ISO 27001 A.8.23 Web Filtering Checklist
Annex A.8.23, Web Filtering, is a critical control within the ISO/IEC 27001:2022 framework. It aims to enhance an organisation’s information security by managing and controlling web traffic, ensuring that users are protected from accessing potentially harmful or inappropriate web content.
Effective implementation of web filtering not only mitigates risks such as malware and phishing attacks but also supports compliance with regulatory requirements, improves productivity, and optimises bandwidth usage.
Purpose of Annex A.8.23
The primary objective of web filtering is to regulate access to the internet by blocking access to specific websites or web-based services that may pose a security risk or be deemed inappropriate. This control helps to mitigate threats such as malware, phishing, and unauthorised data access, thereby protecting the organisation’s information assets.

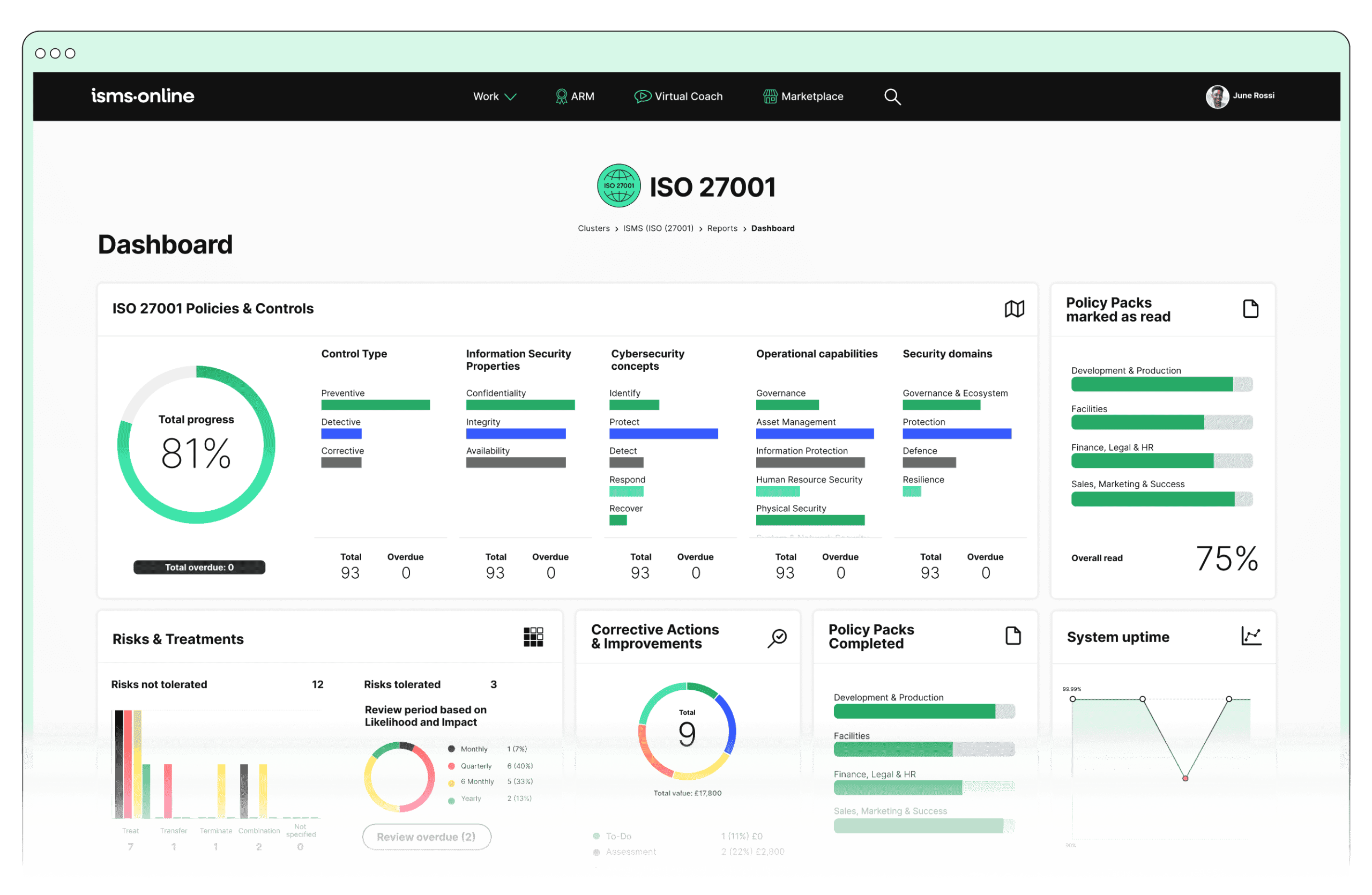
ISO 27001 made easy
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.8.23? Key Aspects and Common Challenges
1. URL Filtering:
- Definition: Restricting access to specific URLs or web addresses based on predefined criteria.
