ISO 27001 A.8.5 Secure Authentication Checklist
A.8.5 Secure Authentication in ISO 27001:2022 is a crucial control focused on establishing robust and secure authentication mechanisms within an organisation. This control is essential for protecting sensitive information and systems by ensuring that only authorised individuals, devices, and systems can access critical resources. Effective implementation of this control helps prevent unauthorised access and potential security breaches.
The key areas covered under A.8.5 include multi-factor authentication (MFA), secure password management, protection of authentication data, and session management. Implementing these measures is vital for safeguarding an organisation’s assets and ensuring compliance with ISO 27001:2022 standards.

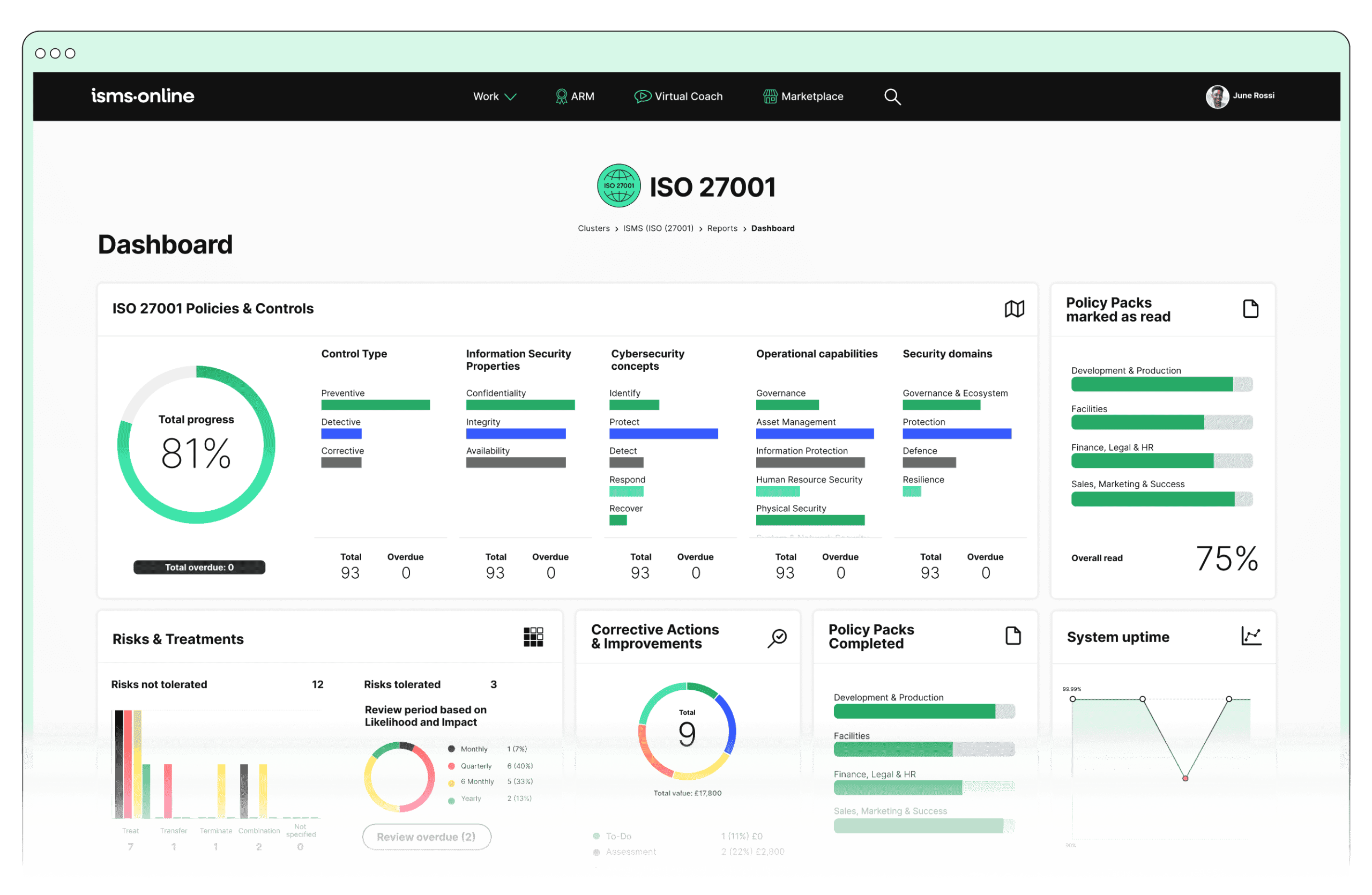
ISO 27001 made easy
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.8.5? Key Aspects and Common Challenges
1. Authentication Methods
Description: Strong authentication mechanisms, such as MFA, are employed to ensure that only authorised individuals can access critical systems and data.
Common Challenges:
- Integration Complexity: Implementing MFA across various systems can be technically challenging and resource-intensive.
- User Resistance: Users may perceive MFA as inconvenient, leading to resistance and non-compliance.
Solutions:
- Integration Planning and Support: Develop a detailed integration plan, including pilot testing and phased rollout to address compatibility issues and technical challenges. Example: Implement MFA in high-risk systems first, then gradually extend to all systems.
- User Education and Communication: Conduct comprehensive training and awareness campaigns to educate users on the importance of MFA and how it enhances security. Use case: Demonstrating how MFA can protect against common threats like phishing attacks.
- Support and Feedback Mechanisms: Establish a robust support system for users to report issues and provide feedback, ensuring continuous improvement in MFA implementation.
Associated ISO 27001:2022 Clauses: This step aligns with managing user identities and access rights, ensuring that authentication measures are robust and consistently applied.
