ISO 27001 A.8.2 Privileged Access Rights Checklist
A.8.2 Privileged Access Rights in ISO/IEC 27001:2022 is essential for managing and restricting elevated access privileges within an organisation.
This control ensures that sensitive and critical information and systems are only accessible to authorised personnel, adhering to the principles of least privilege and need-to-know.
Effective implementation mitigates risks associated with unauthorised access, insider threats, and potential data breaches, which can significantly impact an organisation’s operations and reputation.

ISO 27001 made easy
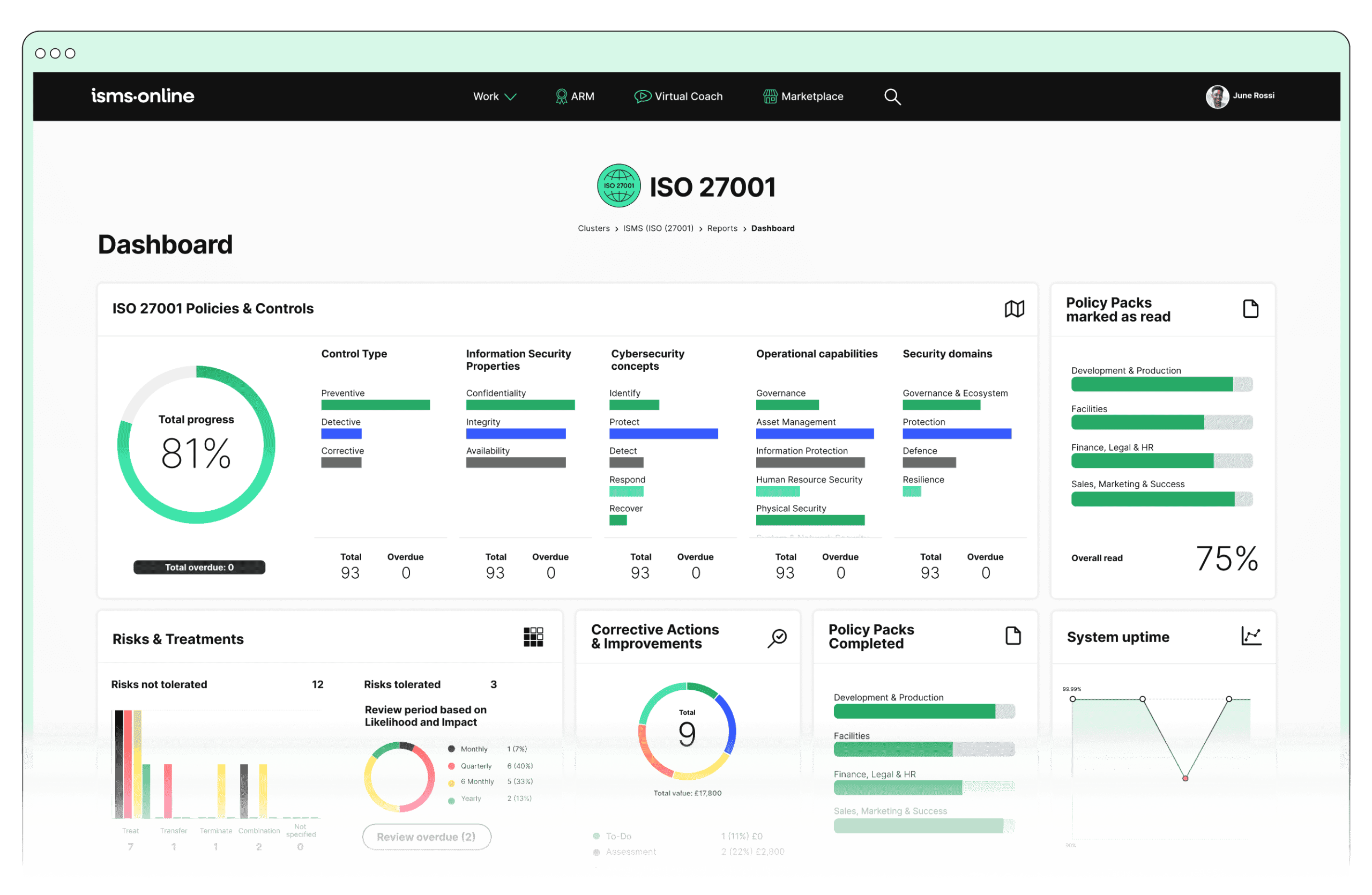
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.8.2? Key Aspects and Common Challenges
Key Aspects of A.8.2 Privileged Access Rights:
1. Definition and Management:
Challenges:
- Identifying All Privileged Accounts: Complex IT environments with numerous systems can obscure visibility into all privileged accounts, including those in legacy systems or shadow IT.
- Role Definition: Defining roles with associated access rights requires understanding diverse functions and data sensitivity across the organisation.
Solutions:
- Comprehensive Account Audits: Regular audits ensure identification of all privileged accounts, both system-level and application-level.