- Implementation: Utilise web filtering software or hardware solutions to create blacklists (blocked sites) and whitelists (approved sites).
- Benefit: Prevents users from accessing harmful or non-business-related websites.
- Overblocking: Risk of blocking legitimate websites, hindering productivity.
- Underblocking: Inadequate blocking of harmful sites due to constantly evolving threats.
- Solutions:
- Regularly review and update blacklist and whitelist entries to minimise the impact on productivity.
- Use machine learning algorithms to improve the accuracy of URL filtering and reduce underblocking.
- Associated ISO 27001 Clauses:
- Context of the Organisation: Understanding external and internal issues (Clause 4.1)
- Leadership and Commitment (Clause 5.1)
- Support: Communication (Clause 7.4)
Challenges:
2. Content Inspection:
- Definition: Analysing the content of web pages and downloads to detect and block malicious or inappropriate material.
- Implementation: Deploy content inspection tools that scan web traffic for viruses, malware, and other threats.
- Benefit: Reduces the risk of malware infections and data breaches.
- Performance Impact: Content inspection can slow down network performance.
- Encrypted Traffic: Difficulty in inspecting HTTPS traffic without appropriate tools.
- Solutions:
- Implement high-performance content inspection tools optimised for minimal impact on network speed.
- Use SSL/TLS decryption solutions to inspect encrypted traffic while ensuring privacy and compliance.
- Associated ISO 27001 Clauses:
- Risk Assessment and Treatment (Clause 6.1.2, 6.1.3)
- Performance Evaluation: Monitoring, measurement, analysis, and evaluation (Clause 9.1)
Challenges:
3. Malware Scanning:
- Definition: Scanning and blocking web content that contains malware.
- Implementation: Use antivirus and anti-malware solutions integrated with web filtering systems to scan web pages and downloads in real-time.
- Benefit: Enhances overall security by preventing the download and execution of malicious software.
- False Positives: Legitimate content being flagged as malware, causing disruptions.
- Update Frequency: Keeping malware definitions updated to combat new threats.
- Solutions:
- Employ advanced heuristic and behavioural analysis to reduce false positives.
- Ensure regular, automated updates of malware definitions and scanning engines.
- Associated ISO 27001 Clauses:
- Support: Resources (Clause 7.1)
- Support: Competence (Clause 7.2)
- Support: Awareness (Clause 7.3)
Challenges:
4. Policy Enforcement:
- Definition: Implementing and enforcing internet usage policies to ensure compliance with organisational standards.
- Implementation: Develop comprehensive web usage policies that define acceptable use of the internet and integrate these policies into the web filtering system.
- Benefit: Ensures consistent and secure internet use across the organisation.
- User Resistance: Employees may resist strict policies, impacting morale.
- Policy Complexity: Developing clear, enforceable policies that cover all scenarios.
- Solutions:
- Engage employees in policy development and provide clear communication and training on the importance of web filtering.
- Simplify policies where possible and ensure they are adaptable to different scenarios.
- Associated ISO 27001 Clauses:
- Leadership: Roles, responsibilities, and authorities (Clause 5.3)
- Support: Documented information (Clause 7.5)
- Operation: Operational planning and control (Clause 8.1)
Challenges:
5. Monitoring and Reporting:
- Definition: Continuously monitoring web traffic and generating reports to analyse usage patterns and detect security incidents.
- Implementation: Use web filtering tools that provide detailed logging and reporting features.
- Benefit: Enables proactive identification and mitigation of potential security issues.
- Data Overload: Managing and analysing large volumes of log data can be overwhelming.
- Privacy Concerns: Balancing monitoring needs with user privacy rights.
- Solutions:
- Implement advanced data analytics and automated reporting tools to manage and interpret large volumes of log data efficiently.
- Develop clear privacy policies and ensure transparency about monitoring practices to address privacy concerns.
- Associated ISO 27001 Clauses:
- Performance Evaluation: Internal audit (Clause 9.2)
- Performance Evaluation: Management review (Clause 9.3)
- Improvement: Nonconformity and corrective action (Clause 10.1)
Challenges:
Benefits of Web Filtering
- Enhanced Security: Protects against web-based threats such as malware, phishing, and ransomware.