2. Password Management
Description: This involves the development and enforcement of strong password policies, including complexity, expiration, and periodic changes.
Common Challenges:
- Balancing Security and Usability: Strong password policies may frustrate users if perceived as overly restrictive.
- Secure Storage and Transmission: Ensuring passwords are securely stored and transmitted to prevent unauthorised access.
Solutions:
- Policy Customisation: Tailor password policies to balance security and usability, such as using passphrases instead of complex passwords or allowing the use of password managers.
- Encryption and Secure Storage Solutions: Implement strong encryption methods for password storage and ensure secure channels for transmission. Practical example: Using bcrypt for hashing passwords.
- Regular Policy Review and Update: Regularly review and update password policies to align with evolving security threats and best practices.
Associated ISO 27001:2022 Clauses: Critical for access control and identity verification, ensuring secure management of user credentials.
3. Authentication Data Protection
Description: Protecting authentication credentials, such as passwords and tokens, through strong encryption and secure communication channels.
Common Challenges:
- Technical Demands: Implementing robust encryption and secure communication protocols can be technically demanding and resource-intensive.
- Ongoing Management: Continuous monitoring and updates are required to maintain protection measures.
Solutions:
- Encryption Standards: Adopt industry-standard encryption protocols (e.g., AES-256) for protecting authentication data both in storage and transmission.
- Secure Transmission Channels: Use secure protocols like HTTPS, TLS, and VPNs to protect data in transit. Example: Ensuring all web-based logins are protected with HTTPS.
- Continuous Monitoring and Audits: Regular audits of encryption and transmission methods to ensure they meet current security standards and are updated as needed.
Associated ISO 27001:2022 Clauses: Aligns with securing sensitive information and maintaining data integrity, ensuring comprehensive protection of authentication data.
4. Session Management
Description: Effective session management, including session timeouts and re-authentication, is crucial for limiting unauthorised access and maintaining security.
Common Challenges:
- Policy Implementation: Developing and enforcing consistent session management policies across different systems and user groups can be challenging.
- User Adaptation: Users may find session timeouts inconvenient, leading to potential non-compliance or attempts to bypass controls.
Solutions:
- Clear Policy Communication: Clearly communicate session management policies and the reasons behind them to users. Example: Highlighting the role of session timeouts in preventing unauthorised access due to unattended sessions.
- Customisable Session Settings: Allow flexibility in session settings based on user roles and risk levels, while maintaining overall security standards.
- Regular Policy Evaluation: Monitor the effectiveness of session management policies and make necessary adjustments based on user feedback and security assessments.
Associated ISO 27001:2022 Clauses: Session management policies are integral to maintaining secure access and user activity controls.

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.8.5
ISMS.online provides a comprehensive suite of tools designed to help organisations implement and demonstrate compliance with A.8.5 Secure Authentication:
- Policy Management: Facilitates the creation, communication, and enforcement of authentication policies, including MFA, password policies, and session management guidelines.
- Incident Management: Manages incidents related to authentication breaches, ensuring proper documentation and response measures.
- Audit Management: Supports planning and conducting regular audits of authentication mechanisms, ensuring compliance with ISO 27001:2022 standards.
- Training Modules: Provides extensive training on secure authentication practices, raising awareness and compliance across the organisation.
- Document Management: Centralises the management of policies and procedures related to secure authentication, ensuring they are up-to-date and consistently applied.
Detailed Annex A.8.5 Compliance Checklist
To ensure comprehensive compliance with A.8.5 Secure Authentication, organisations can use the following checklist:
1. Authentication Methods
- Implement Multi-Factor Authentication (MFA):
- Establish and document MFA policies and procedures.
- Deploy MFA across all critical systems, applications, and user accounts.
- Provide user training on MFA benefits and proper usage.
- Monitor and Review Authentication Methods:
- Conduct regular reviews of authentication methods for effectiveness.
- Update and refine authentication policies as necessary.
2. Password Management
- Develop and Enforce Password Policies:
- Define and communicate policies for password complexity, expiration, and change requirements.
- Ensure that all users are aware of and comply with these policies.
- Secure Password Storage and Transmission:
- Implement encryption for secure storage of passwords.
- Ensure secure transmission methods are in place for password data.
- Regular Password Audits:
- Schedule and conduct periodic audits of password management practices.
- Adjust password policies based on audit results and evolving security threats.
3. Authentication Data Protection
- Encrypt Authentication Data:
- Implement strong encryption for all stored authentication data.
- Use secure communication channels for transmitting authentication information.
- Document Protection Measures:
- Keep detailed records of encryption methods and security protocols.
- Regularly review and update these measures to reflect current best practices.
4. Session Management
- Implement Session Management Policies:
- Define policies for session timeouts and re-authentication.
- Apply these policies consistently across all systems and user roles.
- Monitor and Review Session Management:
- Regularly monitor user sessions to ensure compliance with session management policies.
- Conduct periodic reviews to assess the effectiveness of these policies and make necessary adjustments.
This comprehensive approach, supported by ISMS.online features, ensures that organisations not only implement but also maintain and demonstrate robust compliance with A.8.5 Secure Authentication requirements under ISO 27001:2022. This strategy helps in safeguarding critical systems and data, fostering a secure environment, and enhancing overall organisational resilience against security threats.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.8.5
Ensure your organisation meets the rigorous requirements of ISO 27001:2022 with the comprehensive tools and expertise offered by ISMS.online. Our platform provides everything you need to implement, manage, and demonstrate compliance with A.8.5 Secure Authentication and other critical controls.
Don’t leave your security to chance. Contact ISMS.online today to book a personalised demo and see how our integrated features can streamline your compliance journey, enhance security, and provide peace of mind.
Reach out to us now and take the first step towards a more secure and compliant future!