- Cross-Departmental Collaboration: Engaging with departments helps accurately define roles and necessary access levels, adapting as structures and processes evolve.
Related ISO 27001 Clauses: 4.1, 4.2, 7.1, 7.2, 7.3, 9.1.
2. Authorisation and Approval:
Challenges:
- Approval Process Bottlenecks: Poorly structured processes or unavailable approvers can delay approvals, impacting operations.
- Consistency in Policy Enforcement: Large organisations with multiple approvers may struggle to ensure uniform policy enforcement.
Solutions:
- Automated Workflow Systems: Streamline approvals, ensuring timely and consistent authorisation of privileged access requests.
- Standardised Approval Criteria: Clear, standardised criteria ensure uniform application of policies.
Related ISO 27001 Clauses: 6.1, 6.2, 7.5.
3. Monitoring and Review:
Challenges:
- Determining Review Frequency: Balancing review frequency to avoid security gaps and resource strain.
- Detecting Anomalies: Advanced monitoring capabilities are needed to distinguish between legitimate and suspicious activities.
Solutions:
- Risk-Based Review Scheduling: Prioritise reviews based on data sensitivity and misuse impact.
- Advanced Monitoring Tools: Real-time monitoring and anomaly detection using AI and machine learning.
Related ISO 27001 Clauses: 9.1, 9.2, 9.3.
4. Accountability and Tracking:
Challenges:
- Comprehensive and Secure Logging: Ensuring secure, tamper-proof logging of all privileged actions.
- Log Data Analysis: Managing and analysing large volumes of log data to detect incidents.
Solutions:
- Secure Logging Infrastructure: Implement tamper-proof logging systems for accurate records.
- Automated Analysis and Reporting: Tools for analysing logs, providing insights into suspicious activities.
Related ISO 27001 Clauses: 10.1, 10.2.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.8.2
1. Access Control Management:
- Policy Templates and Pack: Establish clear policies using pre-built templates.
- Role-Based Access Control (RBAC): Simplify access management based on roles and responsibilities.
2. Authorisation and Approval Workflow:
- Workflow Automation: Streamline and document authorisation processes.
- Version Control and Document Access: Maintain comprehensive records of access rights changes and approvals, providing a clear audit trail for compliance verification.
3. Monitoring and Review:
- Risk Monitoring: Continually assess and adjust controls for privileged accounts.
- Incident Tracker: Document and manage incidents to improve response and future prevention.
4. Accountability and Tracking:
- Audit Management: Regularly review privileged access rights for compliance.
- Log Analysis and Reporting: Generate detailed activity reports, aiding in transparency and accountability.
Detailed Annex A.8.2 Compliance Checklist
Definition and Management:
- Conduct a comprehensive audit to identify all privileged accounts, including system and application-level accounts.
- Document all privileged accounts, detailing their access levels and associated roles.
- Clearly define roles that require privileged access, considering the sensitivity of data and organisational needs.
- Engage in cross-departmental collaboration to map roles to access requirements accurately.
- Implement and regularly review RBAC policies to ensure they align with current organisational structures and data sensitivity levels.
Authorisation and Approval:
- Establish and document a formal process for requesting and approving privileged access, including criteria and responsible approvers.
- Implement automated workflow systems to streamline the approval process and reduce delays.
- Ensure all approvals are based on standardised criteria, documented, and reviewed periodically for consistency.
- Use version control to maintain records of all changes to access rights and approvals.
Monitoring and Review:
- Schedule regular, risk-based reviews of privileged access rights, adjusting frequencies based on data sensitivity and potential impact.
- Utilise advanced monitoring tools to detect anomalies and unusual behaviour in privileged accounts.
- Document findings from reviews and implement necessary changes to mitigate identified risks.
- Continuously assess and update the risk profile associated with privileged accounts, ensuring controls remain effective.
Accountability and Tracking:
- Implement comprehensive and secure logging of all actions performed by privileged accounts, ensuring logs are protected from tampering.
- Use automated tools for analysing log data, identifying critical incidents, and generating reports.
- Conduct regular audits of privileged access logs to ensure compliance and uncover potential security weaknesses.
- Maintain an incident tracker for issues related to privileged access, documenting response actions and outcomes.
- Ensure that corrective actions are implemented, documented, and reviewed for effectiveness.
By addressing these aspects and leveraging ISMS.online features, organisations can ensure robust compliance with the A.8.2 Privileged Access Rights control, protecting sensitive information and maintaining operational integrity. This comprehensive approach not only meets regulatory requirements but also fosters a culture of security awareness and proactive risk management.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.8.2
Take the next step towards robust compliance and operational excellence.
Contact ISMS.online today to schedule a personalised demo. Our experts will showcase how our platform can seamlessly integrate into your existing systems, offering powerful tools for access control management, authorisation workflows, monitoring, and more.
Don’t wait—empower your organisation with the best in information security management. Book your demo now!