Strengthening Network Security: Implementing ISO 27002 Control 8.20
Network security is a key component of an organisation’s broader information security policy.
Whilst several controls deal with individual elements of an organisation’s LAN and WAN setup, Control 8.20 is a series of broad protocols that deal with the concept of network security as a governing principle in all its various forms, and draws on guidance from several major information security controls across ISO 27002.
Purpose of Control 8.20
Control 8.20 is a dual-purpose preventive and detective control that maintains risk by implementing controls that safeguard an organisation’s ICT network from the top down, by ensuring that network activity is adequately logged, partitioned and carried out by authorised personnel.
Attributes Table of Control 8.20
| Control Type | Information Security Properties | Cybersecurity Concepts | Operational Capabilities | Security Domains |
|---|---|---|---|---|
| #Preventive | #Confidentiality | #Protect | #System and Network Security | #Protection |
| #Detective | #Integrity | #Detect | ||
| #Availability |

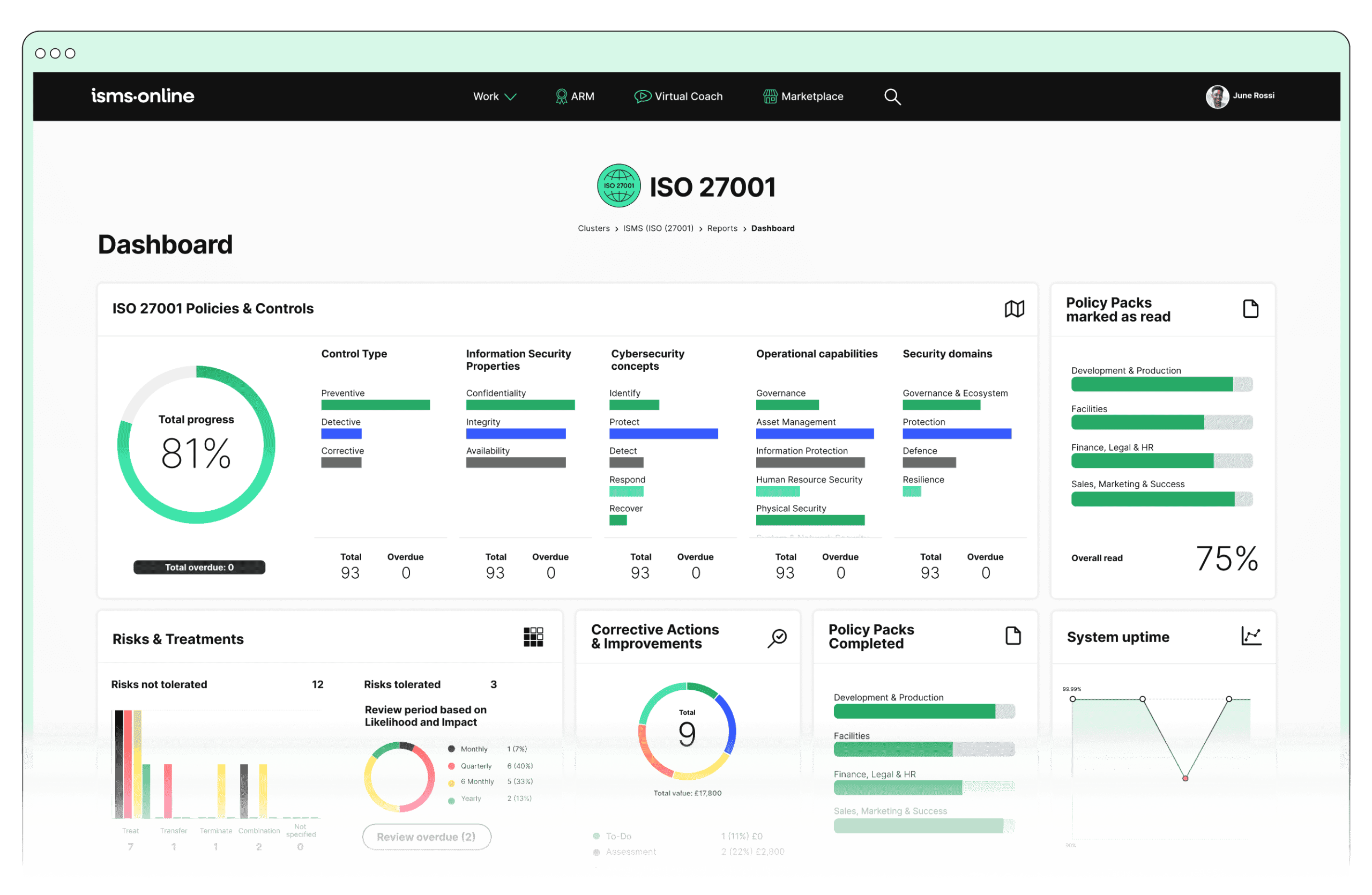
ISO 27001 made easy
An 81% Headstart from day one
We’ve done the hard work for you, giving you an 81% Headstart from the moment you log on. All you have to do is fill in the blanks.

