ISO 27001 A.8.6 Capacity Management Checklist
Capacity Management, as outlined in ISO 27001:2022 under control A.8.6, is a fundamental component of an organisation’s Information Security Management System (ISMS). This control ensures that IT infrastructure, systems, and services can handle both current and future operational demands, maintaining system performance and preventing disruptions.
Effective capacity management aligns with business continuity, strategic growth, and compliance objectives, optimising resource use and supporting long-term planning.

ISO 27001 made easy
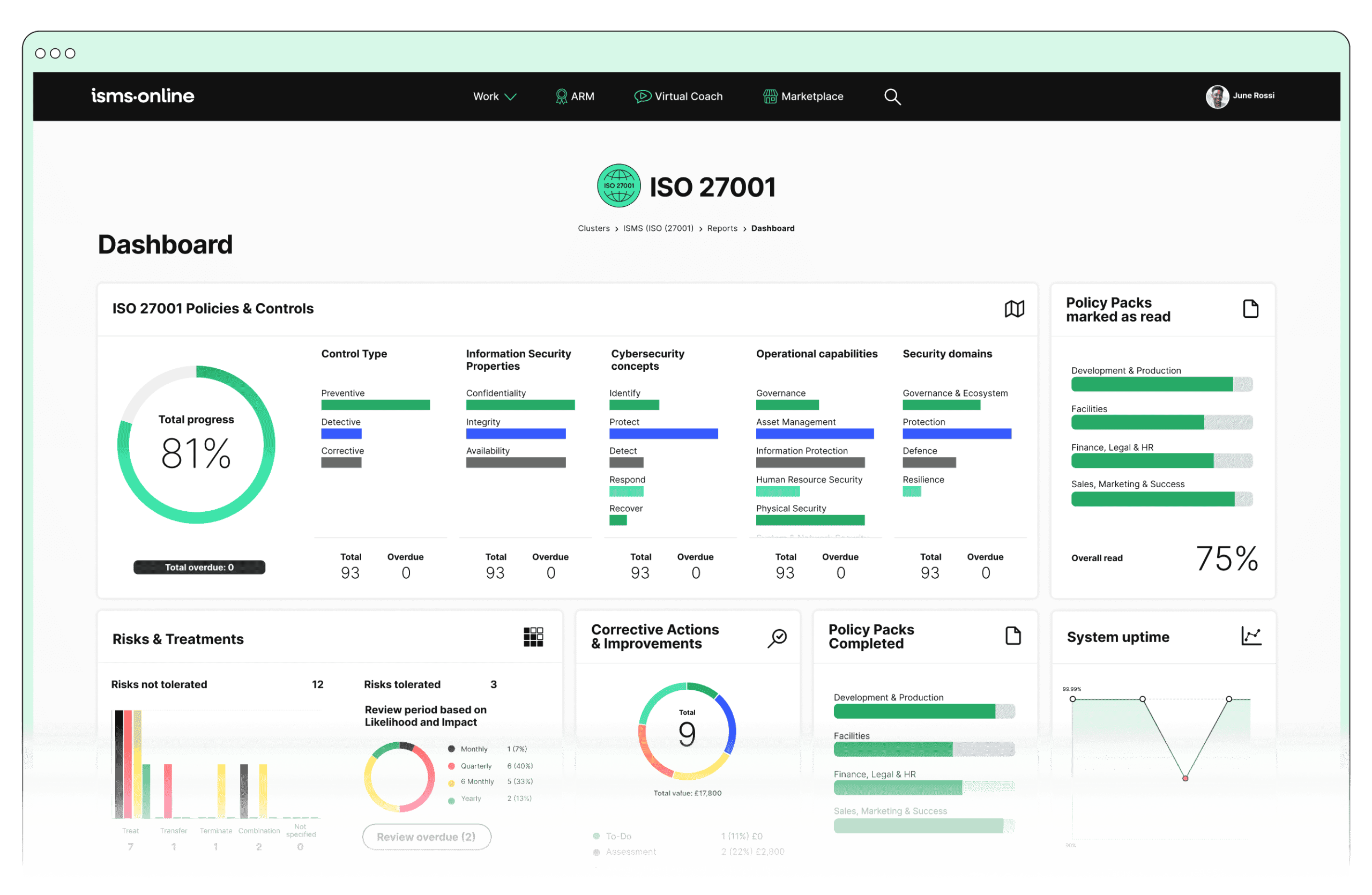
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Why Should You Comply With Annex A.8.6? Key Aspects and Common Challenges
1. Monitoring
Key Aspect: Continuous tracking of IT resources’ performance and utilisation, including servers, storage, networks, and applications.
Common Challenges:
- Data Overload: Managing vast data volumes from monitoring tools can overwhelm systems and staff.
- Integration: Difficulties in integrating diverse monitoring tools across various systems.
Solutions:
- Implement centralised dashboards to aggregate and filter key data, making it accessible and actionable.
- Use automated alert systems to notify relevant personnel of potential capacity issues.
- Standardise protocols and APIs for seamless integration of monitoring tools, enhancing system interoperability.
Related ISO 27001 Clauses: Regular monitoring and measurement (9.1), internal audit (9.2), management review (9.3).
2. Planning
Key Aspect: Forecasting future resource needs based on business growth, new projects, and technological advancements.
Common Challenges:
- Predictive Accuracy: Accurately forecasting capacity requirements amidst unpredictable changes.
- Budget Constraints: Balancing the need for future capacity with financial limitations.
Solutions:
- Utilise predictive analytics and historical data to enhance forecasting accuracy.
- Develop flexible budgeting models to accommodate varying capacity demands.
- Regularly review and adjust capacity plans based on real-time data and business priorities.
Related ISO 27001 Clauses: Risk assessment (6.1.2), risk treatment (6.1.3), objective setting (6.2).
3. Scalability
Key Aspect: Ensuring systems can scale efficiently to handle increased workloads.
Common Challenges:
- Legacy Systems: Older systems may not support easy scalability.
- Technical Debt: Accumulated technical debt can hinder scalability.
Solutions:
- Prioritise modernising legacy systems with scalable architectures, such as cloud-based or modular infrastructure.
- Implement phased approaches to reduce technical debt, focusing on critical areas.
- Leverage cloud computing for elastic scaling, allowing resources to adjust based on demand.
Related ISO 27001 Clauses: Change management (8.1), continual improvement (10.1), risk treatment plan (6.1.3).
4. Efficiency
Key Aspect: Optimising resource use to prevent both underutilisation and overprovisioning.
Common Challenges:
- Resource Optimisation: Balancing resource efficiency with redundancy needs.
- Changing Workloads: Adapting to dynamic and unpredictable workloads.
Solutions:
- Implement dynamic resource allocation strategies based on real-time demand.
- Use virtualisation and containerisation to maximise hardware utilisation and flexibility.
- Conduct regular efficiency audits to identify and eliminate waste, optimising resource allocation.
Related ISO 27001 Clauses: Operational planning and control (8.1), monitoring and measurement (9.1), continual improvement (10.1).