- Compliance: Helps meet regulatory requirements related to internet usage and data protection.
- Productivity: Prevents access to non-business-related websites, thereby improving employee productivity.
- Bandwidth Management: Reduces unnecessary internet traffic, optimising bandwidth usage.
Annex A.8.23 Implementation Tips
- Regularly update blacklists and whitelists to reflect current threats and business needs.
- Ensure web filtering solutions are integrated with other security measures such as firewalls and intrusion detection systems.
- Conduct periodic reviews and audits of web filtering policies and practices to ensure effectiveness and compliance.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.8.23
1. Policy Management:
- Policy Templates & Policy Pack: Easily create and manage comprehensive internet usage policies that define acceptable use of web resources and integrate these policies with your web filtering solutions.
- Version Control & Document Access: Maintain up-to-date policy documents with controlled access and version tracking to ensure all stakeholders have the latest information.
2. Incident Management:
- Incident Tracker & Workflow: Track and manage web filtering-related incidents, such as attempts to access blocked sites or detected malware, using structured workflows to ensure timely response and resolution.
- Notifications & Reporting: Automate incident notifications and generate detailed reports on web filtering incidents to support continuous improvement and compliance efforts.
3. Risk Management:
- Dynamic Risk Map & Risk Monitoring: Identify and assess risks associated with web access and internet usage, updating the risk profile dynamically as new threats emerge. Monitor the effectiveness of web filtering controls continuously.
- Risk Bank: Maintain a repository of identified risks and associated mitigation strategies related to web filtering, ensuring comprehensive risk management.
4. Audit Management:
- Audit Templates & Audit Plan: Plan and execute audits specifically focused on web filtering controls, using predefined templates to ensure thorough evaluation and documentation.
- Corrective Actions & Documentation: Record audit findings and implement corrective actions to address any non-conformities related to web filtering, maintaining comprehensive documentation for future reference.
5. Compliance Management:
- Regs Database & Alert System: Stay informed about relevant regulations and standards affecting web filtering practices, ensuring timely updates to policies and controls.
- Training Modules: Provide targeted training to staff on the importance and proper use of web filtering tools and policies, enhancing overall awareness and compliance.
6. Communication:
- Alert System & Notification System: Keep stakeholders informed about web filtering policies, updates, and incidents through automated alerts and notifications.
- Collaboration Tools: Facilitate collaboration between IT, security teams, and management to ensure cohesive implementation and monitoring of web filtering controls.
By leveraging these ISMS.online features, organisations can effectively demonstrate compliance with Annex A.8.23 Web Filtering, ensuring robust security measures are in place to protect against web-based threats and enhance overall information security posture.
Detailed Annex A.8.23 Compliance Checklist
URL Filtering
- Implement a web filtering solution that supports blacklist and whitelist management.
- Regularly update blacklists and whitelists to reflect current threats.
- Review blocked sites list to ensure no legitimate sites are overblocked.
- Conduct regular testing to ensure harmful sites are adequately blocked.
Content Inspection
- Deploy content inspection tools to scan web traffic for viruses and malware.
- Ensure content inspection tools are capable of handling HTTPS traffic.
- Monitor network performance and adjust content inspection settings as needed.
- Regularly update inspection tools to handle new types of threats.
Malware Scanning
- Integrate antivirus and anti-malware solutions with web filtering systems.
- Schedule regular updates for malware definitions.
- Conduct periodic scans of web content to identify potential threats.
- Review and resolve false positives promptly to minimise disruptions.
Policy Enforcement
- Develop comprehensive internet usage policies.
- Integrate these policies with the web filtering system.
- Communicate policies clearly to all employees.
- Regularly review and update policies to reflect new security requirements.
Monitoring and Reporting
- Implement logging and reporting features within web filtering tools.
- Regularly review logs to identify unusual web traffic patterns.
- Generate and review reports on web filtering incidents.
- Balance monitoring needs with user privacy rights, ensuring compliance with privacy regulations.
By adhering to this compliance checklist, organisations can systematically address the key elements of web filtering, ensuring robust implementation and ongoing compliance with ISO/IEC 27001:2022 Annex A.8.23 Web Filtering.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.8.23
Ready to enhance your organisation’s information security and ensure compliance with ISO/IEC 27001:2022 Annex A.8.23 Web Filtering?
ISMS.online offers comprehensive solutions and expert guidance to help you implement effective web filtering controls seamlessly.
Don’t wait to protect your valuable information assets and improve your security posture.
Contact ISMS.online now to book a personalised demo and discover how our features can simplify your compliance journey and strengthen your cybersecurity defences.