolving threats and best practices.
- Conduct awareness campaigns to highlight the risks associated with privileged utility programs.
- Regular Review and Audits:
- Conduct regular reviews of access controls for privileged utility programs.
- Schedule and execute frequent audits to assess compliance with policies and procedures.
- Allocate sufficient resources and expertise for thorough audits.
- Document and address non-compliance issues in a timely manner.
- Policy Development:
- Develop comprehensive policies governing the use of privileged utility programs.
- Ensure policies detail acceptable use, access control measures, and monitoring requirements.
- Regularly review and update policies to adapt to evolving threats and organisational changes.
- Communicate policies effectively to all relevant personnel.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.8.18
Ready to enhance your information security management system and ensure compliance with ISO 27001:2022?
ISMS.online offers the tools and support you need to manage privileged utility programs securely and efficiently.
Contact ISMS.online today to book a demo and discover how our platform can help you streamline your compliance processes, mitigate risks, and protect your organisation’s valuable assets.