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

ISMS.online Features for Demonstrating Compliance with A.8.6
- Dynamic Risk Map: Visualises capacity-related risks, identifying bottlenecks and improvement areas.
- Resource Management Tools: Tracks and manages resource allocation, ensuring systems can meet current and future demands.
- Monitoring and Reporting: Offers detailed insights into resource utilisation and performance metrics.
- KPI Tracking: Measures the effectiveness of capacity management strategies and aligns them with business objectives.
- Continual Improvement: Regularly reviews and enhances practices, adapting to evolving needs and technological advancements.
Detailed Annex A.8.6 Compliance Checklist
To demonstrate compliance, follow this checklist:
Monitoring
- Implement and configure monitoring tools for all critical systems.
- Regularly review performance and resource utilisation reports.
- Establish clear thresholds and alerts for capacity issues.
- Integrate monitoring data into a centralised dashboard.
Planning
- Conduct regular capacity assessments.
- Develop a capacity management plan aligned with strategic goals.
- Include provisions for unexpected changes in the planning process.
- Allocate budget for future capacity needs.
Scalability
- Identify and document scalability challenges.
- Develop a roadmap for addressing scalability issues.
- Implement scalable solutions such as cloud-based services.
- Review and manage technical debt.
Efficiency
- Optimise resource utilisation.
- Implement redundancy and failover capabilities.
- Regularly review and adjust resource allocation.
- Conduct periodic efficiency audits.

Manage all your compliance, all in one place
ISMS.online supports over 100 standards and regulations, giving you a single platform for all your compliance needs.

Every Annex A Control Checklist Table
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.6.1 | Screening Checklist |
| Annex A.6.2 | Terms and Conditions of Employment Checklist |
| Annex A.6.3 | Information Security Awareness, Education and Training Checklist |
| Annex A.6.4 | Disciplinary Process Checklist |
| Annex A.6.5 | Responsibilities After Termination or Change of Employment Checklist |
| Annex A.6.6 | Confidentiality or Non-Disclosure Agreements Checklist |
| Annex A.6.7 | Remote Working Checklist |
| Annex A.6.8 | Information Security Event Reporting Checklist |
| ISO 27001 Control Number | ISO 27001 Control Checklist |
|---|---|
| Annex A.7.1 | Physical Security Perimeters Checklist |
| Annex A.7.2 | Physical Entry Checklist |
| Annex A.7.3 | Securing Offices, Rooms, and Facilities Checklist |
| Annex A.7.4 | Physical Security Monitoring Checklist |
| Annex A.7.5 | Protecting Against Physical and Environmental Threats Checklist |
| Annex A.7.6 | Working in Secure Areas Checklist |
| Annex A.7.7 | Clear Desk and Clear Screen Checklist |
| Annex A.7.8 | Equipment Siting and Protection Checklist |
| Annex A.7.9 | Security of Assets Off-Premises Checklist |
| Annex A.7.10 | Storage Media Checklist |
| Annex A.7.11 | Supporting Utilities Checklist |
| Annex A.7.12 | Cabling Security Checklist |
| Annex A.7.13 | Equipment Maintenance Checklist |
| Annex A.7.14 | Secure Disposal or Re-Use of Equipment Checklist |
How ISMS.online Help With A.8.6
Ready to elevate your capacity management and achieve ISO 27001:2022 compliance with ease?
ISMS.online offers a powerful, integrated platform designed to streamline your information security processes, including comprehensive tools for A.8.6 Capacity Management. Our solutions are tailored to help you overcome common challenges, optimise resource utilisation, and ensure your systems are always prepared to meet future demands.
Book a demo today to explore how ISMS.online can transform your information security management. Our experts will guide you through the platform’s features and demonstrate how it can be seamlessly integrated into your existing systems to enhance efficiency, scalability, and compliance.