Ownership of Control 8.20
Control 8.20 deals primarily with the operation of back-end networking, maintenance and diagnostic tools and procedures, but its broad scope encompasses far more than day-to-day maintenance operations. As such, ownership should reside with the organisation’s CISO, or equivalent.
General Guidance on Compliance
Control 8.20 focused on two key aspects of network security across all its general guidance points:
- Information security
- Protection from unauthorised access (particularly in the case of connected services)
To achieve these two goals, Control 8.20 asks organisations to do the following:
- Categorise information across a network by type and classification, for ease of management and maintenance.
- Ensure that networking equipment is maintained by personnel with documented job roles and responsibilities.
- Maintain up to date information (including version controlled documentation) on LAN and WAN network diagrams and firmware/configuration files of key network devices such as routers, firewalls, access points and network switches.
- Segregate responsibilities for an organisation’s network from standard ICT system and application operations (see Control 5.3), including the separation of administrative traffic from standard network traffic.
- Implement controls that facilitate the secure storage and transfer of data over all relevant networks (including third-party networks), and ensure the continued operation of all connected applications (see Controls 5.22, 8.24, 5.14 and 6.6).
- Log and monitor any and all actions that directly impact information security as a whole across the network, or within individual elements (see Controls 8.16 and 8.15).
- Coordinate network management duties to complement the organisation’s standard business processes.
- Ensure that all systems and relevant applications require authentication prior to operation.
- Filter traffic that flows through the network via a series of restrictions, content filtering guidelines and data rules.
- Ensure that all devices that connect to the network are visible, authentic and are able to be managed by ICT staff.
- Retain the ability to isolate business critical sub-networks in the event of a security incident.
- Suspend or disable network protocols that are either compromised or have become unstable or vulnerable.
Supporting Controls
- 5.14
- 5.22
- 5.3
- 6.6
- 8.15
- 8.16
- 8.24

Free yourself from a mountain of spreadsheets
Embed, expand and scale your compliance, without the mess. IO gives you the resilience and confidence to grow securely.

Changes and Differences from ISO 27002:2013
27002:2022-8.20 replaces 27002:2013-13.1.1 (Network controls).
27002:2022-8.20 advocates for a far more comprehensive approach to network security, and contains a number of additional guidance points that deal with several key elements of network security, including:
- Filtering traffic
- Suspending protocols
- Categorising network information
- Isolating sub-networks
- Maintaining visible devices
- Firmware records
New ISO 27002 Controls
| ISO/IEC 27002:2022 Control Identifier | ISO/IEC 27002:2013 Control Identifier | Control Name |
|---|---|---|
| 5.7 | NEW | Threat intelligence |
| 5.23 | NEW | Information security for use of cloud services |
| 5.30 | NEW | ICT readiness for business continuity |
| 7.4 | NEW | Physical security monitoring |
| 8.9 | NEW | Configuration management |
| 8.10 | NEW | Information deletion |
| 8.11 | NEW | Data masking |
| 8.12 | NEW | Data leakage prevention |
| 8.16 | NEW | Monitoring activities |
| 8.23 | NEW | Web filtering |
| 8.28 | NEW | Secure coding |
| ISO/IEC 27002:2022 Control Identifier | ISO/IEC 27002:2013 Control Identifier | Control Name |
|---|---|---|
| 6.1 | 07.1.1 | Screening |
| 6.2 | 07.1.2 | Terms and conditions of employment |
| 6.3 | 07.2.2 | Information security awareness, education and training |
| 6.4 | 07.2.3 | Disciplinary process |
| 6.5 | 07.3.1 | Responsibilities after termination or change of employment |
| 6.6 | 13.2.4 | Confidentiality or non-disclosure agreements |
| 6.7 | 06.2.2 | Remote working |
| 6.8 | 16.1.2, 16.1.3 | Information security event reporting |
| ISO/IEC 27002:2022 Control Identifier | ISO/IEC 27002:2013 Control Identifier | Control Name |
|---|---|---|
| 7.1 | 11.1.1 | Physical security perimeters |
| 7.2 | 11.1.2, 11.1.6 | Physical entry |
| 7.3 | 11.1.3 | Securing offices, rooms and facilities |
| 7.4 | NEW | Physical security monitoring |
| 7.5 | 11.1.4 | Protecting against physical and environmental threats |
| 7.6 | 11.1.5 | Working in secure areas |
| 7.7 | 11.2.9 | Clear desk and clear screen |
| 7.8 | 11.2.1 | Equipment siting and protection |
| 7.9 | 11.2.6 | Security of assets off-premises |
| 7.10 | 08.3.1, 08.3.2, 08.3.3, 11.2.5 | Storage media |
| 7.11 | 11.2.2 | Supporting utilities |
| 7.12 | 11.2.3 | Cabling security |
| 7.13 | 11.2.4 | Equipment maintenance |
| 7.14 | 11.2.7 | Secure disposal or re-use of equipment |
How ISMS.online Helps
The ISMS.Online platform helps with all aspects of implementing ISO 27002, from managing risk assessment activities through to developing policies, procedures and guidelines for complying with the standard’s requirements.
It provides a way to document your findings and communicate them with your team members online. ISMS.Online also allows you to create and save checklists for all of the tasks involved in implementing ISO 27002, so that you can easily track the progress of your organisation’s security program.
With its automated tool-set, ISMS.Online makes it easy for organisations to demonstrate compliance with the ISO 27002 standard.
Contact us today to schedule a demo.